Are you seeing an “Unsecured Network” or “Weak Security” warning on your iPhone, iPad, or Mac? In this guide, we’ll share more details about this issue and help you fix it.
How to fix the Weak Wi-Fi Security warning on iPhone, iPad, Mac
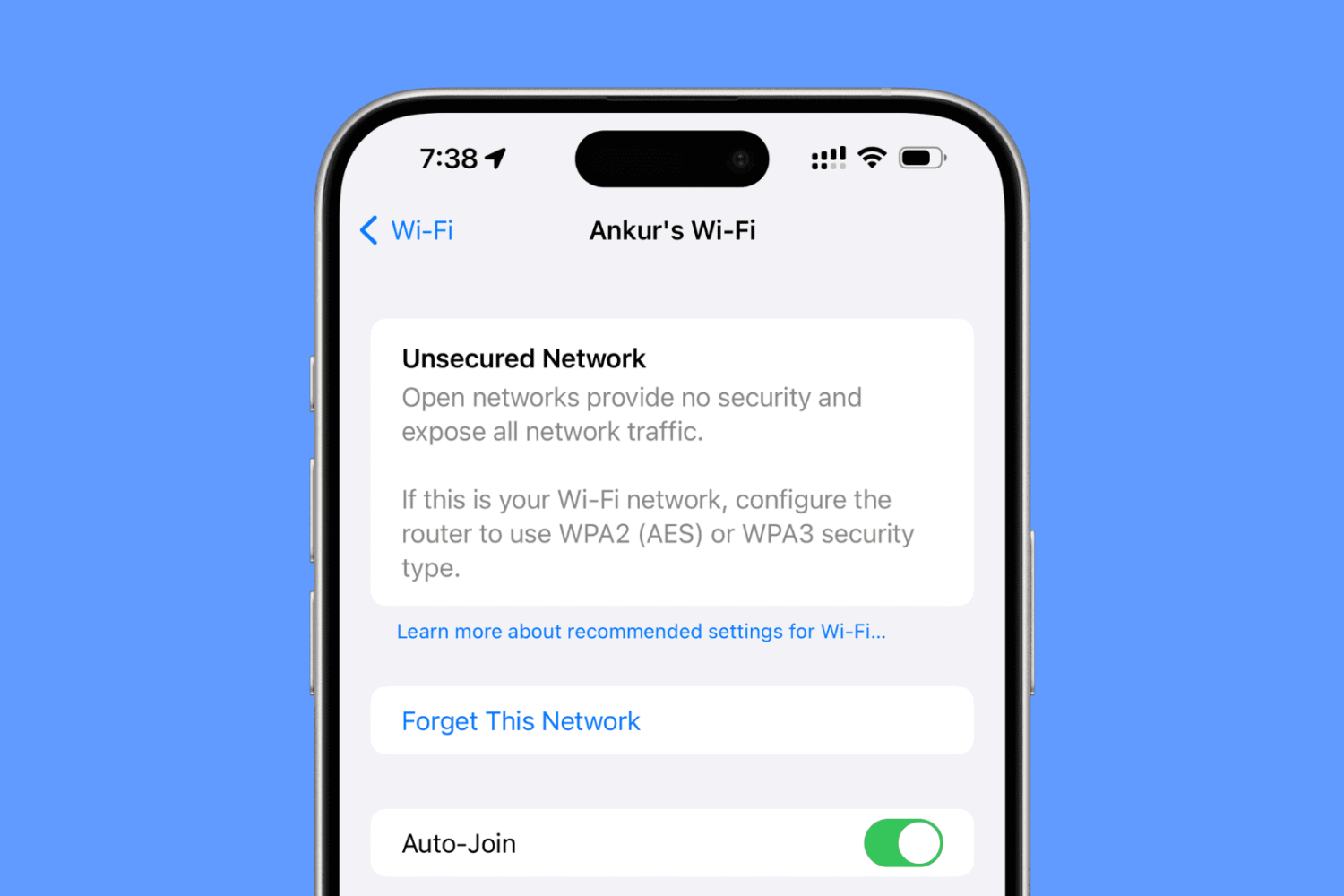
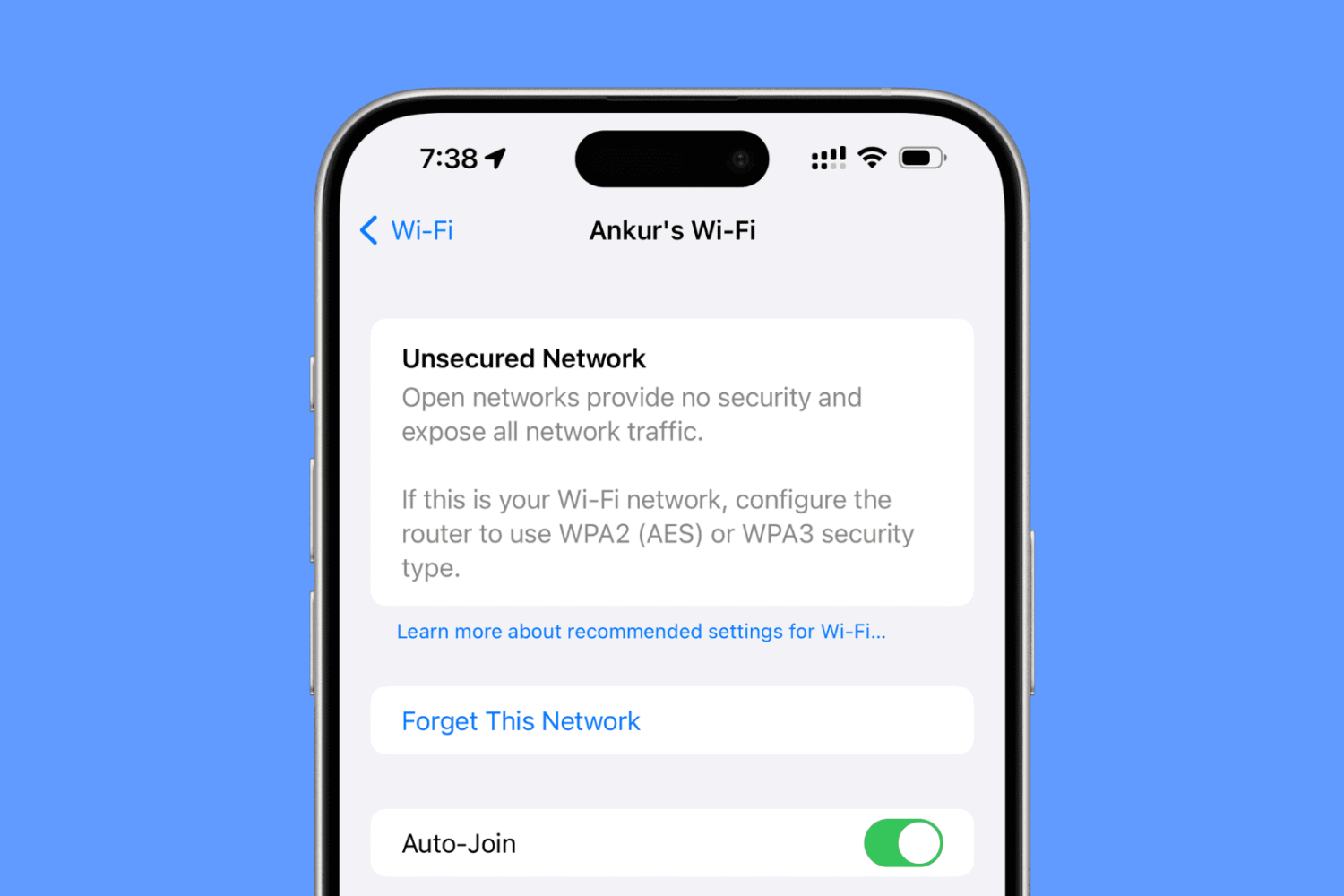
Are you seeing an “Unsecured Network” or “Weak Security” warning on your iPhone, iPad, or Mac? In this guide, we’ll share more details about this issue and help you fix it.

