Apple yesterday let iOS 6.1.3 out of the gate, fixing the widely reported Lock screen vulnerability. As you’re probably aware, the glitch was first detailed a month ago and lets people with access to your iPhone, iPad or iPod touch easily bypass your passcode and mess with your private data on the device. But as is often the case, new software releases fix old bugs and introduce new ones to be squashed in the future.
A report Wednesday claims an all-new Lock screen vulnerability has been discovered in iOS 6.1.3, one making it easy to – you guessed right – bypass one’s passcode and gain access to an unsuspecting user’s contacts and photos kept on the device. Luckily, this one can be avoided easily by disabling the Voice Dial feature…
Dutch web site iPhoneclub.nl passes along the above video by YouTube user ‘videosdebarraquito’ highlighting the flaw.
The trick involves using the iPhone or iPod touch’s Voice Dialing feature to dial a number – in this case, ‘123’). Then, as soon as the calling confirmation pops up (“dialing 123”), eject the SIM card to abruptly end the call.
You should be now able to access the recent call history, as well as check out Photos and browse through Contacts – even add a new contact or picture, either by taking a new photo or by picking one from the photo library on the device.
The good news is, the glitch “only” seems to allow intruders to access your contacts and photos, but not other critical apps like Phone, Messages and what not.
Unfortunately, we cannot tell from the video whether or not the poster is in fact running iOS 6.1.3. For what it’s worth, iPhoneinCanada was able to confirm that the glitch affects their iPhone 4 running iOS 6.1.3.
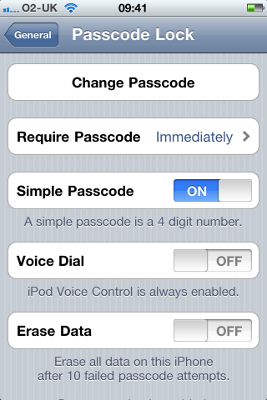
To be on the safe side, owners of older iPhone and iPod touch devices which don’t support Siri must disable Voice Dialing by going to their device’s Settings > General > Passcode Lock.
Those with an iPhone 4S or iPhone 5 are wise to disable Siri access from the Lock screen, again in Settings > General > Passcode Lock. On the flip side, anyone looking to exploit this glitch to their advantage must have physical access to your device and be able to eject the SIM.
If it’s any consolation, it isn’t just Apple’s handset – a dangerous Lock screen vulnerability has also been discovered on Samsung’s Galaxy S4, have a look below.
Again, I haven’t had a chance to test this on my device yet so your mileage may vary.
Why not help us fill in the blanks by testing this out and share your experience with fellow readers down in the comments?