Ever since the unc0ver team issued a DMCA take down request for the Odyssey jailbreak GitHub page, many avid jailbreakers have been waiting for the smoke to clear. At this time, the investigation is still pending, and no official verdict has been declared. Odyssey lead developer CoolStar did, however, respond to the DMCA take down with an appeal. Now we wait to see what happens...
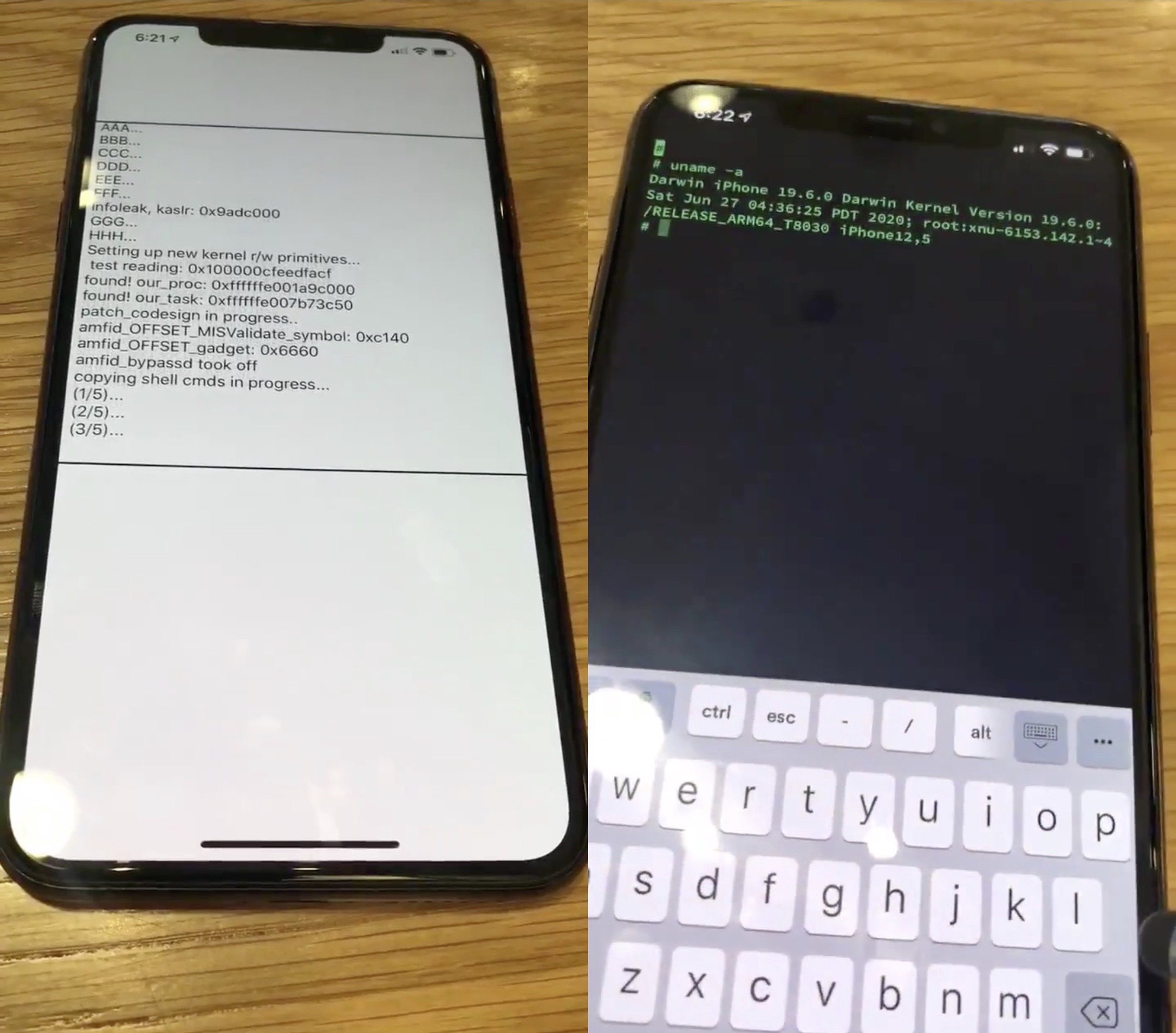
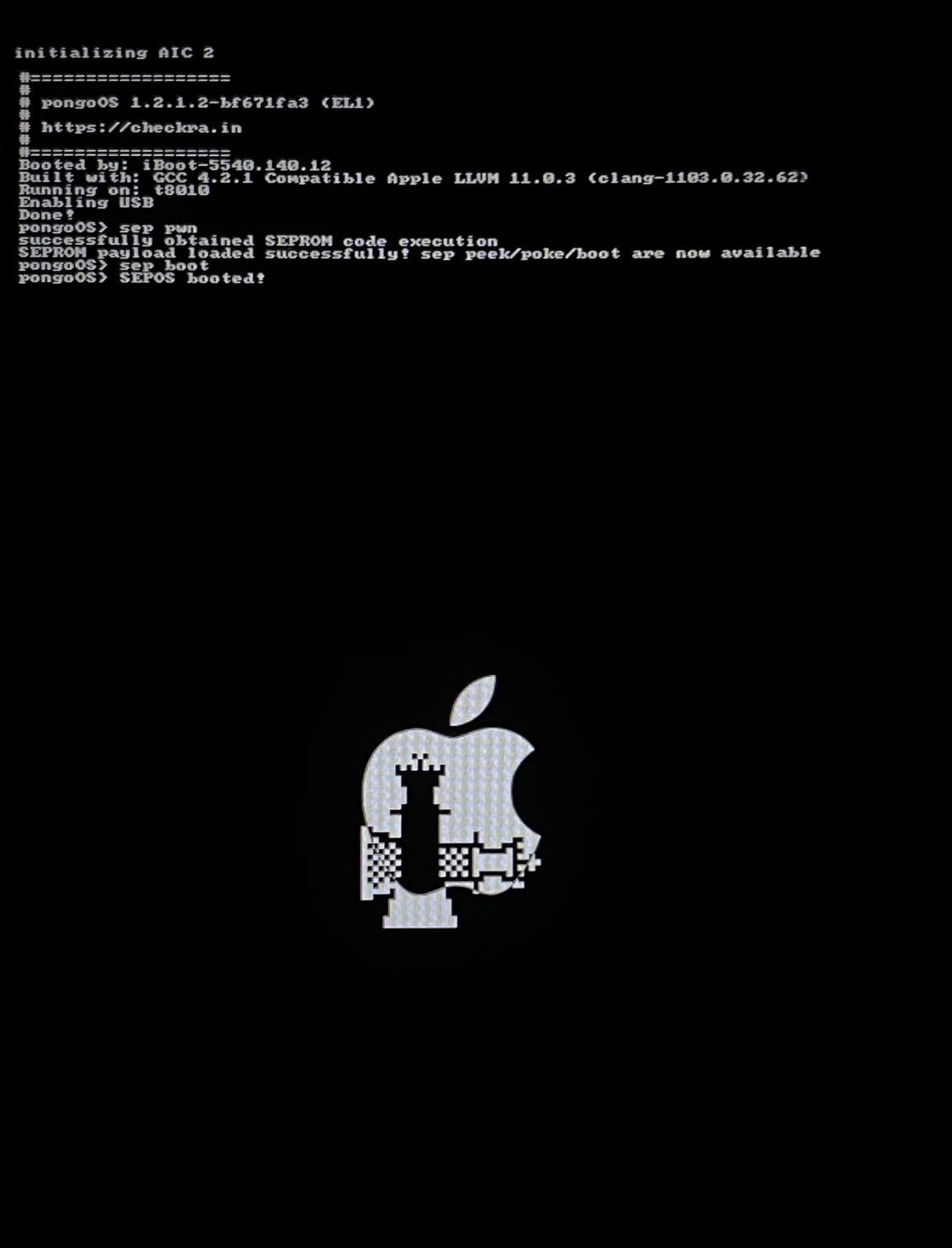