Engineers at Apple and Cloudflare, a web infrastructure company providing content delivery network services, announced today that they have collaboratively developed a new internet protocol focused on privacy.
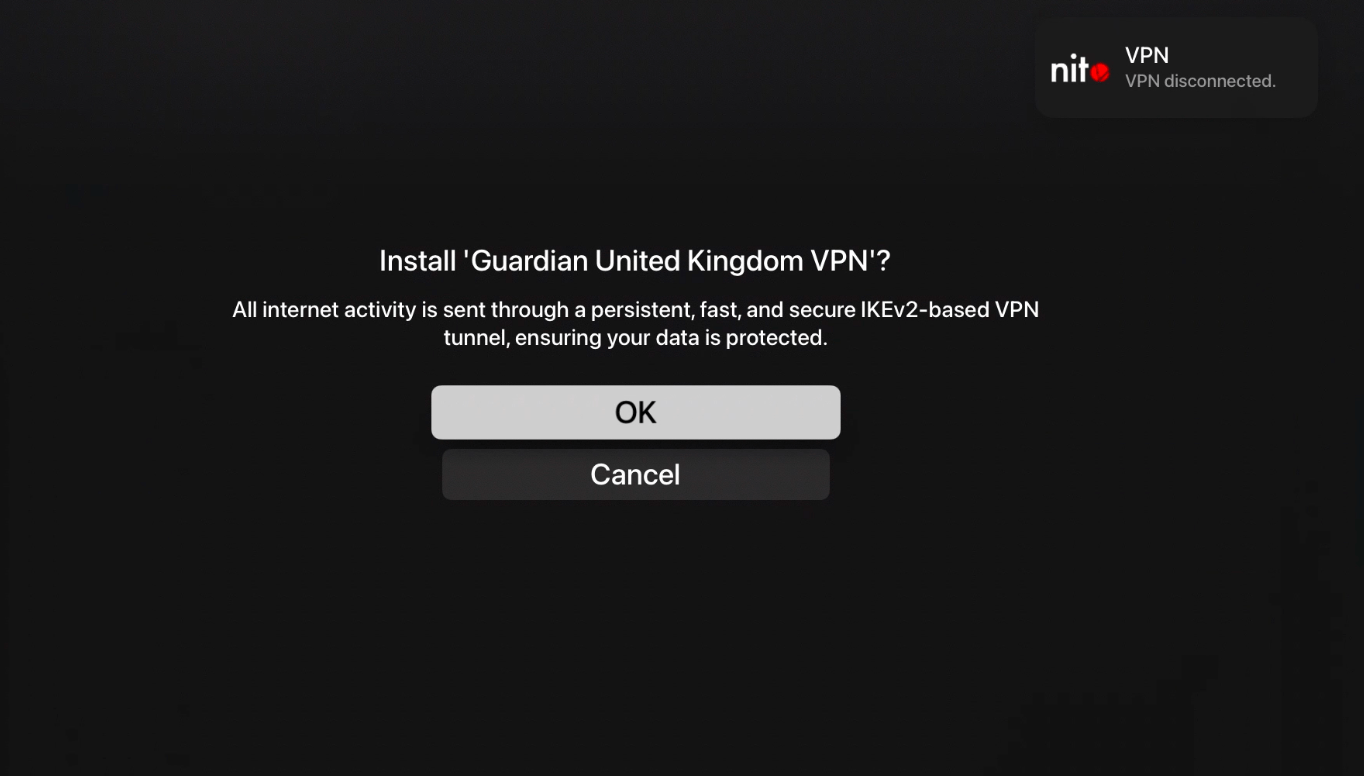
About a month ago, Guardian Firewall VPN founder and CEO Will Strafach, a former member of the Chronic Dev Team, shared a particularly exciting announcement in that nitoTV (now going by @freenitoTV on Twitter) had gotten VPN connections working on the Apple TV platform for the very first time; albeit with a jailbreak.
