
If you’ve been paying any attention to the iOS & iPadOS security research side of things recently, then you might’ve caught wind about a kernel bug discovered by Mohamed Ghannam (@_simo36) that held the capacity to pwn iOS & iPadOS 14.1 and below. Unfortunately, Ghannam later revealed that the bug didn’t work on iOS or iPadOS 14, and instead that it would only support variants of iOS & iPadOS 13.
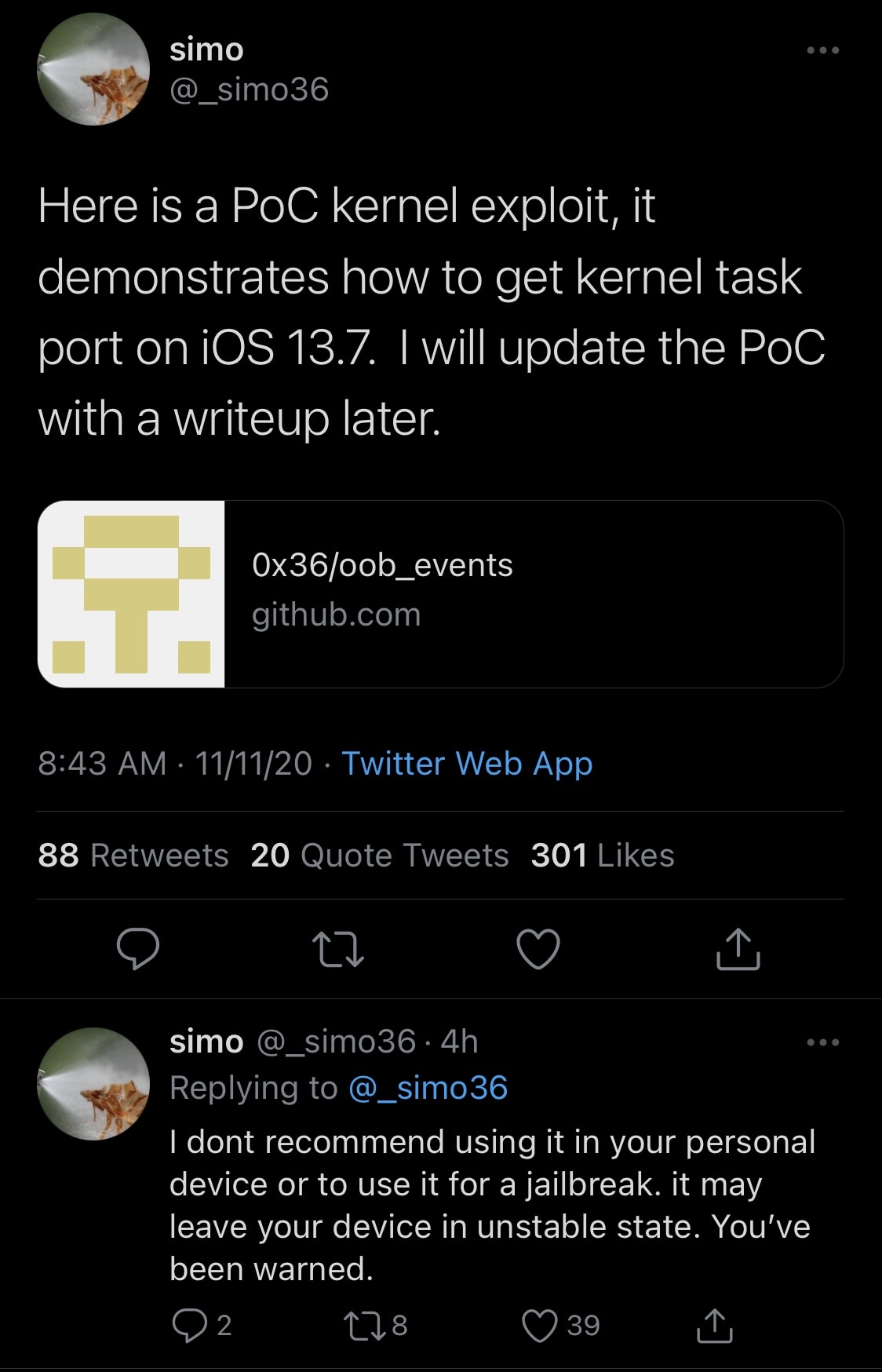
While the aforementioned circumstances were indeed a bummer for those who’d been looking forward to a potential exploit release for iOS & iPadOS 14, the good news is that Ghannam officially released a kernel exploit proof of concept (PoC) dubbed ‘OOB Events’ on Wednesday with instructions for achieving kernel task port (tfp0) on iOS & iPadOS 13.7:
For those unaware, tfp0 or kernel task port enables arbitrary reads and writes to the device’s kernel memory, which is essential in the process of jailbreaking.
So what does this mean for the state of the jailbreak community? A good question, but the answer could perhaps be more convoluted than it seems at first glance. In a somewhat bittersweet follow-up Tweet, Ghannam noted that he wouldn’t recommend using the exploit on a personal device or for a jailbreak because it could potentially ‘leave the device in an unstable state.’
From what we can gather, the exploit isn’t quite as reliable as many would like for a public jailbreak. It can purportedly result in arbitrary kernel panics, and it would need a lot more work to enhance the stability across Apple’s diverse device lineup.
Does this mean it would be impossible to improve this exploit? Absolutely not, but it would necessitate someone to put a lot of additional time and effort into improving the exploit. Renowned hackers and security researchers in today’s jailbreak community such as Jake James have been known to modify and improve exploits for enhanced compatibility and/or stability; however there’s no telling if James or another individual with this talent will take the same steps for this exploit.
One thing worth noting, however, is that Ghannam’s latest exploit supports up to iOS & iPadOS 13.7, which is notable since the public software-based jailbreaks of today like Odyssey and unc0ver only support up to iOS & iPadOS 13.5 at the time of this writing. Another jailbreak supporting up to iOS & iPadOS 13.7 is allegedly in the works, but by another and unrelated group of individuals entirely dubbed FreeTheSandbox.
It will indeed be interesting to see what becomes of the new exploit, as there’s no telling whether or not someone might be able to develop a jailbreak from it. If we’re lucky, then someone might be able to enhance its stability. At worst, nothing becomes of it and we wait for another exploit or jailbreak to drop. Whatever happens, it’s important to remember to keep your device on the lowest possible firmware if you intend to increase your changes of jailbreak eligibility in the future.
Those interested in checking out Ghannam’s OOB Events exploit PoC for iOS & iPadOS 13.x can head over to the official GitHub page.
Are you excited to see what happens? Let us know in the comments section down below.