If you’re a Windows user who intends to jailbreak with palera1n-c, and you have no intention of dual-booting Linux on your computer, then the palen1x project is pretty much your only option.
Check out the latest news and tutorials about checkm8, a hardware-based bootrom exploit for A7-A11 iPhones and iPads that can’t be patched by Apple, making it a popular choice for jailbreak tools.
If you’re a Windows user who intends to jailbreak with palera1n-c, and you have no intention of dual-booting Linux on your computer, then the palen1x project is pretty much your only option.
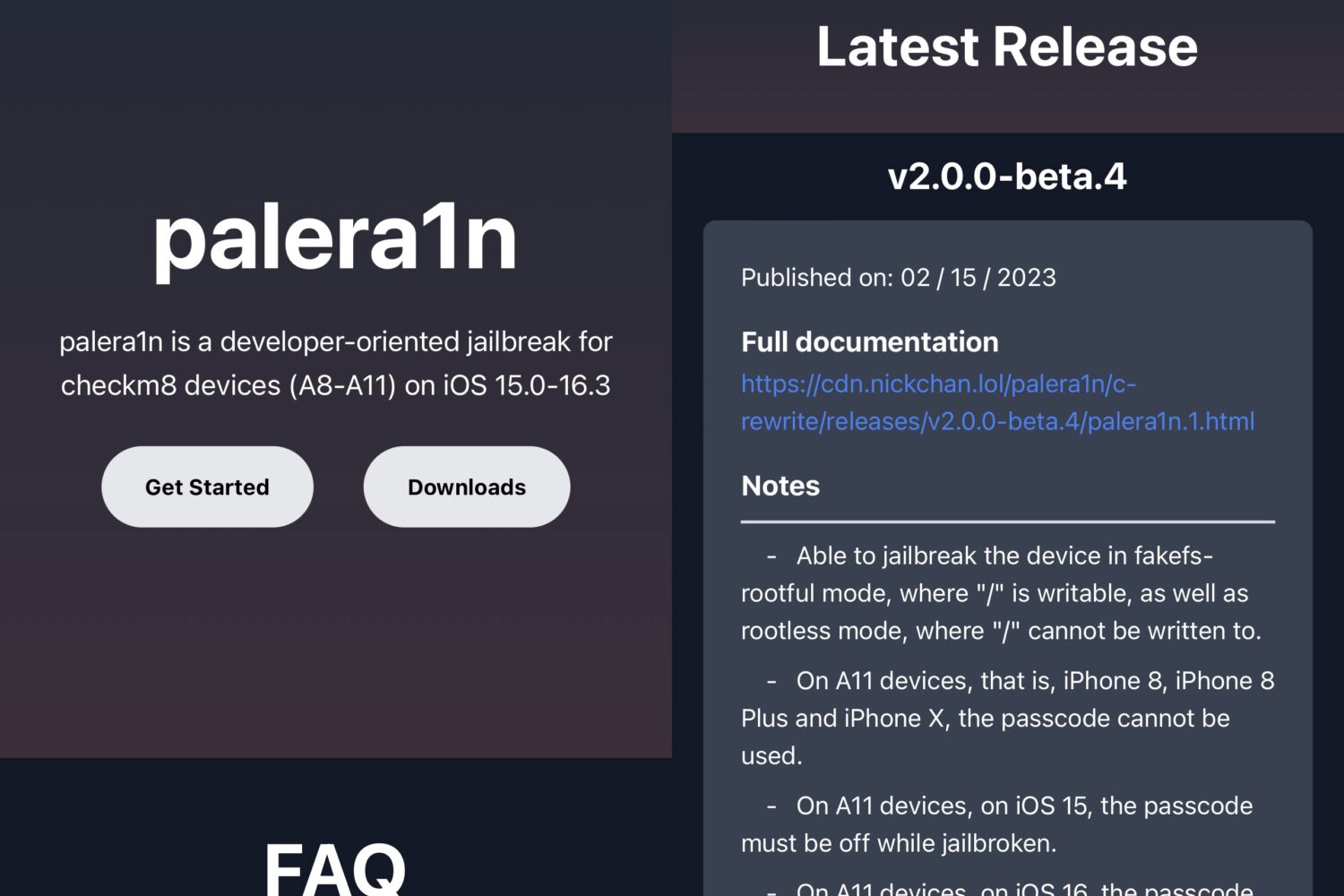
The palera1n jailbreak team made an important step toward making its jailbreak more user-friendly Friday afternoon after updating the official palera.in website to reflect the tool’s latest release(s) and automatically detect the user agent to make downloading the correct tool easier.
When it comes to jailbreaking A9-A11 chip-equipped iOS & iPadOS 15 or 16 devices, there’s no better tool out there than palera1n.
The palera1n team made a major announcement on Twitter Sunday afternoon regarding the checkm8 bootrom exploit-based palera1n jailbreak tool for A9-A11 chip-equipped devices running iOS 15.x-16.3.