The aforementioned jaw-dropping feat demanded tons of complicated hackery, but after lots of research, development, testing, and refinement, the project, officially dubbed “vpnd,” is now available for jailbreakers who might want to try their hand at configuring a VPN connection on their own Apple TV.

Accomplished security researcher Ian Beer, known for releasing a host of iOS exploits used by modern jailbreak tools, dropped a bombshell on Twitter late Wednesday evening after sharing a detailed blog post about a jaw-dropping radio proximity exploit affecting up to and including iOS and iPadOS 13.5.
The blog post summary goes on to explain that the hacker can remotely trigger kernel memory corruption through the execution of arbitrary code. Furthermore, it can force affected iOS and iPadOS devices in radio proximity to reboot with no user interaction needed or put privacy at risk by breaching user data or utilizing cameras and microphones without the user’s knowledge. Scary indeed…
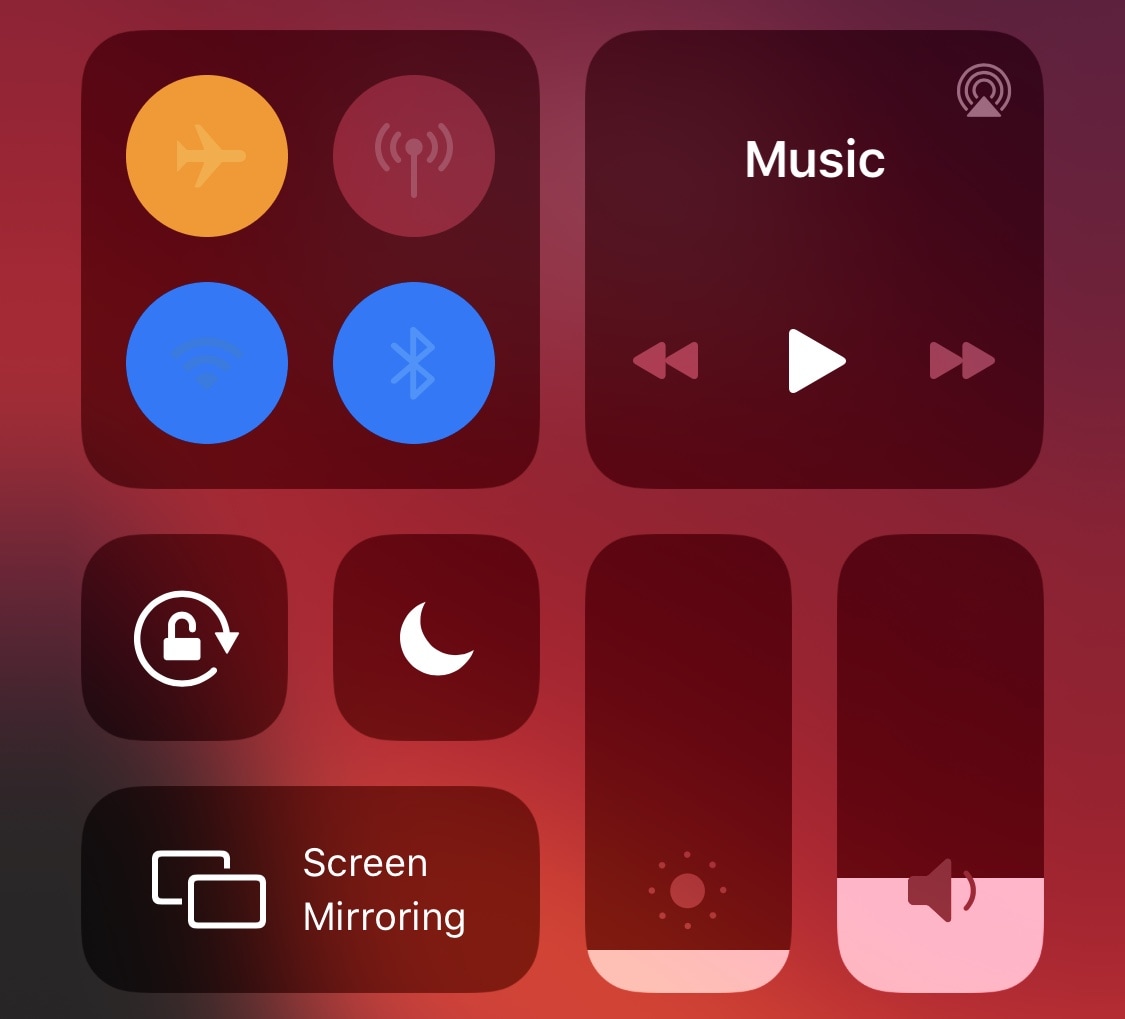
I love how convenient Control Center makes it to toggle my iPhone or iPad’s controls on or off in a pinch, but I’m almost certain that anyone who’d grab my iPhone when I’m not looking might feel exactly the same way. In fact, Control Center makes it far too easy for a thief or mischief-maker to toggle Airplane Mode as a hindrance to handset recovery, and that’s enough to make anyone second-guess the added convenience…
Grounded is a brand new and free jailbreak tweak by iOS developer biD3V that’s designed to prevent such issues from living rent-free in your head. The tweak works by allowing users to make certain Control Center toggles unusable as long as your iPhone or iPad is locked, but they become usable the moment you authenticate yourself.

