Despite the absurd amounts of time and money that Apple pours into security efforts to make iOS one of the most secure mobile operating systems available today, it seems that even iOS 12.1, the latest publicly-available firmware version on the iPhone and iPad, isn’t entirely hack-proof.
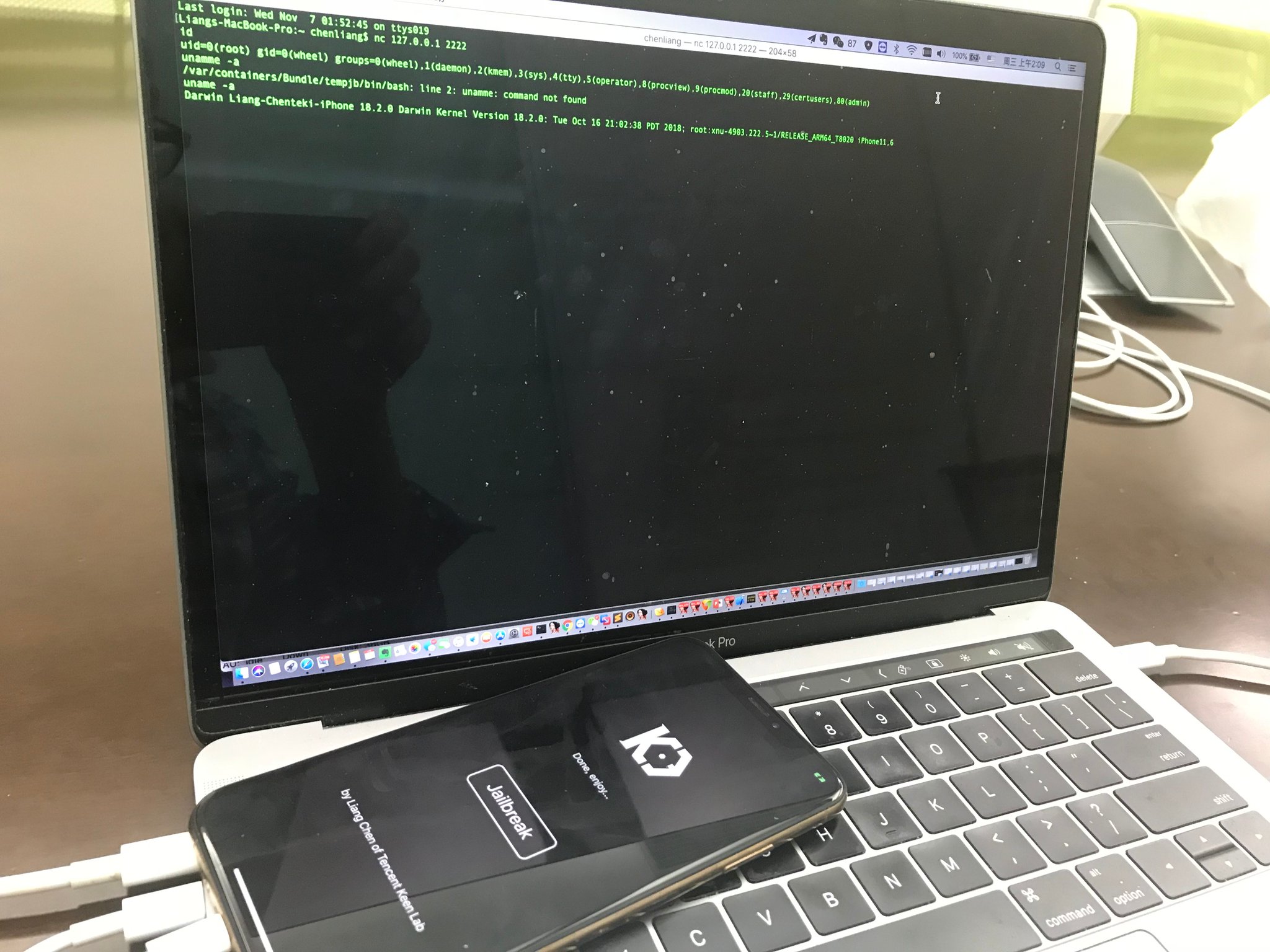
At the recent Pwn2Own contest in Tokyo, Richard Zhu and Amat Cama, a duo of white hat hackers, reportedly harnessed the power of a powerful Safari-based 0-day exploit to recover a photograph that was recently deleted from an iPhone X’s native Photos app.