
You should be extra careful about the shortcuts you download because some of these iOS automation scripts were created by ill-minded people for malicious purposes.
Case in point: Codea developer Simeon has stumbled upon a malicious shortcut disguised to appear to the user as an innocent RAM optimizer and cleaner (via iGen.fr).
In reality, it collects personal data like contacts, addresses, files on your device and what not. This stuff is silently archived in a ZIP file that gets sent via an iMessage to an attacker.
https://twitter.com/twolivesleft/status/1088080309453676544
That particular shortcut was able to get away with this because the details of what it was doing were obfuscated through base64 encoding. “I’ve disclosed all the details to Apple and hope that they fix it, but the more Shortcuts becomes mainstream, the more people need to be aware of how they can be powerfully misused,” he wrote on Twitter.

Aside from the fact that no one should ever bother using an app or a shortcut that promises to clean your memory (iOS does a far better job managing the RAM than any app could), it’s unclear what an average user could do in order to avoid malicious shortcuts.
TUTORIAL: How to share iCloud Drive files
The problem with shortcuts is Apple’s powerful scripting language they employ, allowing users to chain multiple repetitive tasks into a single action. Apple does not host user-created shortcuts so they’re certainly not being screened or scrutinized in detail like App Store apps.
Typically, a user-created shortcut is shared via an iCloud file link.

And therein lies the problem. “You couldn’t expect a reasonable user to know what they were agreeing to run when receiving an Apple-hosted link to a shortcut,” Simeon said.
Apple could alleviate this issue by requiring that all shortcuts be hosted by App Store so that any submissions from the community could be screened by its review team.
It could also introduce new types of protective measures like we saw in macOS Mojave to forbid shortcuts to access low-level functions, such the file system, or at least throw a prompt when a shortcut wants to mess with your data.
In Mojave, users must give their permission when an app or a script wants to control other apps (System Preferences → Security & Privacy → Privacy → Automation).
It would be nice to have similar options in iOS.
iGen also proposed additional measures, like checking a shortcut’s authenticity by taking a closer look at what it really does in the Shortcuts app (tap Show Actions).
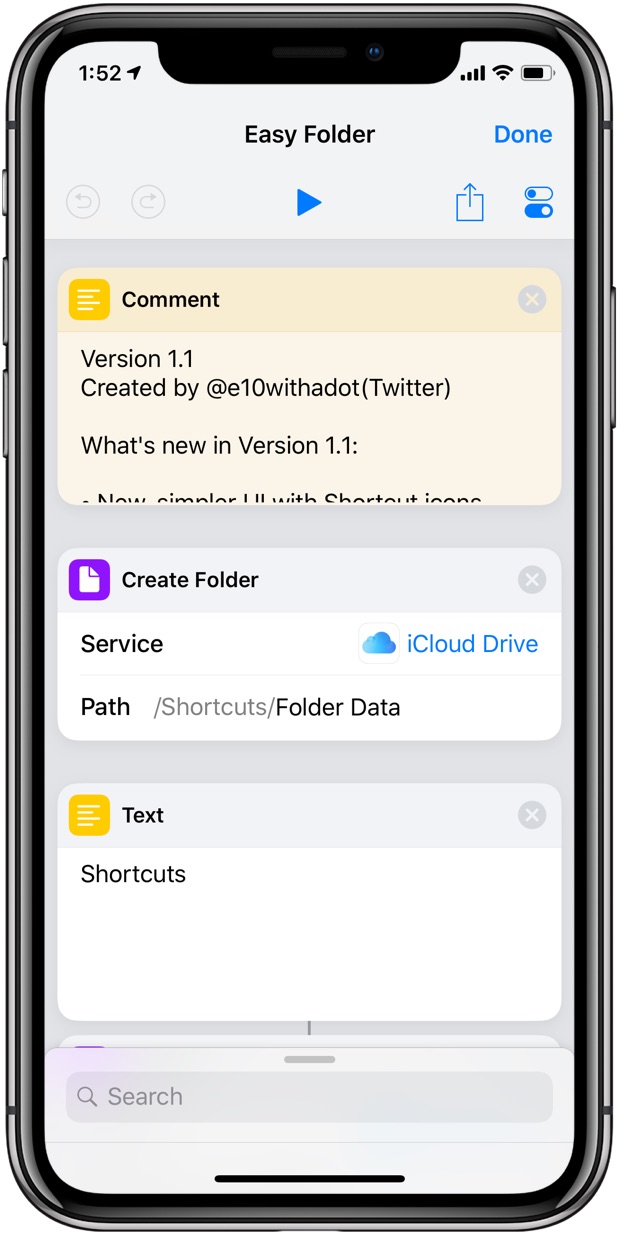
For instance, if a shortcut that’s supposed to crop images suddenly requests access to Messages, this should raise red flags. Additionally, iGen cautions people against downloading shortcuts from people or websites they don’t trust.