As promised, following security researcher 08Tcw3BB’s much anticipated presentation at HITB CyberWeek 2020, affiliated software security firm ZecOps has officially released an exploit for iOS & iPadOS 13.5.1-13.7.
The announcement, shared this Thursday afternoon via the ZecOps Twitter account, links to a blog post on the firm’s own website that discusses the exploit, how it works via a proof of concept, and how an attacker could use it:
Those paying close attention to the jailbreak community as of late would already know that there’ve been a number of recent developments that could eventually spell out the jailbreakability of iOS 13.5.1-13.7. If you missed the news, FreeTheSandbox is working on a public jailbreak supporting these firmware versions while security researcher @08Tc3wBB plans to release a dedicated exploit for use by the jailbreak community.
Neither of the aforementioned things have happened yet, but for those trying to keep tabs on everything as it happens, it might be worth mentioning that @08Tc3wBB plans to discuss his iOS 13.5.1-13.7 exploit on November 19th via HITB CyberWeek in a talk entitled “Jailbreaks Never Die: Exploiting iOS 13.7.”
The past few weeks have been crazy for anyone heavily invested in the jailbreak community. Not only was the checkra1n jailbreak updated to add support for A10(X) devices and iOS 14.1-14.2, but a new exploit PoC targeting iOS & iPadOS 13.x was released and FreeTheSandbox once again affirmed that a jailbreak with support for iOS & iPadOS 13.5-13.7 would be released in the near future without a definitive ETA.
