The Odyssey Team has been investigating the feasibility of the new iOS & iPadOS 15.0-15.1.1 kernel exploit for an upcoming semi-untethered jailbreak tool, and many prospective jailbreakers are undoubtedly anxious to see what happens next.

Many are especially anxious after utilizing the DelayOTA and futurerestore methods to upgrade to iOS & iPadOS 15.1 or 15.1.1 despite the fact that these firmware versions are no longer officially signed by Apple. These users are essentially stuck in place and waiting for some new jailbreak development.
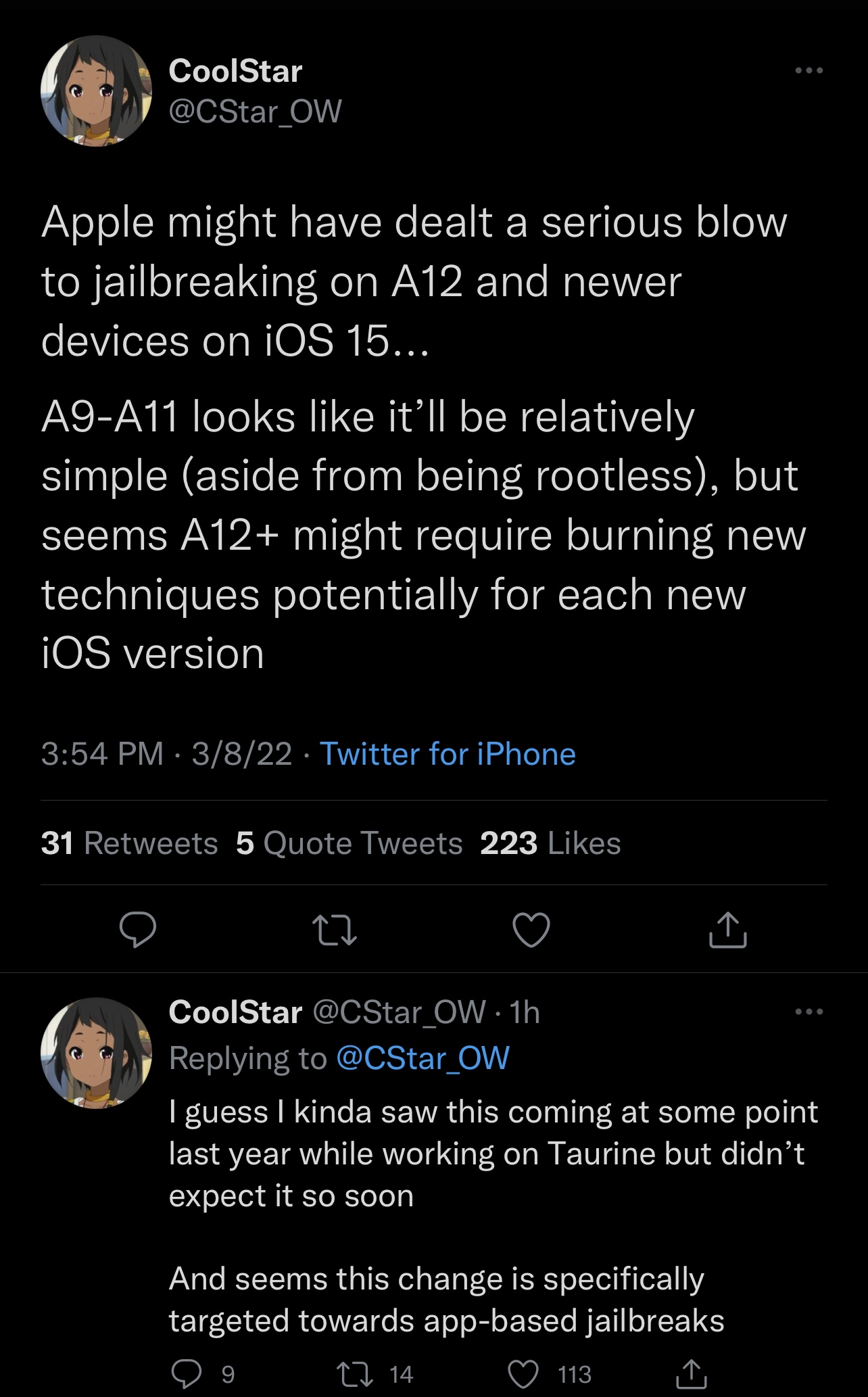
In a series of Tweets shared this week, Odyssey Team lead developer CoolStar shared some insight into the matter, and it may surprise you.
There’s good news if you’re wanting to jailbreak an A9, A10, or A11-equipped handset on iOS or iPadOS 15, because it seems that creating a jailbreak would be particularly straightforward on these devices apart from switching to a rootless bootstrap.
If you have an A12 or newer device on iOS or iPadOS 15, however, then this is where things allegedly become trickier.
CoolStar says that because of changes made by Apple, presumably to target app-based jailbreaks like Taurine and unc0ver, jailbreak developers may potentially need to burn new techniques — that is, the method of attack — for every version of iOS or iPadOS that the jailbreak plans to support.
While this doesn’t mean that iOS & iPadOS 15 would be unjailbreakable on A12 and newer devices, it does mean that jailbreak developers would need to work harder to maintain jailbreaks for such devices as exploits drop for newer versions of iOS & iPadOS. Obviously, this poses its own challenges, as exploits and security mechanism bypasses have been particularly few and far in between lately.
Jailbreakers are no stranger to Apple’s continuous cat-and-mouse game with jailbreaking, however Apple’s efforts to clamp down on jailbreaking certainly appear more amplified in recent years, especially with respect to modern handsets running newer firmware.
Even the checkra1n jailbreak is seeing turbulence in being updated for iOS & iPadOS 15, as Apple’s secure system volume (SSV) protection means that the checkra1n jailbreak also needs to utilize new techniques to avoid disruption. This has no impact, however, on the unpatchable checkm8 hardware-based bootrom exploit, which remains viable even on iOS & iPadOS 15.
So while Apple certainly seems to have made things more challenging with iOS & iPadOS 15, this wouldn’t be the first time. Apple seems to make things tougher year after year, and yet the community continues to prevail.
It will be interesting to see what becomes of the new iOS & iPadOS 15.0-15.1.1 exploit, especially as more hands get involved in the pot.