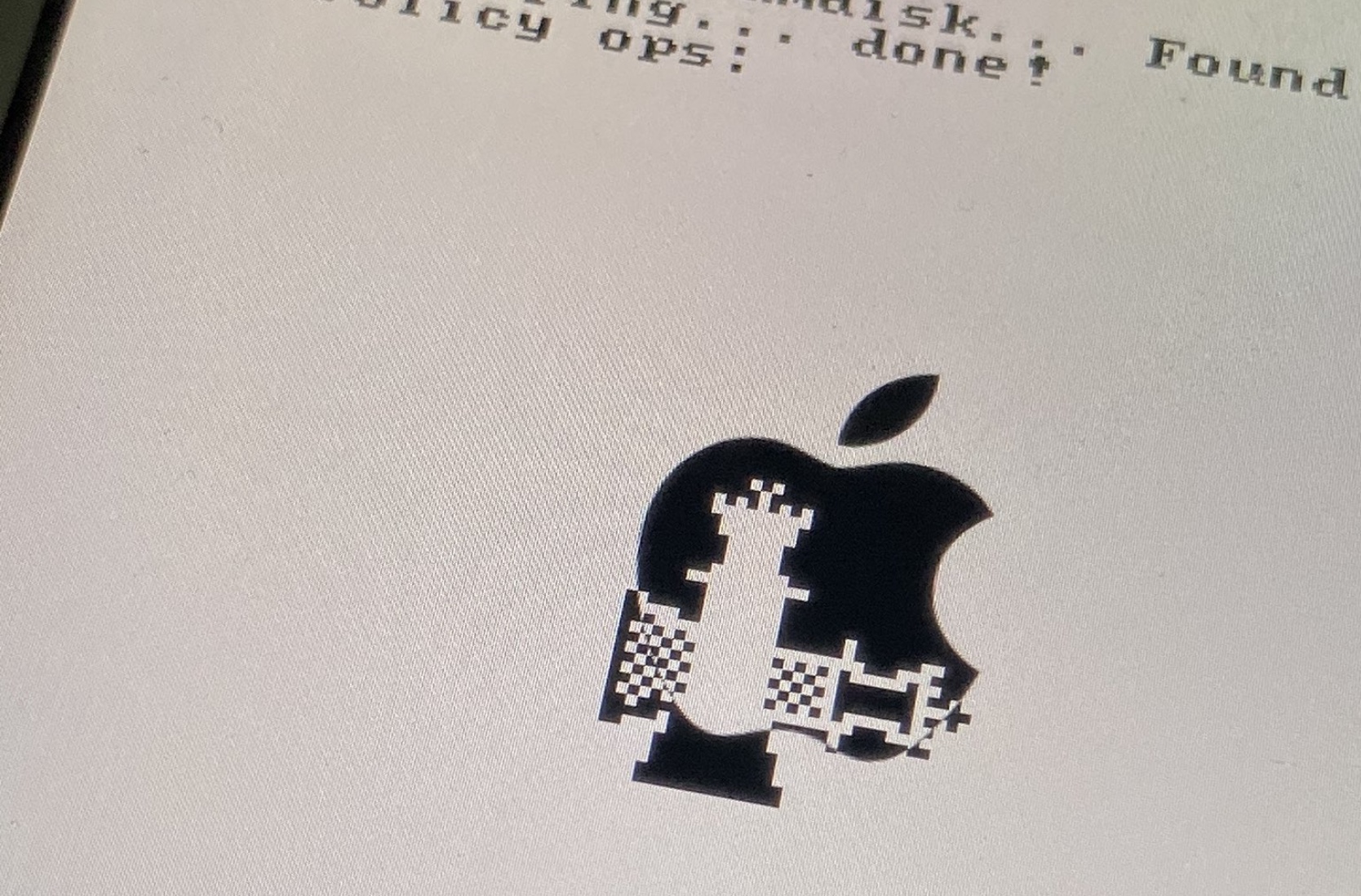
In an unfortunate turn of events for the jailbreak community, it seems that Apple will not be supporting the iPad (7th generation) with this year’s release of iPadOS 26, which means that the last remaining checkm8 bootrom exploit-vulnerable device will no longer receive major software updates this year and that checkm8-based jailbreaks will not be able to pwn iPadOS 26.
iPadOS 26 drops support for iPad (7th generation), the final checkm8 bootrom exploit-vulnerable iOS/iPadOS device