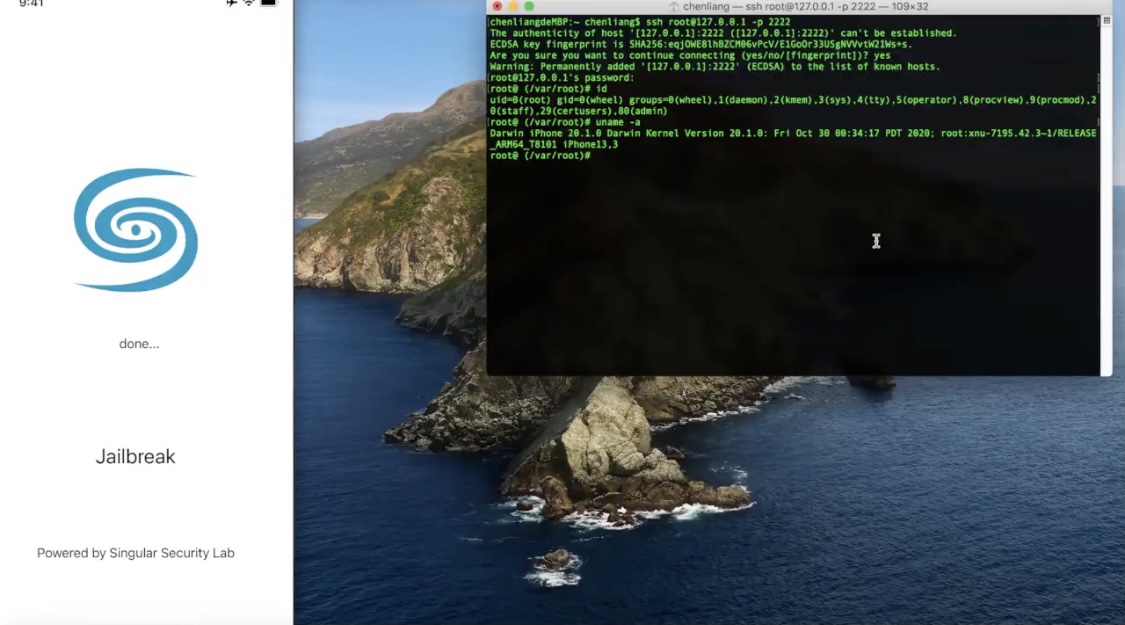
But the community was in for yet another teaser this week after talented security researcher Liang Chen (@chenliang0817) of Singular Security Lab (@SingularSecLab) demonstrated a working jailbreak on Apple’s brand-new iPhone 12 Pro handset running iOS 14.2 — the latest publicly available firmware at the time of this writing:

If you’ve been paying any attention to the iOS & iPadOS security research side of things recently, then you might’ve caught wind about a kernel bug discovered by Mohamed Ghannam (@_simo36) that held the capacity to pwn iOS & iPadOS 14.1 and below. Unfortunately, Ghannam later revealed that the bug didn’t work on iOS or iPadOS 14, and instead that it would only support variants of iOS & iPadOS 13.
While the aforementioned circumstances were indeed a bummer for those who’d been looking forward to a potential exploit release for iOS & iPadOS 14, the good news is that Ghannam officially released a kernel exploit proof of concept (PoC) dubbed 'OOB Events' on Wednesday with instructions for achieving kernel task port (tfp0) on iOS & iPadOS 13.7:

Apple unleashed iOS & iPadOS 14.2 to the masses yesterday afternoon, and while most iPhone and iPad owners gleefully updated to take advantage of more than 100 new Emojis and six new wallpapers, the updates also appeared to beef up their respective platforms’ security.
Security improvements are generally a good thing for users; however, they can be red flags for proponents of the jailbreak community since software exploits are the very things that make jailbreak tools possible. With that in mind, it may come as no surprise that jailbreak developers repetitiously remind the community to stay in the lowest possible firmware, as this can increase one’s chances of jailbreak eligibility.
