The Verge claims to have discovered a major security hole which allows attackers to reset your Apple ID password using only your email address and date of birth. Yes, you read that right. The scary part is that it doesn't take a genius to harvest these two pieces of information from Google and your social media accounts or by analyzing your online identity per se.
Exploiting the vulnerability basically lets attackers take over your Apple ID account, and with it all your purchases, iTunes credits, email messages, contacts, your Photo Stream and pretty much any personal data residing up in the Apple cloud.
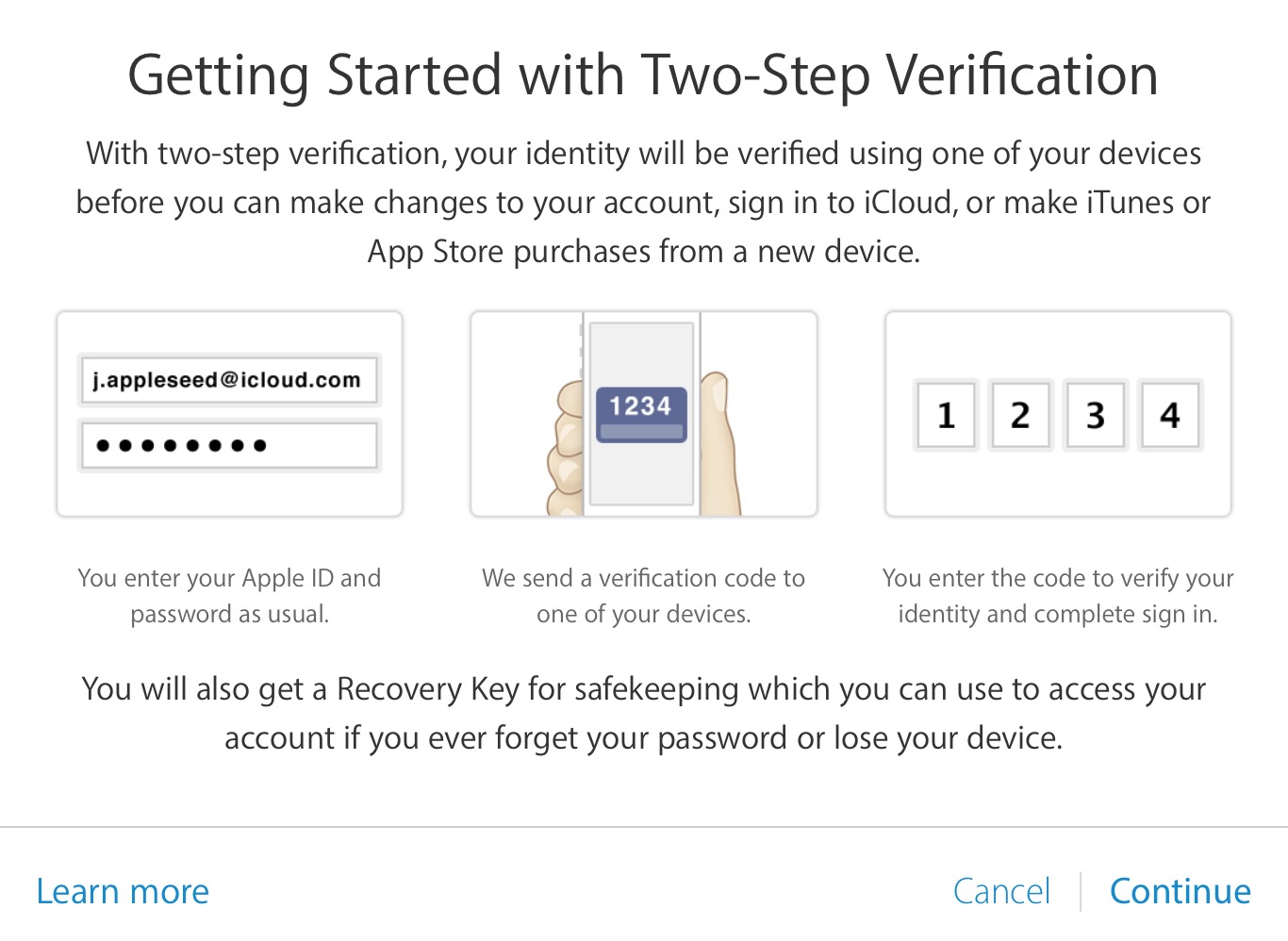
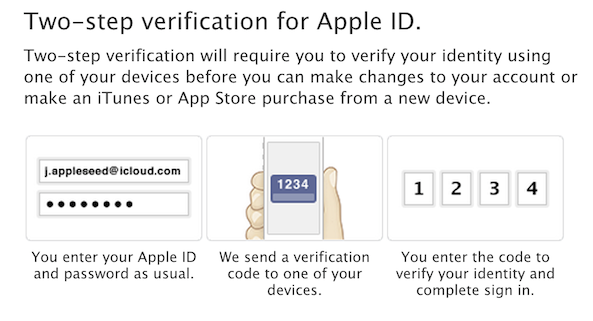
Apple's iForgot page went down "due to maintenance" shortly after the incident, presumably to prevent exploits until Apple plugs the security hole. Conveniently enough, the company just recently rolled out a new (and way overdue) two-step verification process to protect your Apple ID using not only your password, but also by tapping your trusted devices and a recovery key.
With this exploit making the headlines, you should enable two-step verification now (Cody has a timely tutorial on that)...