Apps designed to use iCloud Drive for syncing data between devices “just work”. On the other hand, those that don’t natively support Apple's secure Two-Factor Authentication system may ask for your Apple ID password to access data stored in your iCloud account.
For instance, Fantastical for Mac may require your Apple ID user name and password to import your iCloud calendars. And what if you'd like to use your iCloud email account in apps like Spark or Airmail, but don't want to expose your Apple ID credentials to the app?
Given that asking for the user's iCloud password poses a dangerous attack vector, Apple now mandates that all native apps use app-specific passwords to access user data stored in iCloud.
The change goes into effect on June 15, 2017.
To ensure worry-free experience, you can use an app-specific password to sign in to an app or service not provided by Apple, without ever typing your Apple ID password.
In this step-by-step tutorial, you will learn how to create an app-specific password for any native app that wants to access your personal data stored in iCloud, revoke all of your generated passwords one by one or all at once, and more.
About app-specific passwordsSecurity is paramount.
Protecting your Apple ID account against hackers and nefarious users by turning on Apple's older Two-Step Verification system or the modern, more secure Two-Step Verification also entails using app-specific passwords for any web apps, online services and apps that don’t natively support entering verification codes.
TUTORIAL: How to protect your Apple ID with Two-Factor Authentication
App-specific passwords maintain “a high level of security and ensure that your primary Apple ID password won’t be collected or stored by any third-party apps you might use,” notes Apple.
You can have up to 25 active app-specific passwords at any given time. If you need to, you can revoke passwords individually or all at once.
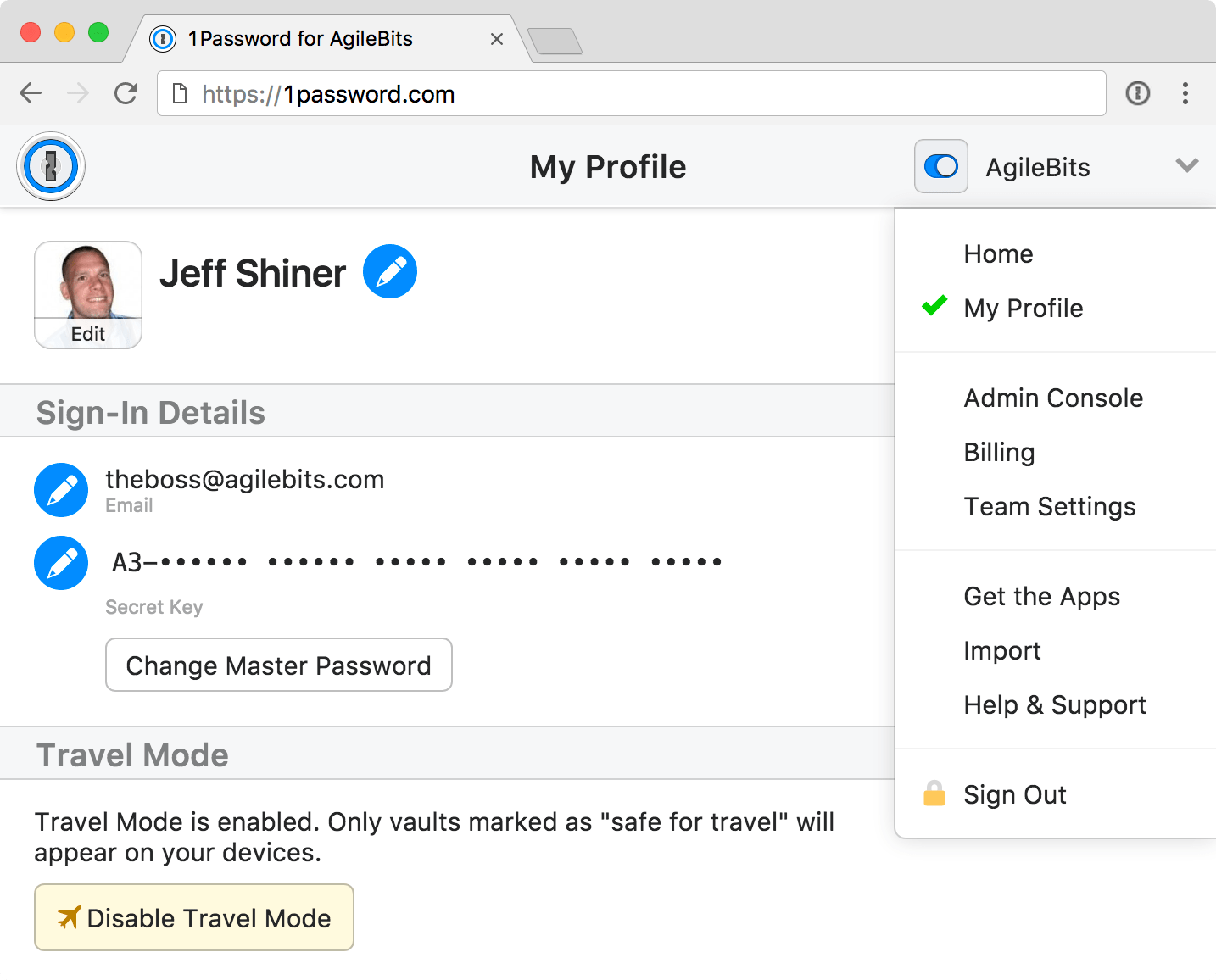
How to generate app-specific passwords1) Sign in to your Apple ID account page at appleid.apple.com/account/home.
2) In the Security section, click Generate Password below App-Specific Passwords.
3) Type a password label into the text field, then click Create to generate a random password. The password label helps distinguish one app-specific password from another.
I'll create an app-specific password for Fantastical and name it “Fantastical for Mac”.
4) Click Done to finish creating the password.
5) Now paste the password into the password field of the app as you would normally.
Again, I'm a Fantastical believer so I'm going to type the generated password into Fantastical.
Using an app-specific password ensures that Fantastical is able to access my iCloud calendar and gives me a piece of mind knowing I don't have to worry about the security of my Apple ID.
As a reminder, you can have up to 25 active app-specific passwords at any given time. Keep in mind that each app-specific password is case-sensitive and only works in one app.
How to revoke app-specific passwordsYou can revoke app-specific passwords individually or all at once. Revoking an app-specific password stops the app from accessing data in your iCloud account.
1) Sign in to your Apple ID account page at appleid.apple.com/account/home.
2) In the Security section, click Edit.
3) In the App Specific Passwords section, click View History.
4) You can now revoke an individual password or all passwords at once:
Revoke individual passwords—To revoke an individual password, click the “x” next to a password you'd like to delete, then click Revoke. Revoke all passwords at once—To revoke all the app-specific passwords you've generated thus far, click Revoke All.“After you revoke a password, the app using that password will be signed out of your account until you generate a new password and sign in again,” notes Apple.
Be sure to generate new app-specific passwords for any apps that don't support entering verification codes because, for the sake of your own security, all of your app-specific passwords are auto-revoked any time you update or reset your primary Apple ID password.
Need help? Ask iDB!If you like this how-to, pass it along to your support folks and leave a comment below.
Got stuck? Not sure how to do certain things on your Apple device? Let us know at help@iDownloadBlog.com and a future tutorial might provide a solution.
Submit your how-to suggestions via tips@iDownloadBlog.com.