Recently, more tidbits about forthcoming Apple products have been coming from its offices in Cupertino, California, than from the company's vast supply chain in Asia.
That's according to Outline's William Turton, who has watched a video of an hour-long briefing held by former NSA investigators in order to educate about 100 top Apple employees on how confidential information gets leaked out to the press.
Titled “Stopping Leakers—Keeping Confidential at Apple,” the presentation was led by Apple's Director of Global Security David Rice, Director of Worldwide Investigations Lee Freedman and Jenny Hubbert, who works on Apple's Global Security communications and training team.
The presentation educated employees on the ways to “prevent information from reaching competitors, counterfeiters and the press.” Apple’s Global Security team employs an undisclosed number of investigators around the world, with some members embedded on certain Apple product teams to help employees keep secrets.
“When I see a leak in the press, for me, it’s gut-wrenching,” one Apple employee said. “It really makes me sick to my stomach.” Another employee said that when an Apple employee does leak confidential information, they're “letting all of us down.”
“It’s our company, the reputation of the company, the hard work of the different teams that work on this stuff,” said the employee. Tim Cook publicly promised in 2012 that Apple would double-down on secrecy. So, how has that worked out?
According to Greg Joswiak, Apple’s Vice President of iOS product marketing:
This has become a big deal for Tim. Matter of fact, it should be important to literally everybody at Apple that we can't tolerate this any longer. I have faith deep in my soul that if we hire smart people they’re gonna think about this, they’re gonna understand this, and ultimately they’re gonna do the right thing and that’s to keep their mouth shut.
Apple is actively going after leakers who would spoil its “One More Thing” surprises.
According to Jenny Hubbert:
So you heard Tim say, ‘We have one more thing.’ So what is that one more thing? Surprise and delight. Surprise and delight when we announce a product to the world that hasn’t leaked. It’s incredibly impactful, in a really positive way. It’s our DNA. It’s our brand. But when leaks get out, that’s even more impactful. It’s a direct hit to all of us.
In recent months, Apple clamped down on supply chain leaks, so much so that more confidential information now gets leaked out from Apple’s campuses in California than its factories abroad.
“Last year was the first year that Apple campuses leaked more than the supply chain,” Rice told the gathered employees. “More stuff came out of Apple campuses last year than all of our supply chain combined.”
This is a notable achievement given that Apple's contract manufacturers employ up to three million people when the company ramps up production, and all of these people need to be checked every time they enter and exit the factory.
The iPhone maker has been “busting its ass” to prevent supply chain leaks, with Rice describing the efforts as “trench warfare non-stop,” especially with “very talented adversaries” and black market sellers offering “top dollar” for Apple parts.
A product's housing is the most sough-after part. “If you have a housing, you pretty much know what we're going to ship,” Rice says, adding that the stolen parts often end up in Huaqiangbei, one of the biggest electronics markets in the world, located in Shenzhen, Southern China.
“There’s a whole slew of folks that can be tempted because what happens if I offer you, say, three months’ salary?’ In some cases we’ve seen up to a year’s worth of salary being rewarded for stealing product out of the factory,” said Rice.
2013 was a particularly painful year for Apple as the company had to buy back about 19,000 stolen enclosures before the iPhone 5c announcement and then an additional 11,000 before the phones were shipped to customers. “So we're buying as fast as we possibly can to try to keep it out of every blog on Earth,” Rice said.