The Apple-hosted gallery of scripts available in the Shortcuts app is a trusted source for sure, but what about all those iCloud-hosted, community-created scripts that you may stumble upon on Reddit and social media?
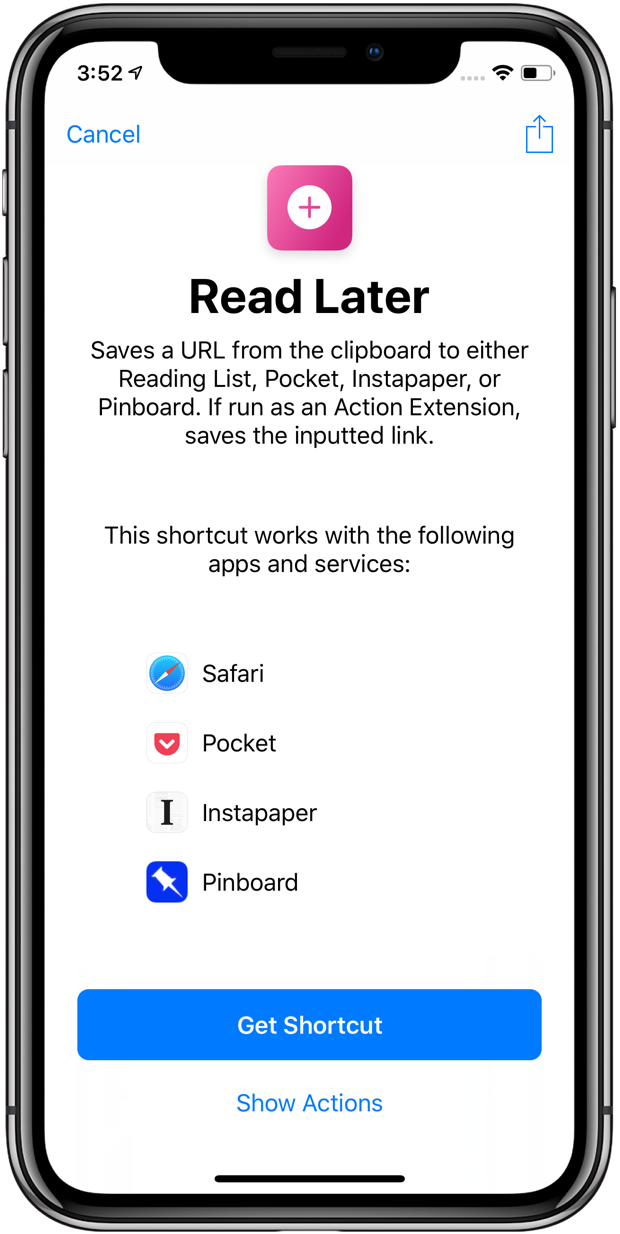
iGeneration advises checking a shortcut against a list of shortcuts from people who are well-known in the Apple community. One such list is hosted on the Sharecuts website.
You should also check out the ShortcutsGallery website, as well as browse iDownloadBlog’s collection of the best community scripts in our Shortcuts Focus archive.
Be sure to verify the shortcuts you download via the Sharecuts website.
Summing up, anyone can create, host and share their own shortcuts and package them as anything they like (i.e. “Clear Screenshots from Photos”, “Performance Optimizer” and so forth) without any repercussions.
With that in mind, being less trusting of any community-created shortcuts you download goes a long way in addressing these privacy and security concerns dealing with iOS automation.
Do you use shortcuts on your iOS device?
If so, how would you solve the trust issue if you were Apple?
Feel free to chime in with your thoughts in the comments.