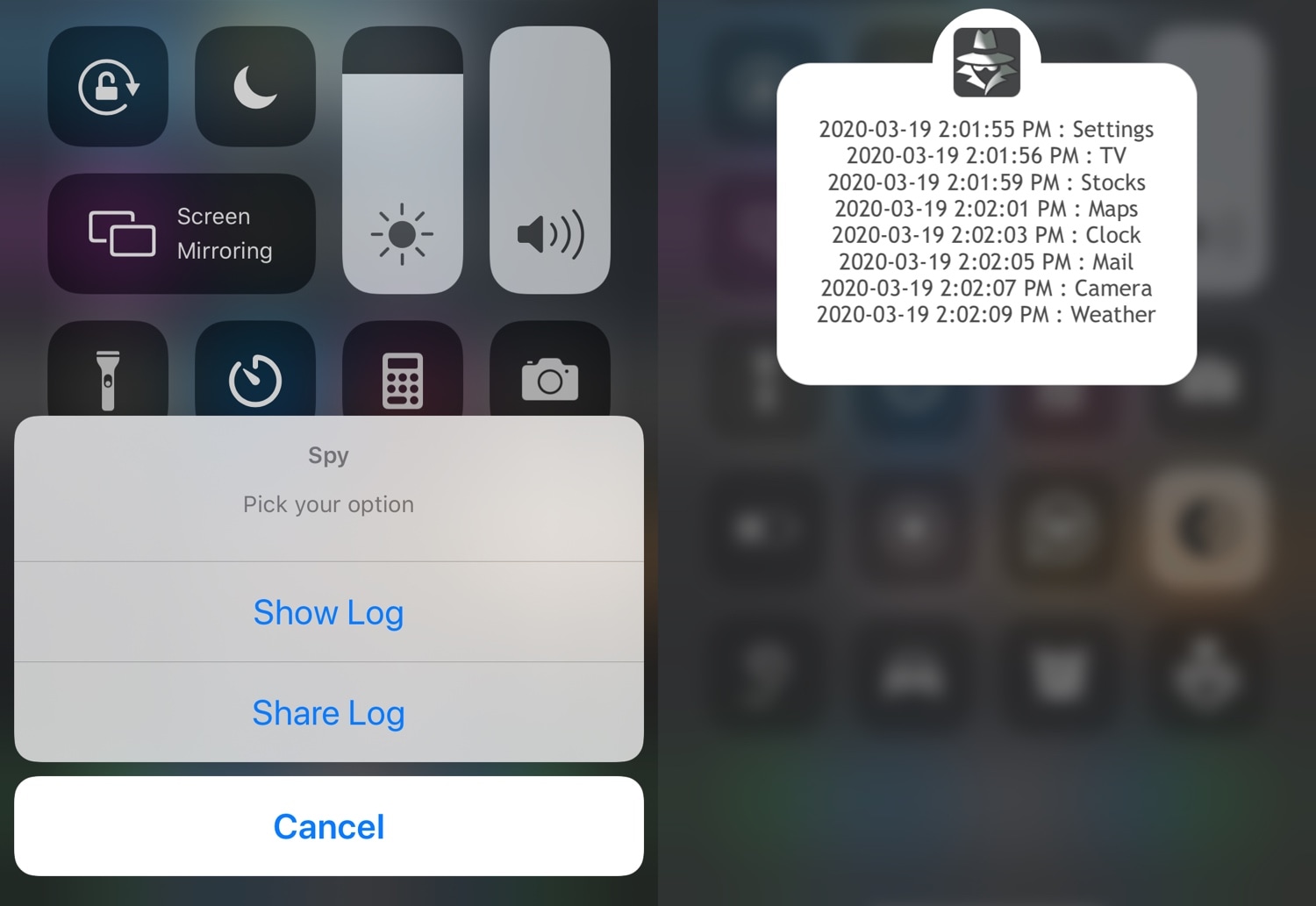
Apple has acknowledged that all 2020 iPad Pro models will disconnect their built-in microphones at the hardware level when a case is attached to the tablet and closed. The privacy and security enhancement prevents malicious software from secretly recording users.
2020 iPad Pro disconnects its microphones when not in use to prevent eavesdropping