A bug affecting iOS & iPadOS versions 15.x-16.1.2 and macOS 13.0.1 called CVE-2022-46689, also codenamed MacDirtyCow, has been making headlines recently. This bug was discovered by security researcher Ian Beer of Google Project Zero, and while it’s not being used in any jailbreaks, it does appear to be at the epicenter of some interesting hacks for modding iPhones and iPads recently, such as TrollLock Reborn.

Since these mods are akin to jailbreak tweaks in many ways, this raises questions about what MacDirtyCow is and what else it might be capable of. Obviously, the bug itself isn’t a jailbreak, but it’s powerful enough to permit mods that shouldn’t be allowed to run on an iPhone or iPad. If this all sounds familiar, that’s because a CoreTrust bug exploited by TrollStore allows similar hacks and add-ons to be used without a jailbreak.
So what exactly is MacDirtyCow, and what is it capable of? That’s a good question, and more information may soon reveal itself.
At face value, MacDirtyCow appears to allow whoever might be using it to write to all files that a sandboxed app can access on the device itself. These aren’t our words, but rather the words of TrollStore developer opa334, who took to /r/jailbreak to explain what this hack might be capable of.
One important takeaway is that the exploit is quite limited in what it can accomplish, and another caveat is that changes aren’t permanent. For example, the exploit only allows information to be written to cached data in the affected device’s memory (RAM), which means that any changes will revert with a simple reboot because RAM is a type of volatile memory and as such loses its integrity with loss of power.
So what does this all mean? In essence, it means that you can make minor mods to your iPhone or iPad on a firmware that is affected by the MacDirtyCow bug, but they will only last so long as the device remains powered on. Once you reboot that device, you’ll have to reapply any relevant mods.
TrollLock Reborn, for example, allowed the Lock Screen’s Face ID padlock to be themed with alternate icons. In the case of this specific add-on, an animated troll face was used. TrollLock Reborn would be sideloaded onto a supported iPhone or iPad by way of software such as AltStore or Sideloadly, which means that the sideloaded app would remain signed for as long as seven days before having to be re-signed again.
Worthy of note, other MacDirtyCow-supported add-ons also exist, or are already in the works. For example, software developer Zhuowei Zang published a writeup for a MacDirtyCow demo on GitHub and shared it to Twitter, and soon after publishing that, made a proof-of-concept app called WDBFontOverwrite that appears to be capable of modifying system fonts on an iPhone or iPad. That project is also available on the developer’s GitHub page.
The WDBFontOverwrite app can currently apply the following font styles to an iPhone or iPad without a jailbreak:
- DejaVu Sans Condensed
- DejaVu Serif
- DejaVu Sans Mono
- Go Regular
- Go Mono
- Fire Sans
- Segoe UI
- Comic Sans MS
- Choco Cooky
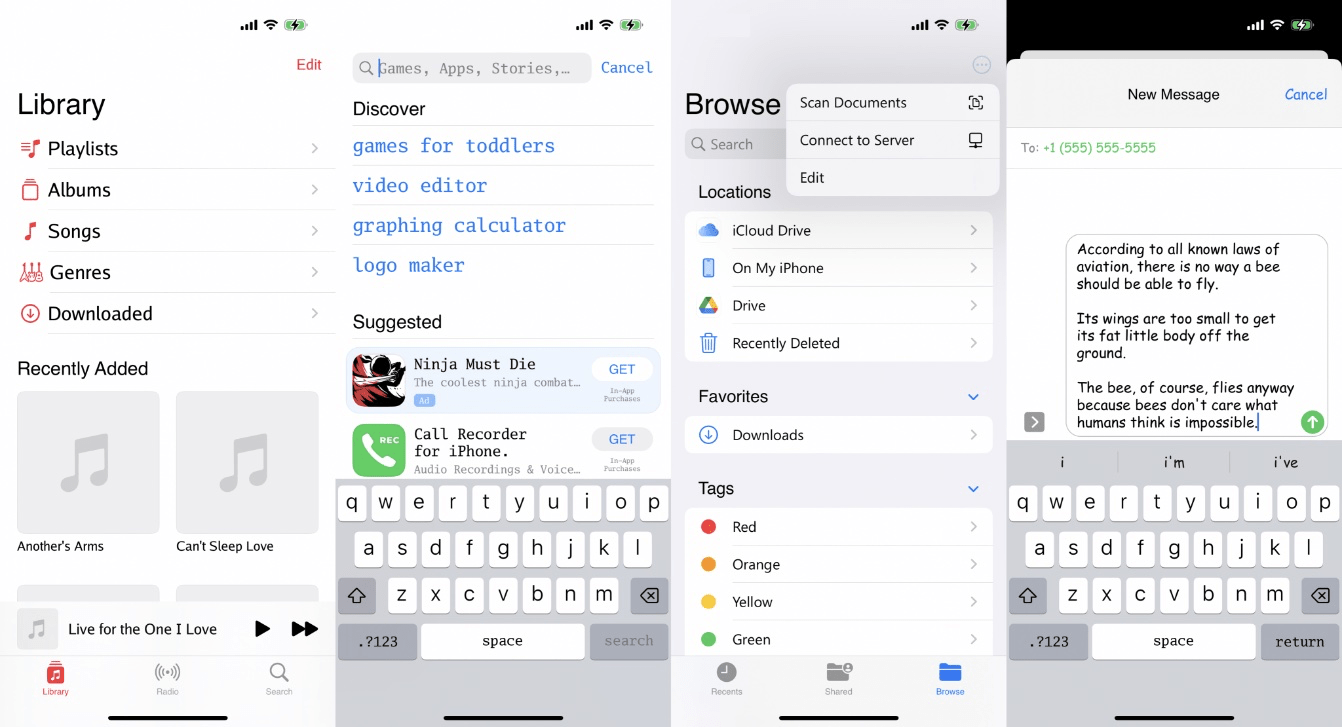
This concept is especially interesting, as changing a device’s system font is a common trait of jailbreaking an iPhone and using the BytaFont jailbreak app and a compatible font file. Without a jailbreak, this means that MacDirtyCow can make similar changes that are easily reversed with nothing more than a reboot.
Ian Beer has yet to publish a full write-up about CVE-2022-46689, also currently known as MacDirtyCow, but it would be interesting to see if his version is any more capable than the demo currently floating around. Additional projects made almost entirely dependent on this bug are being released and/or worked on at the time of this writing, so it will be interesting to see what else materializes from it all.
Do you plan to take advantage of any MacDirtyCow bug-related add-ons on your iPhone or iPad running iOS or iPadOS 15.x-16.1.2, or have you already updated to version 16.2? Let us know in the comments section down below.