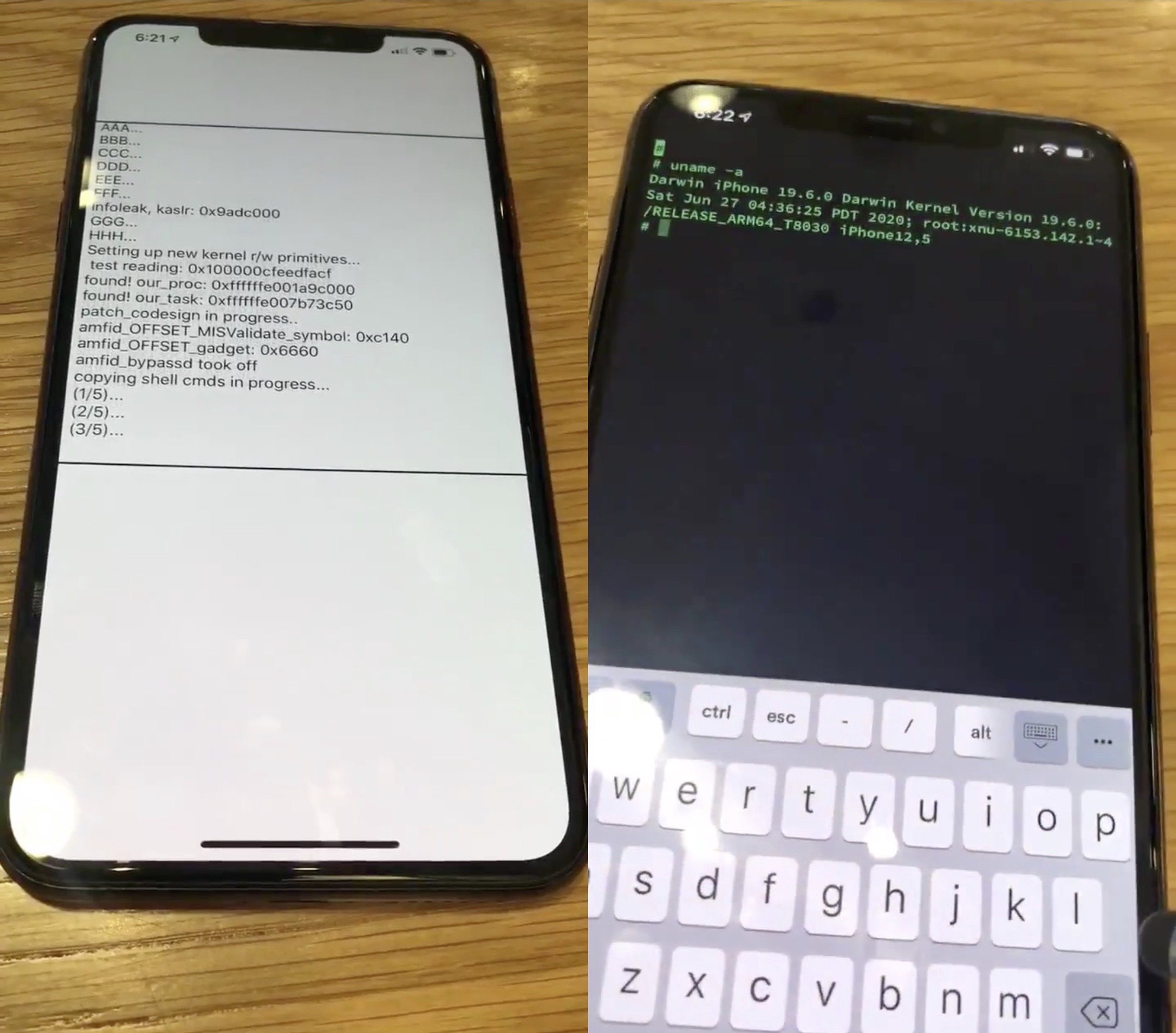
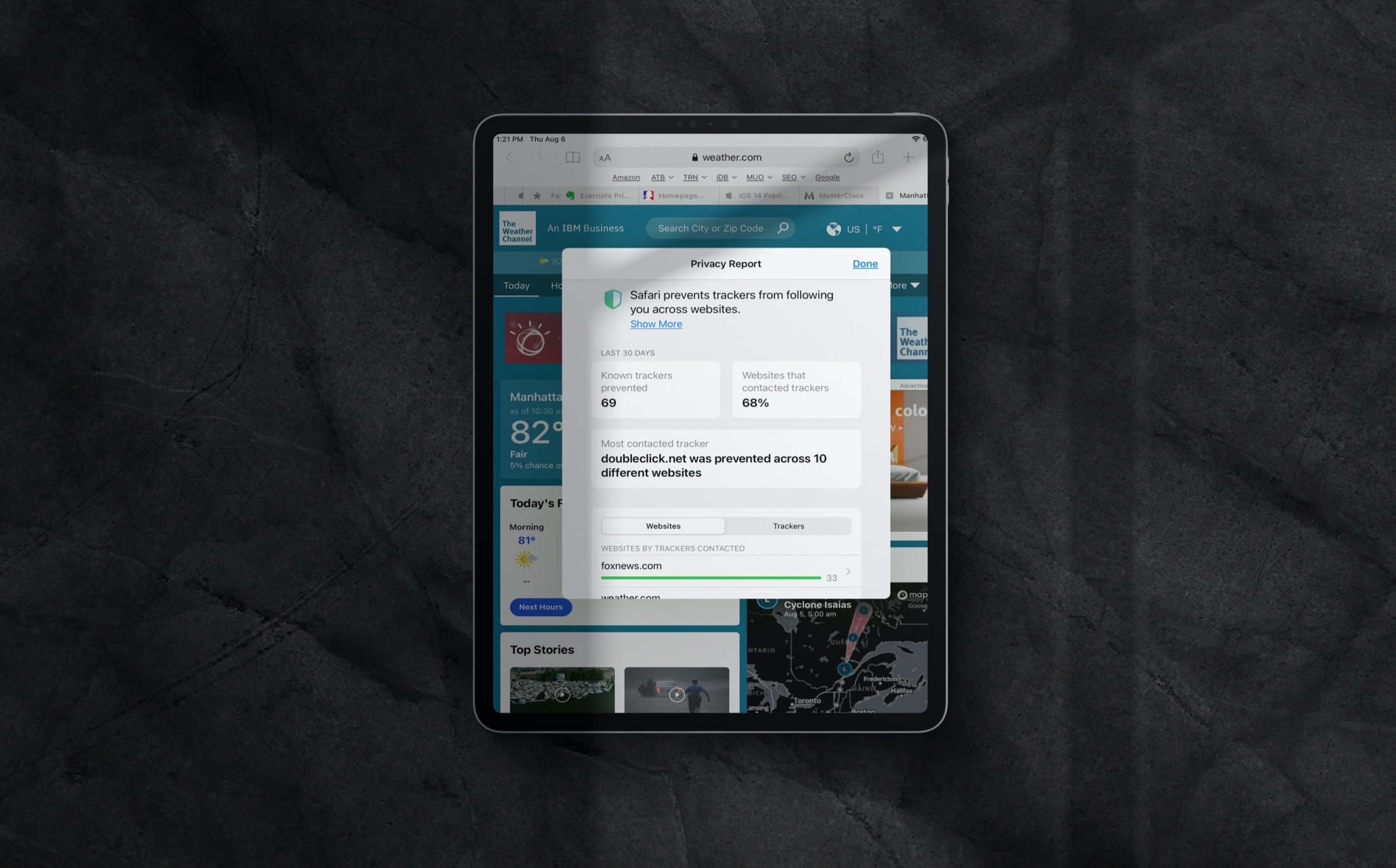
Privacy is a growing concern these days as seemingly more and more apps try to harvest our personal data for the sake of monetary gain. What we learn from this is actually quite simple: people generally don’t like being tracked and prefer to enjoy their right to privacy.