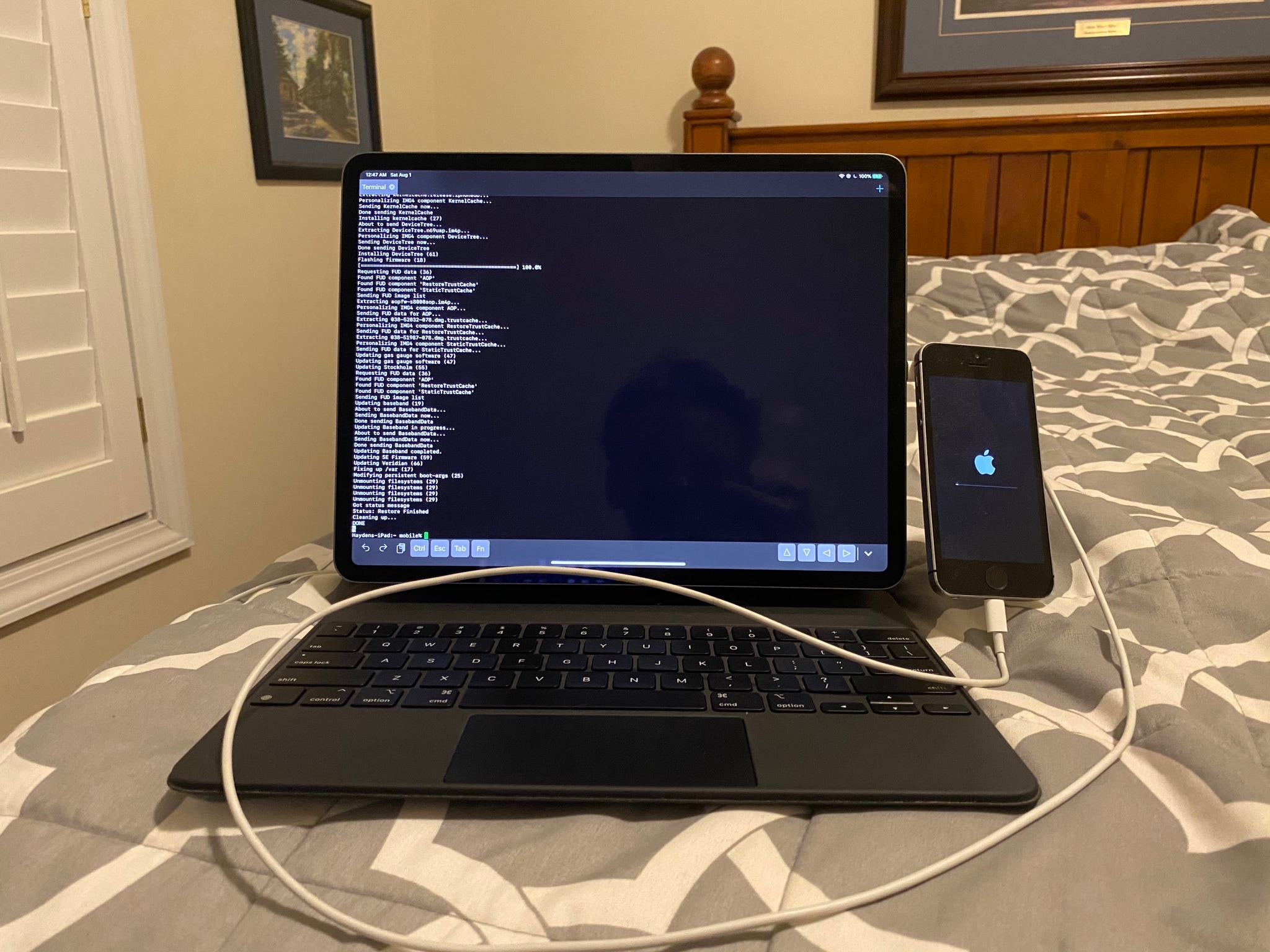
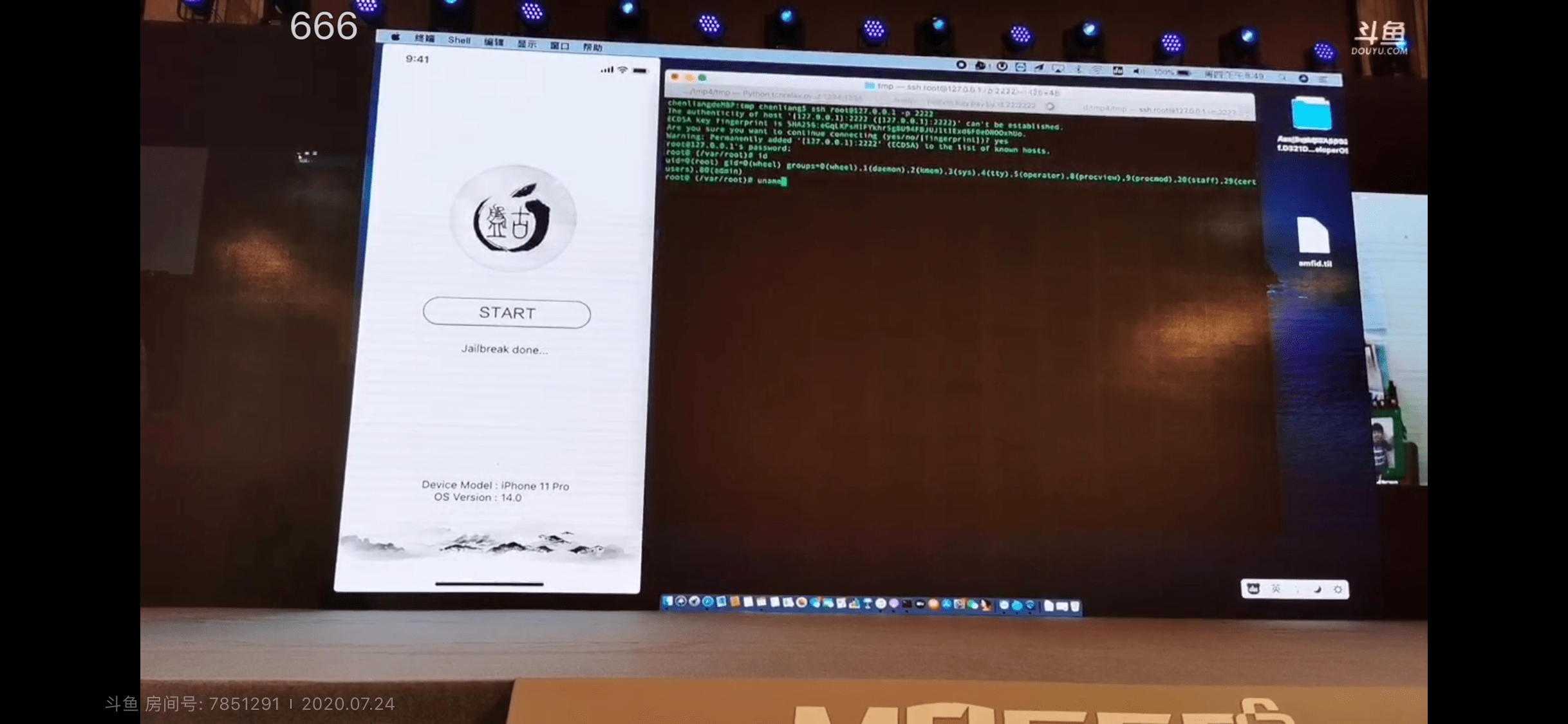
In the meantime, those avidly waiting for the Odyssey jailbreak to launch have been forced to wait longer than expected to download and use the tool. CoolStar’s most recently ETA for release is ‘whenever GitHub restores the repository,’ but things took an interesting turn early Sunday morning when CoolStar Tweeted a link encompassing what appears to be a beta pre-release version of the Odyssey jailbreak tool: