
The release of Brandon Azad’s oob_timestamp exploit yesterday afternoon meant that Pwn20wnd could finally get to work on adopting support for the unc0ver jailbreak. On the other hand, a plethora of Tweets shared early Saturday morning suggest that doing so could be a lot more work than initially thought.
While Pwn20wnd has every intention of updating the unc0ver jailbreak to support iOS 13.3 on A12(X)-A13 as planned, it seems that the biggest complication would be the impractical amount of work needed to support each and every individual firmware version between iOS 13.0 and 13.3 on each and every device type:
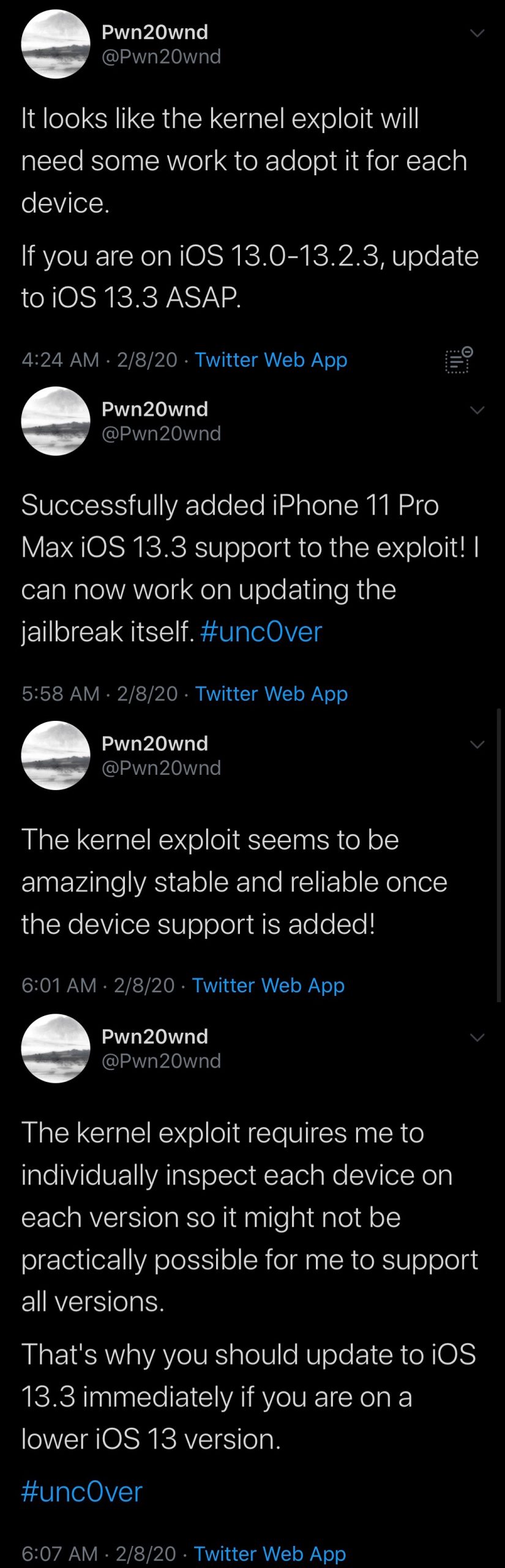
Pwn20wnd noted that adding support for every device type and firmware likely wouldn’t be ideal for him to do. Albeit possible, it would take substantially more time and resources than he has to offer.
Given the unfortunate circumstances, Pwn20wnd recommends that everyone update (or downgrade) specifically to iOS 13.3 since it is still being signed by Apple and because it’s the last public firmware supported by Azad’s oob_timestamp exploit. We’d recommend the same.
The oob_timestamp exploit was originally released to support the iPhone 11 on iOS 13.3, and Pwn20wnd has already gotten it working on the larger sister device – the iPhone 11 Pro Max. With just a little more work, he should be able to support the iPhone 11 Pro and perhaps even previous-generation devices with the A12 processor such as the iPhone XS and iPhone XS Max.
Pwn20wnd also said that the exploit was surprisingly stable, which speaks to how easy it could make jailbreaking once in users’ hands.
In earlier Tweets, Pwn20wnd said he would be prioritizing support for A12(X)-A13 since older devices are already supported by checkra1n, but the convenience of an on-device jailbreak cannot be overstated. Although checkra1n can’t be patched by Apple, unc0ver doesn’t require a computer, so there are pros and cons to each jailbreak.
Despite the apparent challenges, it seems like unc0ver could be well on its way to supporting iOS 13 for the first time thanks to Azad’s new exploit. Are you excited to take advantage of an updated unc0ver when it comes? Discuss in the comments!