Here's how many Apple enclosures were stolen since 2013:
2014—387 enclosures stolen
2015—57 enclosures stolen, 50 of which were lifted on the announcement night
2016—4 enclosures stolen
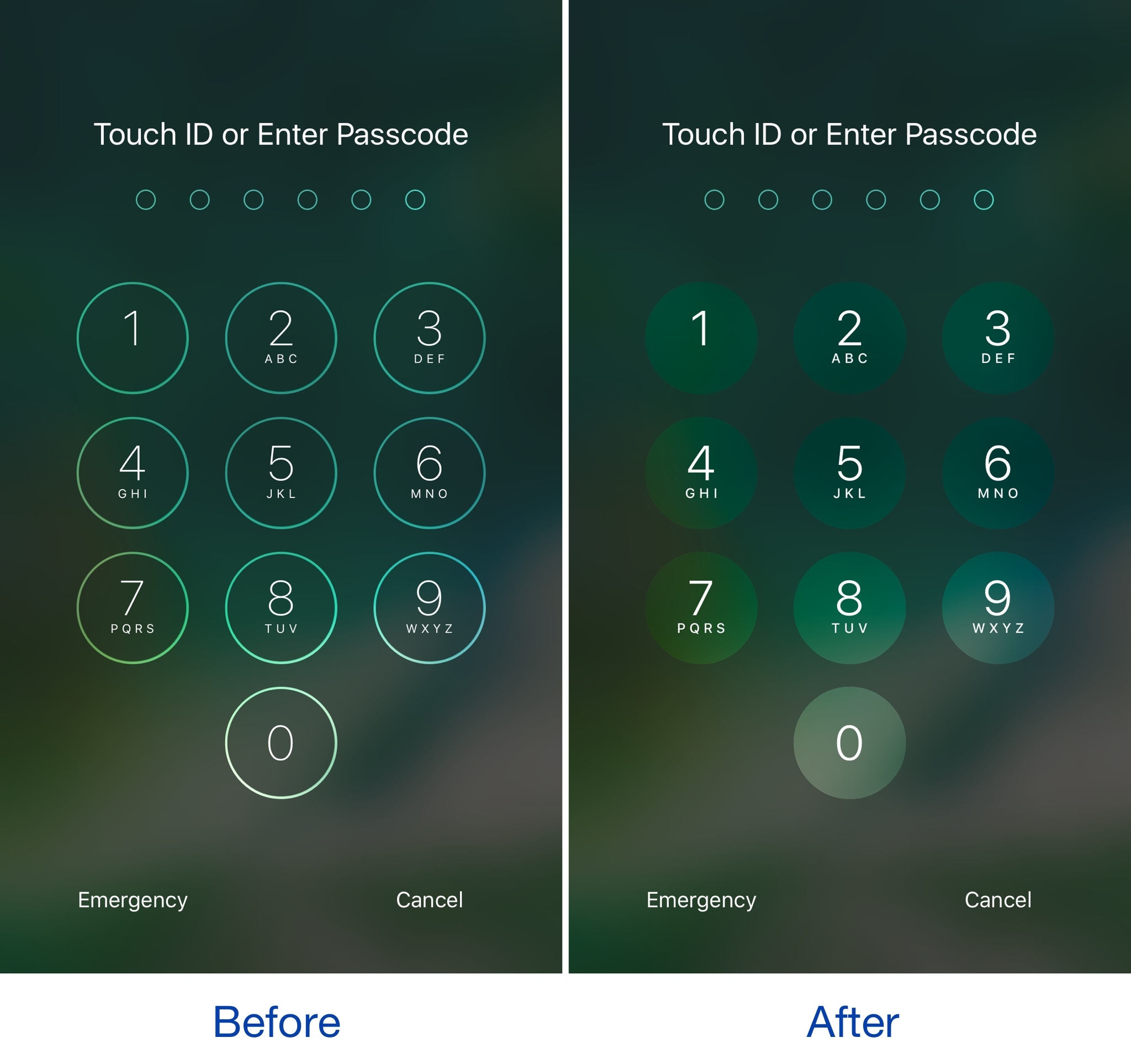
A few years ago, Apple began removing traces of unreleased products from iOS builds.
Its renewed focus on preventing leaks is on full display with virtually no iPhone 8 component leaks as of yet, unlike in years past when new iPhone parts would leak out of Asian factories for months in advance.
Not even Bloomberg's Mark Gurman, formerly with 9to5Mac, could obtain iPhone 8 parts. Rice “gleefully recounted” a blog post by Daring Fireball's John Gruber, in which he criticized Gurman for not having details on Apple’s new HomePod speaker before it was released.
Like many other manufacturers, Apple has long been using special cases to conceal iPhone prototypes during testing in the wild. Still, no security is perfect so leaks remain a fact of life. Security always comes down to the human factor, as we saw with the iPhone 4 leak.
For an in-depth overview of Apple's commitment to corporate secrecy, I wholeheartedly recommend Adam Lashinksy’s book “Inside Apple”, available on iBooks Store for $14.99.