If you’ve been paying any attention to the jailbreak community lately, then you’d be pretty hard-pressed to have never heard of palera1n. It's a pretty big deal these days.
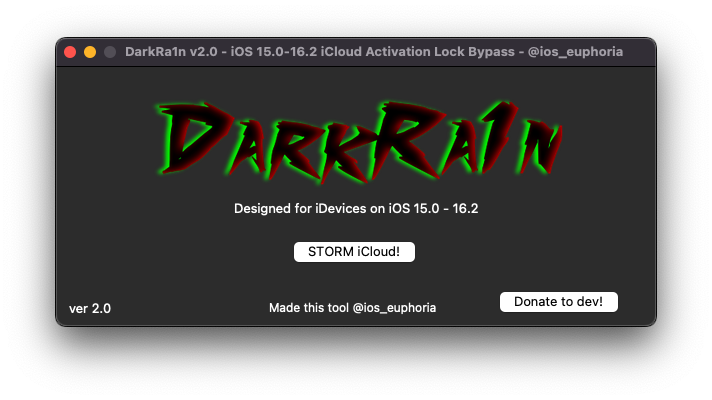
Apple’s iCloud Activation Lock feature prevents unauthorized users from acquiring your device, restoring it as new, and using it as their own. Unfortunately, users can be locked out of their own device by this feature after forgetting a password or buying an iCloud locked device from the internet.

The palera1n team this week released version 1.4.1 of its checkm8 bootrom exploit-based jailbreak tool for A9-A11 chip-equipped handsets running iOS or iPadOS 15.0-16.x, all while one team member demonstrated the tool’s upcoming and previously-teased GUI (graphical user interface).

As expected, following the announcement that tfp0 (kernel task port) had been achieved on an iOS 16.1.1 device, the palera1n team has officially added support for iOS & iPadOS 16 to its checkm8 bootrom exploit-based palera1n jailbreak tool in version 1.4.0.

If after trying the palera1n jailbreak you’ve decided that it isn’t right for you, then you might be wondering what you can do to remove it from your device.
The palera1n team appears to be looking into the possibility of adding iOS & iPadOS 16 support to its checkm8 bootrom exploit-based palera1n jailbreak tool for A9-A11 devices.

The palera1n jailbreak, albeit intended for developers more-so than the general public, remains one of the only publicly available jailbreaks supporting iOS & iPadOS 15.x. But as more users turn to the newer iOS & iPadOS 16 for the newer features, it only seems appropriate to mention that palera1n co-developer @itsnebulalol has teased successful tweak injection and kernel memory read and write capabilities on a physical iOS 16 device.

In case you’ve been living under a rock, there’s a checkm8 bootrom exploit-based jailbreak out there for A9-A11 devices running iOS or iPadOS 15.0-16.x called palera1n. While palera1n is primarily intended for developers, it also has the strongest foothold in the iOS & iPadOS 15 community out of any jailbreak as of this moment.
Note: The legacy palera1n jailbreak is now deprecated. Use the newer palera1n-c tool instead.