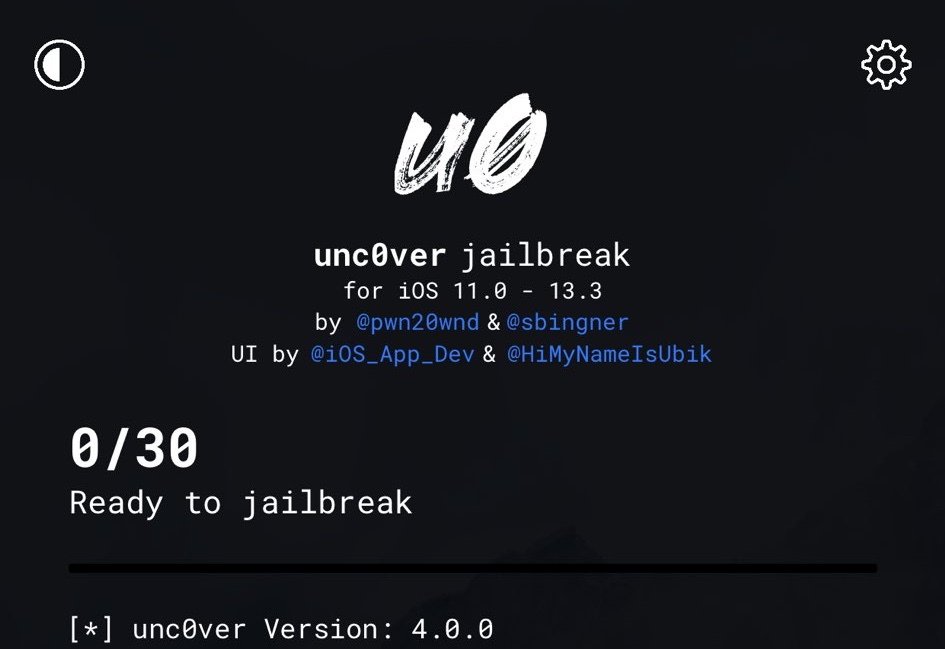
Kicking off this Wednesday morning, hacker and unc0ver lead developer Pwn20wnd has issued an updated version of the unc0ver jailbreak tool dubbed version 4.2.1.
In a Tweet shared just minutes ago, Pwn20wnd said that unc0ver v4.2.1 would resolve a plethora of issues that were present in v4.2.0, including battery drain and Substitute unreliability: