As part of his summer project, NYU grad student Dejian Zeng spent six weeks working undercover in a Chinese factory operated by iPhone manufacturer Pegatron. In a video interview with Business Insider's Kif Leswing, he reveals some of the security measures designed to prevent unwanted leaks as part of preparations ahead of iPhone 7 production.
Here's an interesting excerpt from the interview:
In the workshop, we were originally producing iPhone 6s and during that time that we were in the workshop they were already building up some facilities or infrastructure to build the assembly line for iPhone 7.
And they had this big curtain that blocked everything.
While we were in the same workshop, we saw nothing. And later on, we were moved to another sub-factory building to do work there for a while, because they need to rebuild the assembly line that we are working on also.
The following points from the interview stood out for me:
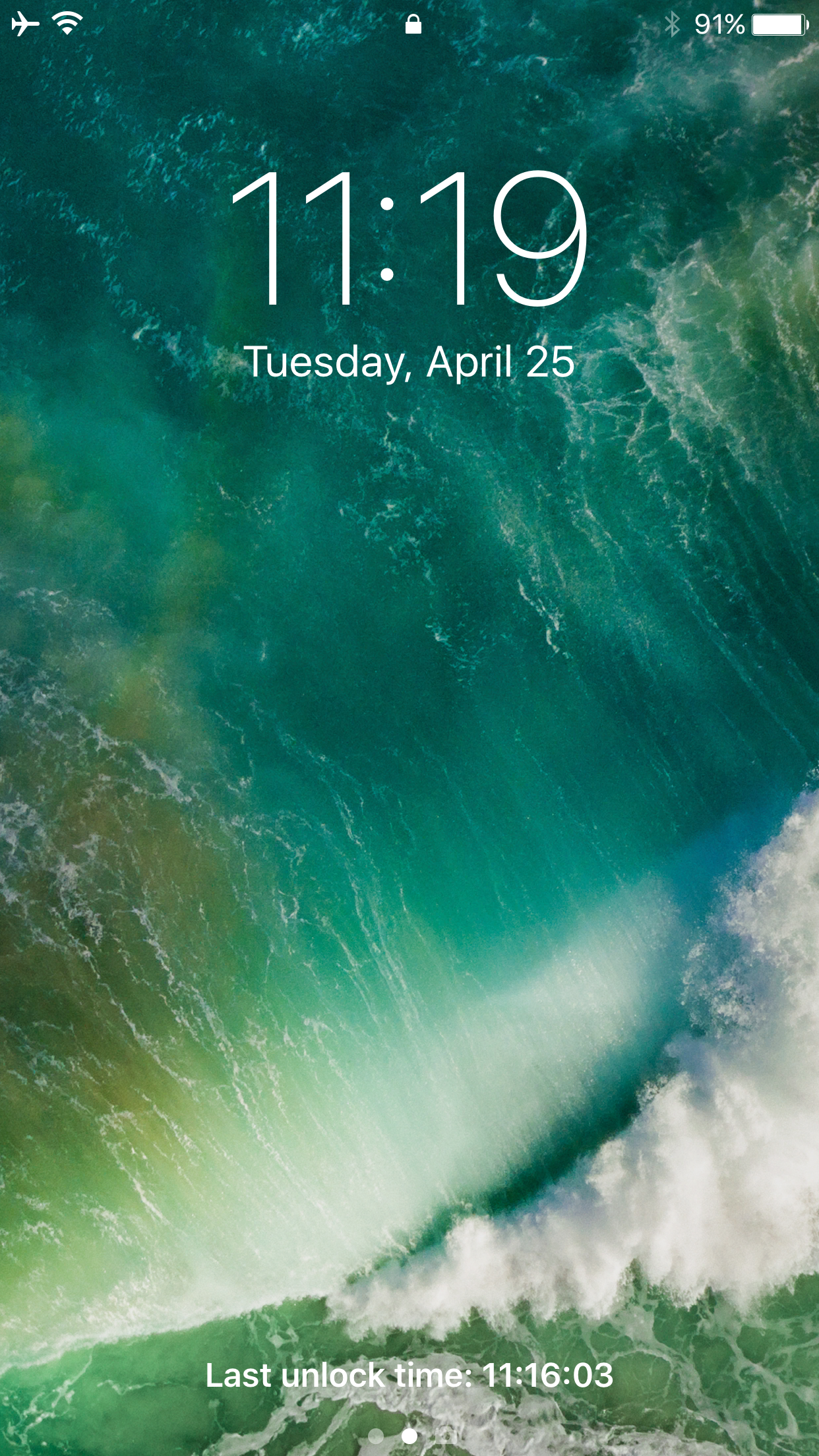
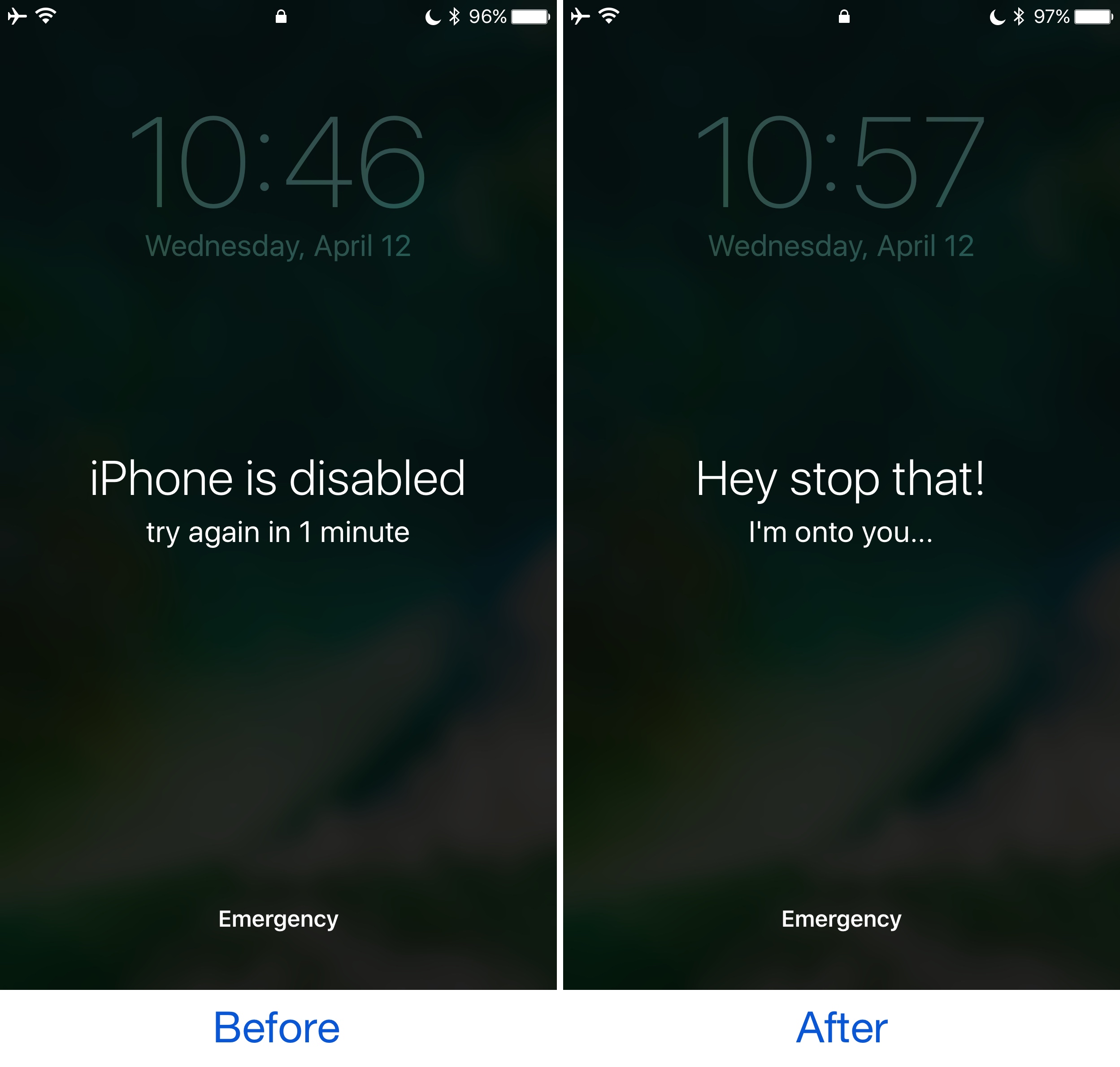
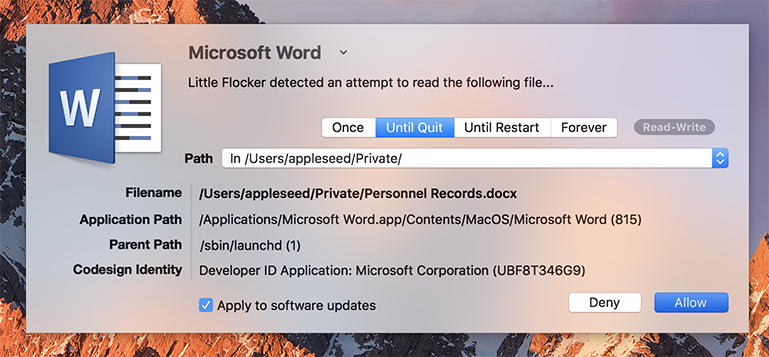
It's “impossible” for workers to take photos, let alone carry some components out
Workers are required to leave their phones, keys and other metals in a locker room
No metal is allowed inside the factories
There are security cameras in every assembly line
Security involves access cards, facial recognition cameras and metal detectors
The security level increased sharply ahead of iPhone 7 production.
For starters, management at the factories installed two metal detectors and increased their sensitivity, in turn creating problems for female workers wearing bras.
“All of a sudden, on that specific day, they couldn’t pass the security door, and they needed to go back and change everything,” said Dejian.
