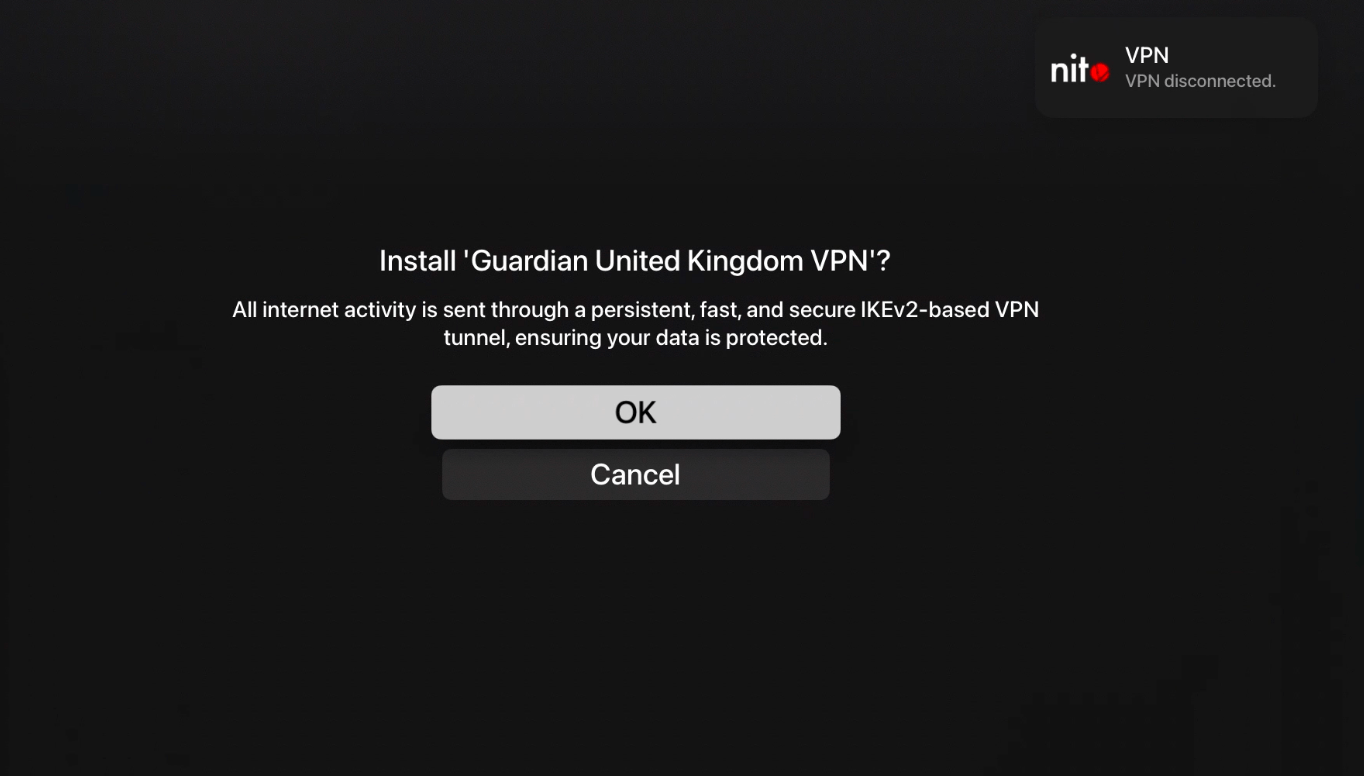
About a month ago, Guardian Firewall VPN founder and CEO Will Strafach, a former member of the Chronic Dev Team, shared a particularly exciting announcement in that nitoTV (now going by @freenitoTV on Twitter) had gotten VPN connections working on the Apple TV platform for the very first time; albeit with a jailbreak.
The aforementioned jaw-dropping feat demanded tons of complicated hackery, but after lots of research, development, testing, and refinement, the project, officially dubbed “vpnd,” is now available for jailbreakers who might want to try their hand at configuring a VPN connection on their own Apple TV.