
Apple unleashed iOS & iPadOS 14.2 to the masses yesterday afternoon, and while most iPhone and iPad owners gleefully updated to take advantage of more than 100 new Emojis and six new wallpapers, the updates also appeared to beef up their respective platforms’ security.
Security improvements are generally a good thing for users; however, they can be red flags for proponents of the jailbreak community since software exploits are the very things that make jailbreak tools possible. With that in mind, it may come as no surprise that jailbreak developers repetitiously remind the community to stay in the lowest possible firmware, as this can increase one’s chances of jailbreak eligibility.
That rule of thumb couldn’t be more aligned with this week’s iOS & iPadOS 14.2 releases. Apple’s own “About the security content of iOS 14.2 and iPadOS 14.2” web page cited at least 24 instances of bug fixes, many of which could have resulted in arbitrary code execution. One in particular, a kernel bug dubbed CVE-2020-27905, received quite a bit of attention in the jailbreak community in the past 24 hours, and for good reasons.
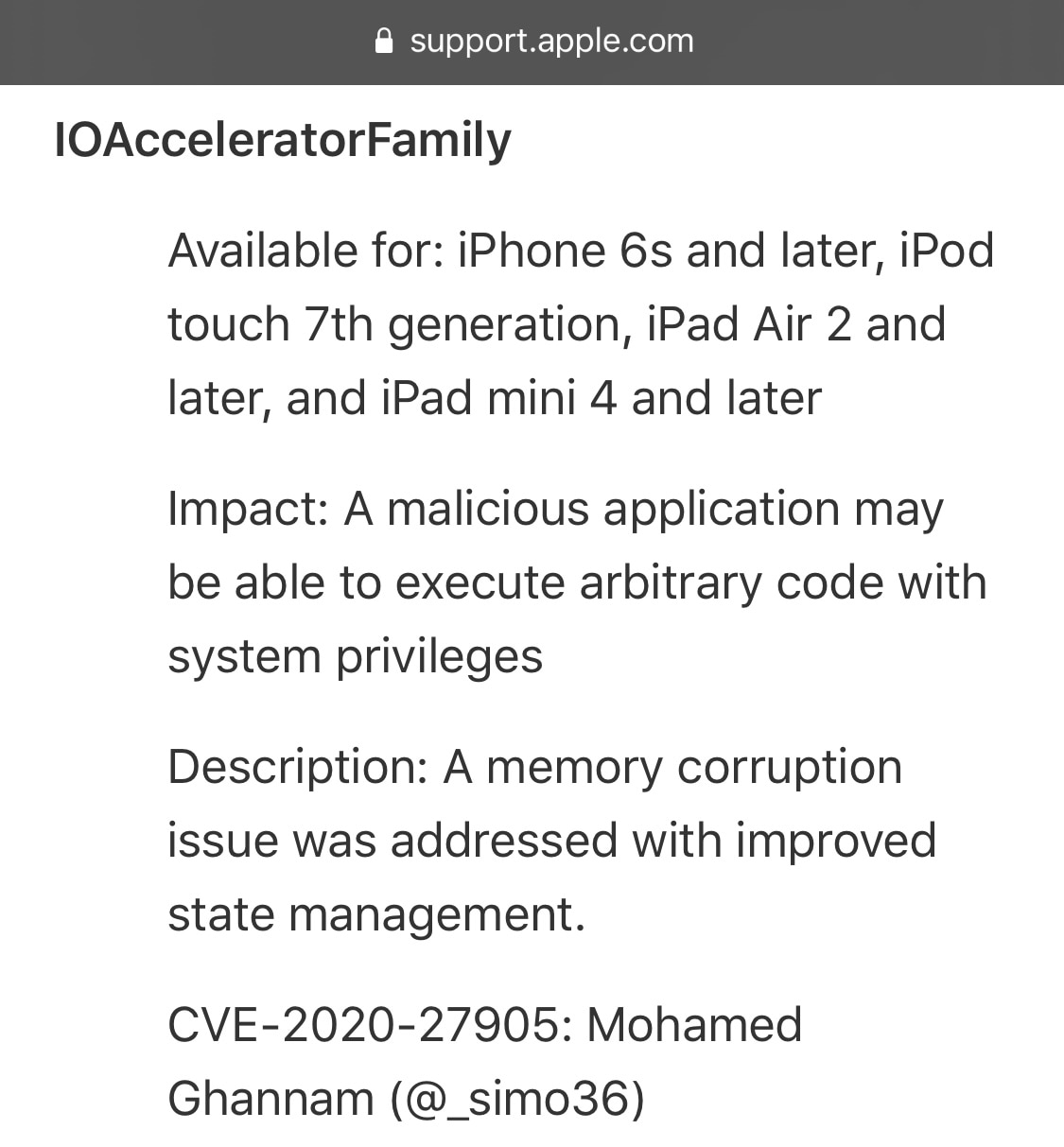
Mohamed Ghannam (@_simo36), the individual responsible for discovering the aforementioned kernel bug, shared a proof of concept (PoC) on Twitter Thursday evening, noting that it was “reachable from within the sandbox:”

What we can tell at first glance is that this shared PoC was patched in iOS & iPadOS 14.2, but that it supports iOS & iPadOS 14.1 and below. Further, it’s merely a kernel bug in its current state, which isn’t the same as a kernel exploit. With a bit more work, a kernel exploit could be developed from this kernel bug, and according to the remainder of the Tweet, it appears to be Ghannam’s intention to develop and release said kernel exploit at a later date.
So what does this mean for the jailbreak community? Well, nothing… yet. A jailbreak tool like Odyssey and/or unc0ver can’t be updated to support up to iOS & iPadOS 14.1 unless a full-blown kernel exploit for these versions exists, and it doesn’t yet; this PoC is merely a kernel bug. If a kernel exploit becomes of this bug, then that would change everything, especially if Ghannam releases it as we’ve been led to believe.
For what it’s worth, this isn’t the first time that Ghannam has been at the forefront of an iOS/iPadOS kernel bug PoC. The last instance involved iOS & iPadOS 13.3.1 and transpired back in March.
While there’s no guarantee that a kernel exploit will materialize from this, much less that a jailbreak tool will add support for it, it still raises hope for a lot of people who might be trying to decide whether they should continue running iOS 14.0-14.1 or update to yesterday’s iOS & iPadOS 14.2 release. If jailbreaking is at all important to you, then we’d advise avoiding the latter and staying on whatever earlier version of iOS 14 you might be running.
Those interested in learning more about Ghannam’s kernel bug can visit its dedicated GitHub page.
Are you excited to learn that a kernel exploit for iOS & iPadOS 14.1 and below could be released in the future? Discuss your position in the comments section down below.