He says regular assembly line workers were strictly prohibited from bringing their cameras or phones inside the factories, unlike high-level managers who could bring their phones.
“I’m not sure whether photos can get leaked by that,” he said.
But even high-level managers were asked to wake up their phone's screen every time they went through the metal detectors so that security personnel could determine that they weren't carrying an unfinished iPhone unit concealed in a fake phone case. And if a worker does get caught attempting to carry an iPhone out of the factories, they're sent to the police.
In spite of all the security, leaks do happen and they're a fact of life.
Who's to stop a person from running to the press to tell them what they saw inside the factories? After they started building iPhone 7, some employees were able to confirm to the media that the device would come without headphone jack and with two cameras on the back.
“Those are some things that we can see and we can remember and we can tell the media later on,” said Dejian. Apple is known for holding its contractors to the highest security standards.
In that regard, the following excerpt is revealing:
When I was producing iPhone 6, I did see Apple come for audits. I think it was two or three times.
And every time when they come, the manger in the factories got very nervous. They would tell us you need to follow the procedure and sit straight, and don’t talk.
When they kicked off iPhone 7 production, Apple staff was there “every single day”.
Factory workers are reportedly aware of how popular the iconic smartphone is and think it’s “very cool” that they get to see Apple's unreleased products before anyone else.
The full video interview is available on Business Insider.