Last week, Apple’s Marketing SVP Phil Schiller tweeted out a link to a mobile malware report that showed Android devices accounted for a staggering 79% of new mobile threats last year, while iOS devices accounted for just 0.7%.
Of course, the fact that he tweeted the link was far more surprising than the report’s data. After all, we’ve known for years that Android is far more susceptible to mobile malware than iOS. Right? Security experts say not so fast…
The Next Web‘s Matthew Panzarino points to a new report from security firm Skycure that highlights and details, what they are calling, a major security vulnerability for iOS: configuration profiles.
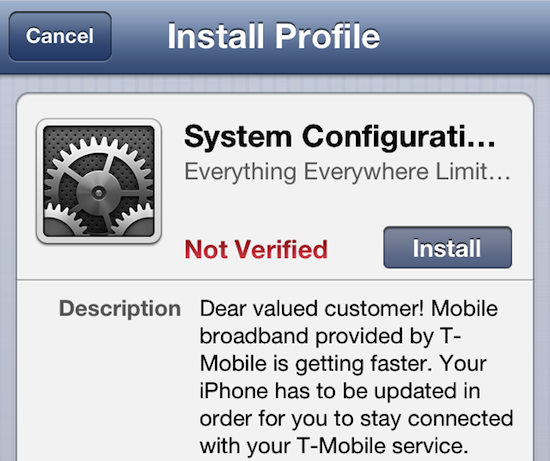
What is a configuration profile? It’s a tiny file that has the ability to alter settings in iOS. Everyone has seen them at one point or another. Apple used to use them to deliver patches, and carriers sometimes use them to distribute updates.
But according to Skycure, if used maliciously, these profiles can be very dangerous. Even though their use is approved by Apple, they aren’t subject to the standard ‘sandboxing’ rules that apply to third party App Store apps and websites.
To demonstrate the danger, Skycure setup a fake website with a prompt to install a configuration profile and sent the link out to Panzarino. After installing it, he found out they were able to pull passwords and other data without his knowledge.
“After the profile was installed, Sharabani demonstrated to me that he could not only read exactly which websites I was visiting, but also scrape keystrokes, searches and login data from apps like Facebook and LinkedIn. To be perfectly clear, this is not a vulnerability within iOS, instead it uses standardized frameworks to deliver a profile that has malicious intent.”
Should you panic? No. You have to actually install these ill-willed profiles for your device to be susceptible to the above behavior. But it’s not hard to imagine ways to tempt users into doing that: “Free music and movies, install app now.”
The big takeaway here is really to just make sure you avoid installing configuration profiles from unknown or sketchy sources. Considering how much they’re used, we don’t imagine Apple will be getting rid of them anytime in the near future.