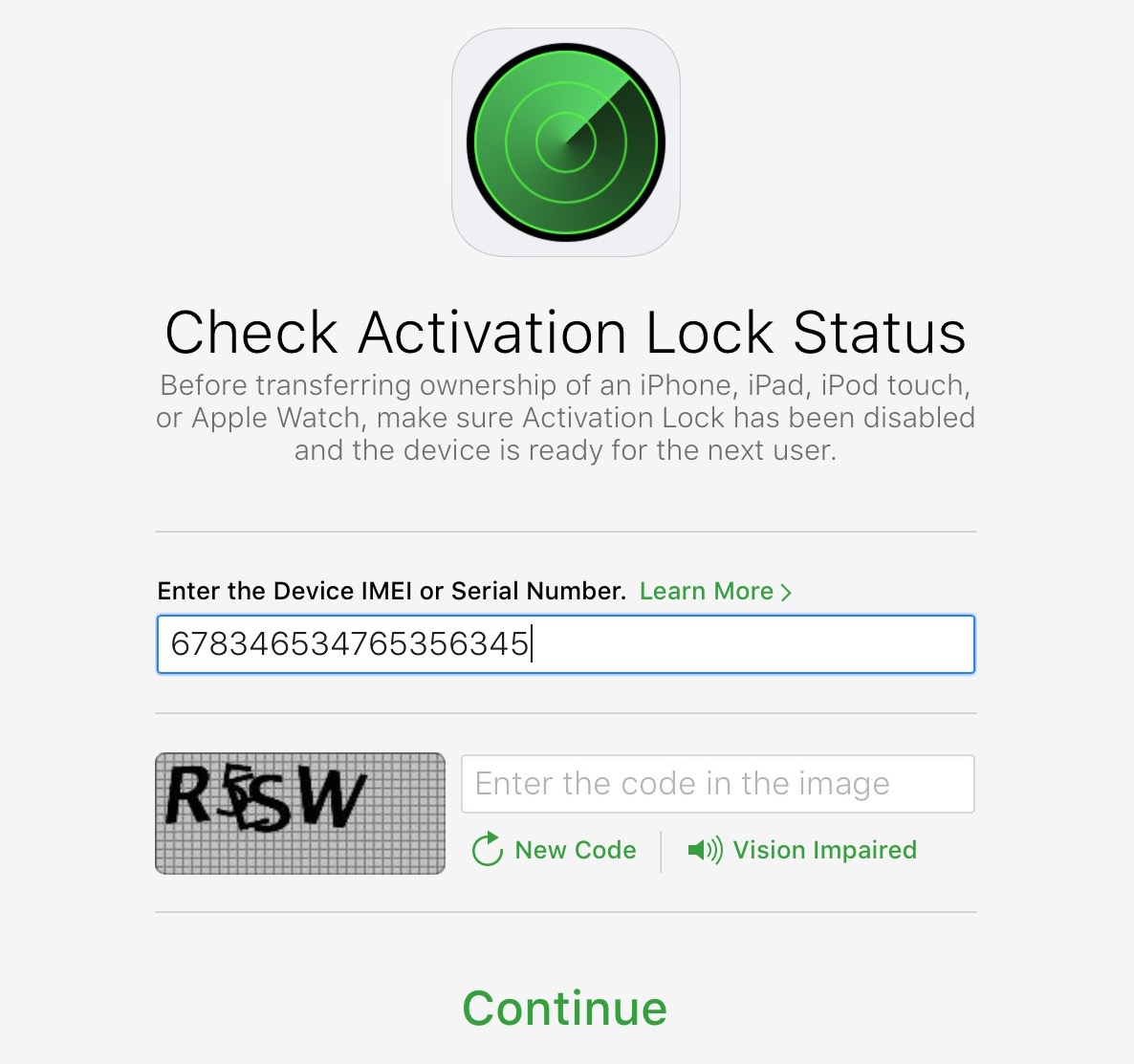
As we reported, Apple recently took down its tremendously useful Activation Lock webpage for reasons unknown. The theft-deterrent tool allowed legitimate iOS device owners and just about anyone else to check the status of the Activation Lock feature by entering a serial number. Apple provided no explanation for the removal, but all checks point to it being a precautionary measure meant to prevent hacks relying on stolen serial numbers, as a reader pointed out in comments.
The Activation Lock web tool allowed users to enter a serial number of an iOS device to verify if Activation Lock has been enabled on it. The tool was also readily accessible to anyone who would run a batch of serial numbers against it i order to see which one worked before leveraging a bypass hack to unlock the bricked device.
Hackers would also change a few characters in an invalid iOS device serial number until stumbling across a combination that would let them unlock a bricked device.
This is part of a bigger issue where hackers steal iOS device serial numbers for nefarious purposes. Say I got hold of your iPhone’s serial number (i.e. you shared it online in a Settings app screenshot). I could use the removed web tool to check if you had Activation Lock enabled before bypassing the protection on your device.
“Someone could be using a serial number of a phone that has not been sold yet, meaning it will be iCloud-locked even on the first setup,” our reader wrote. “It’s a smart move by Apple even though it hurts people who want to buy second hand devices.”
In the video below (I set it to start at mark 5:25), you can see how the iCloud Activation Lock web tool, released in October 2014, can be used to verify that automatically generated serial numbers are available and unlocked for stolen iOS devices.
As MacRumors notes, this scheme that steals valid serial numbers from existing iOS users might explain why some people reported finding their devices locked to an unknown Apple ID and not being able to regain control without Apple’s help.
In November, a researcher exploited a bug in iOS 10.1.1 to bypass Activation Lock protections on an iPad by flooding Wi-Fi logins with long character strings and repeatedly opening and closing a Smart Cover. It has been patched since.