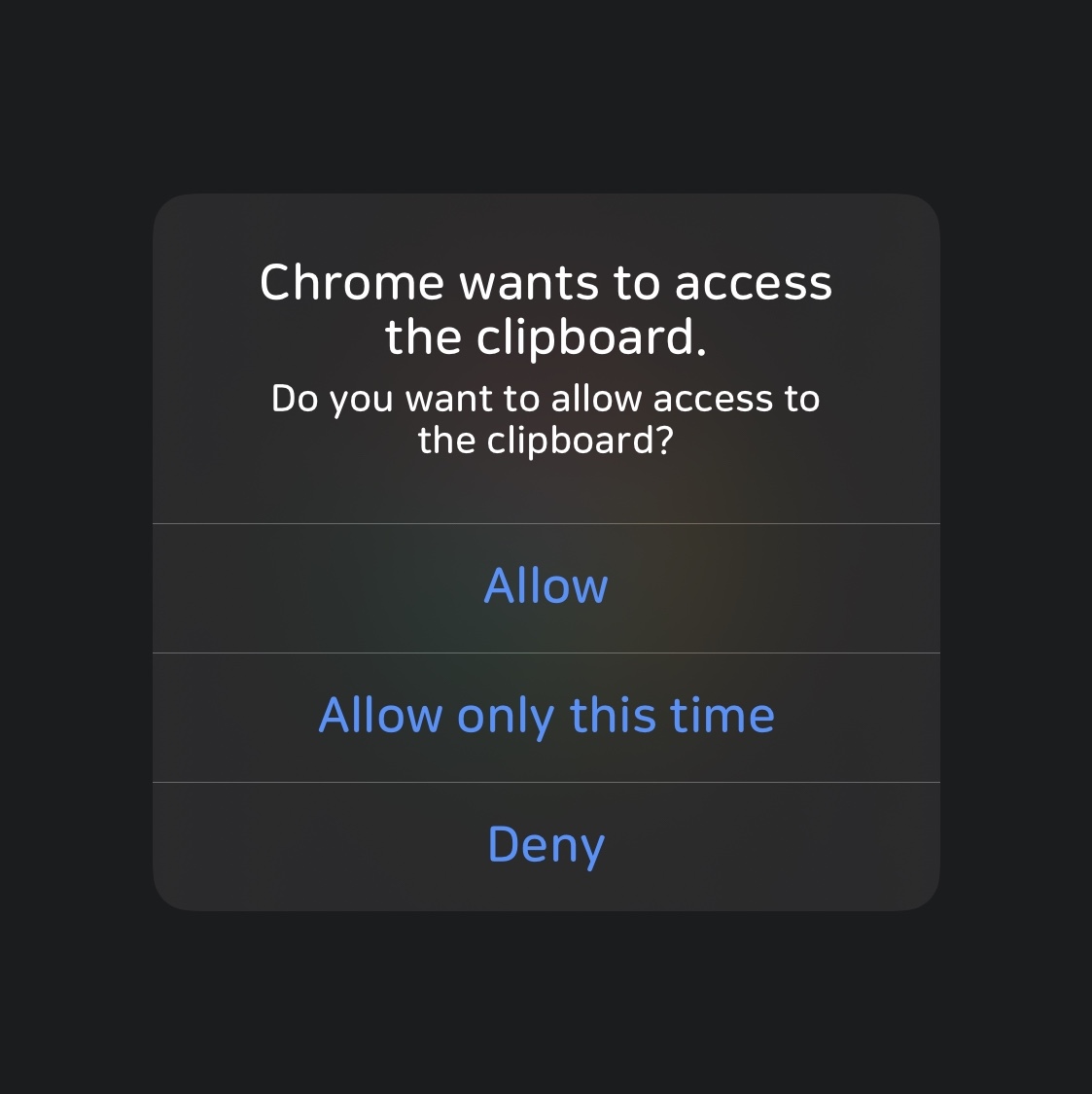
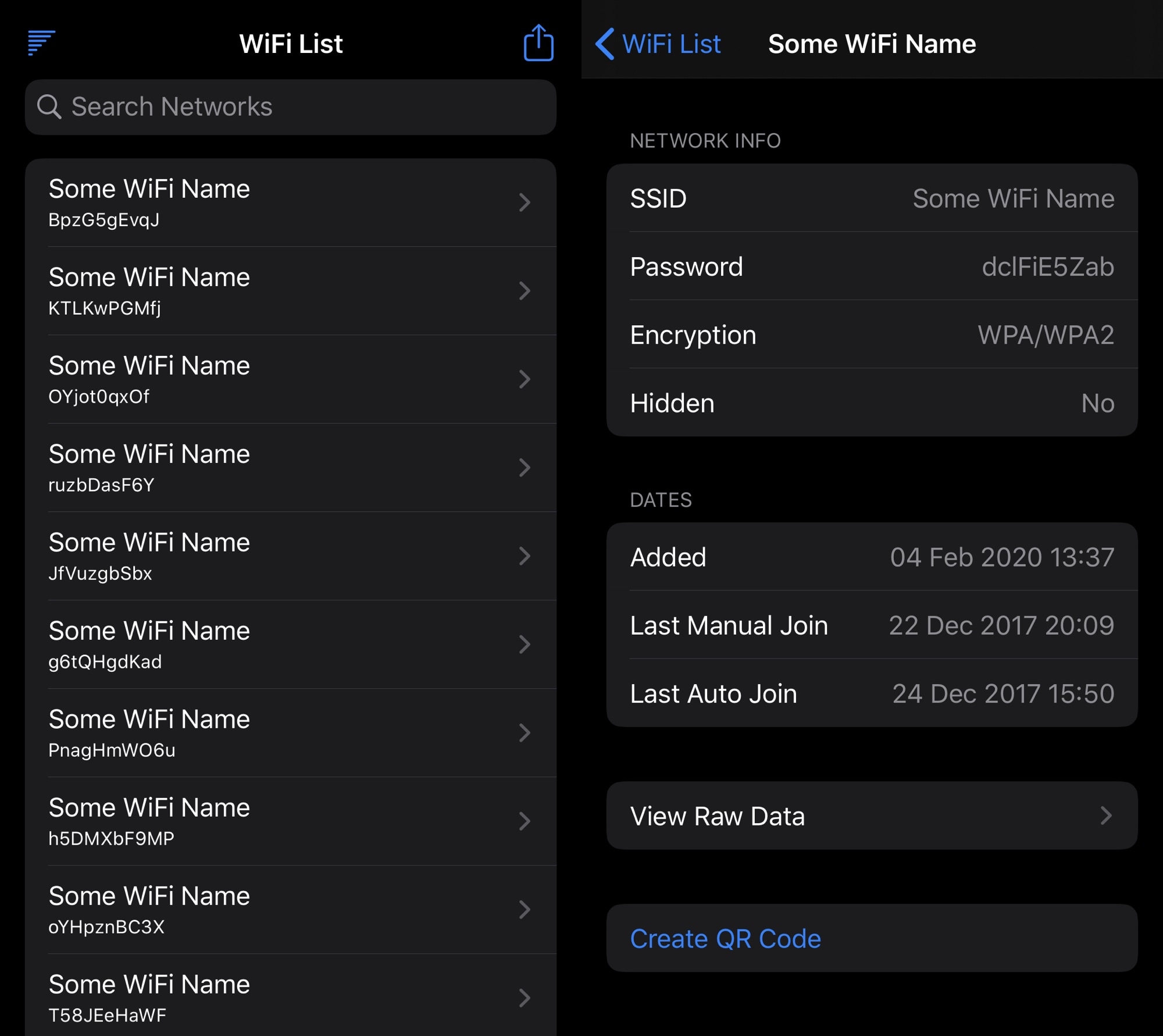
Smartphone-centric privacy breaches happen a number of different ways, including location tracking, camera or microphone spying, and/or Photo Library snooping. But the pasteboard, which may sometimes store sensitive information if you do any copying and pasting on your iPhone or iPad, is another thing that often slips under the radar.