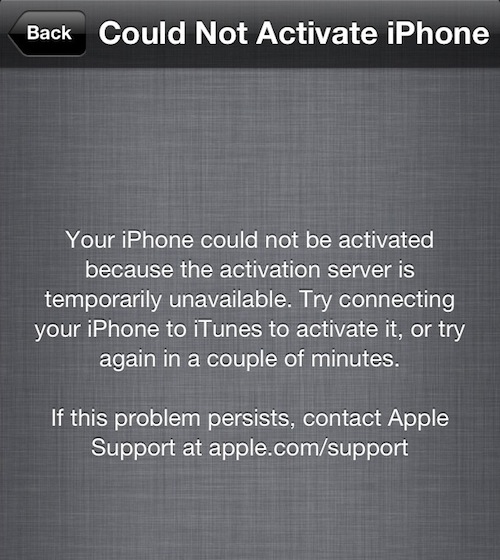
While independent security researcher Ibrahim Balic claimed responsibility for taking down Apple's Dev Center, in reality his discovery of an iAd Workbench vulnerability had nothing to do with the Dev Center outage.
Apple this morning credited Balic for reporting the iAd Workbench bug that did allow him to obtain full names and Apple IDs of Apple's registered iOS and Mac developers.
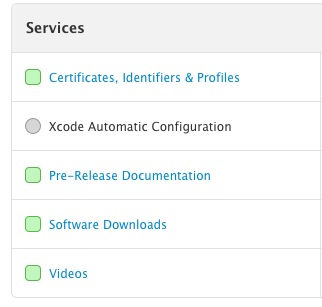
While it's a bit murky whether or not Balic was solely responsible for the system-wide Dev Center shutdown, Apple today wrote on its Web Server notifications page that it fixed a "remote code execution issue" that allegedly caused the downtime...