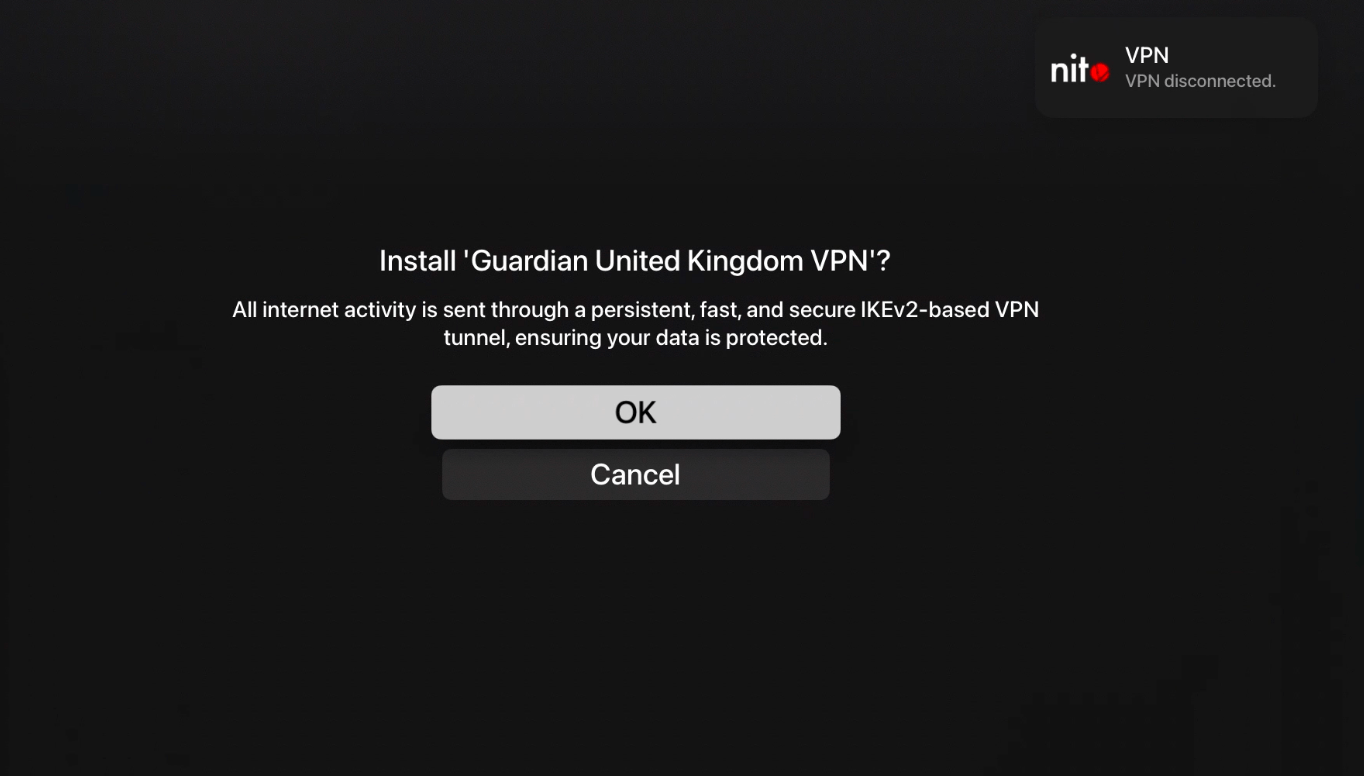
For a company that appears to tout privacy as much as they do, it’s both astounding and questionable as to why Apple doesn’t permit VPN functionality on its Apple TV platform out of the box. Fascinatingly, VPNs can be installed and used on almost every other Apple device aside from the Apple Watch, including the iPhone, iPad, iPod touch, and even the Mac.
There’s no question that this silly limitation has brushed some Apple TV users the wrong way. On the other hand, there may be hope for those holding out. In a teaser Tweet shared this Thursday afternoon, Guardian Firewall founder and CEO Will Strafach said that the first VPN (and firewall) for tvOS is in the works and could be released for jailbroken Apple TVs in the future:

One of the things that makes the checkra1n jailbreak unique is that it’s bootrom-based, which means that it’s able to jailbreak any hardware vulnerable to the checkm8 bootrom exploit. This includes iPhones, iPads, Apple TVs, and even the T2 chip that many modern Mac computers now come equipped with from the factory.
It wasn’t long ago that the checkra1n team baked official support for the T2 chip into their jailbreak tool, and as such, it may come as no surprise that some of the first T2-based hacks are beginning to trickle in. One of the latest of such hacks apparently involves modifying a T2 chip-equipped Mac Mini to play the infamous THX sound during boot-up: