Brightiup’s CVE-2021-30955 kernel bug for iOS & iPadOS 15.0-15.1.1 has received tons of publicity lately after two prestigious security researchers including Jake James and @Peterpan980927 each went hands-on to develop proof-of-concepts (PoCs) based on the original write-up, which didn’t come with a PoC of its own.
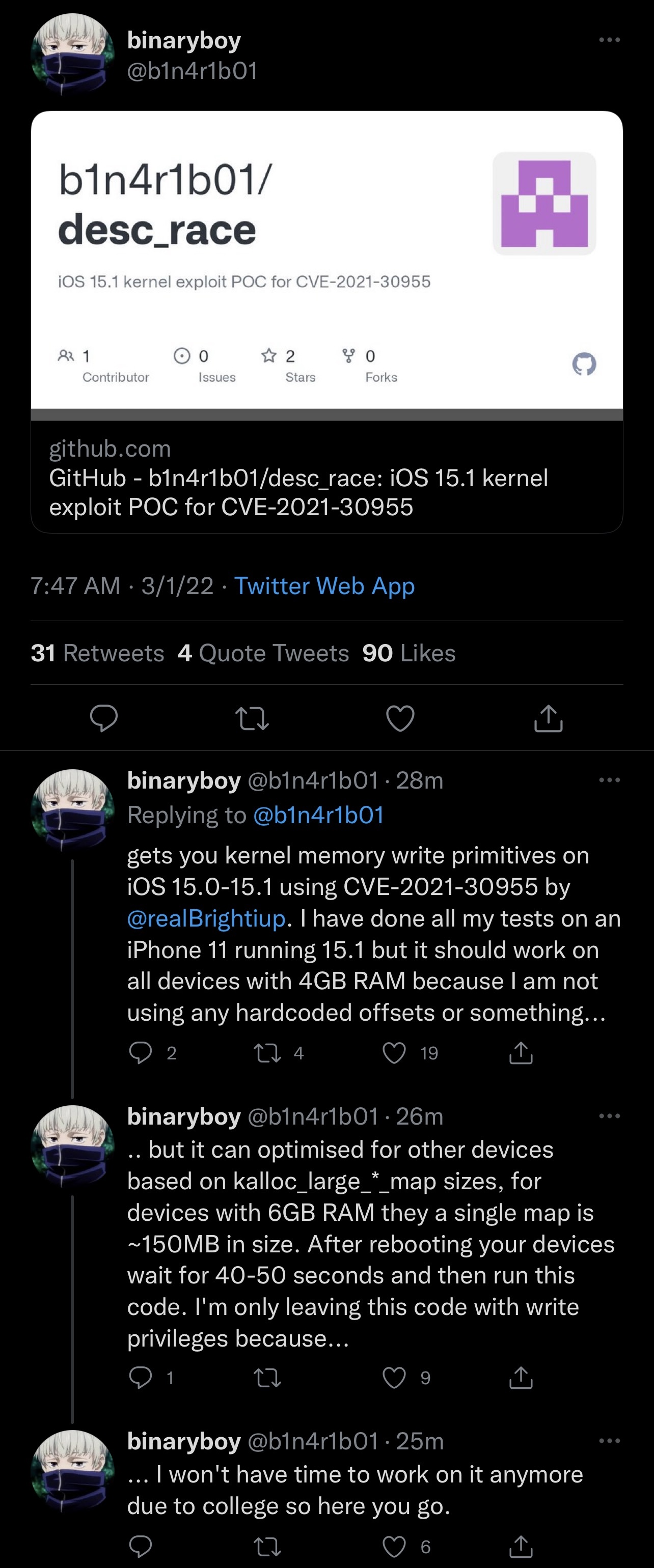
As of Tuesday morning, another progression was made after hacker @b1n4r1b01 published what appears to be a full-blown iOS & iPadOS 15.0-15.1.1 exploit proof of concept dubbed desc_race based on Brightiup’s kernel bug.
What makes @b1n4r1b01’s PoC different from the two other hackers’ PoCs is that this one is actually a full exploit that, according to @b1n4r1b01, grants the user with kernel memory write primatives on handsets running the affected firmware versions.
@b1n4r1b01 went on to explain that all initial tests were made using an iPhone 11 running iOS 15.1, but it should play nicely with all handsets equipped with at least 4GB of RAM. It was also explained that the exploit could be optimized for other devices and that @b1n4r1b01 won’t have the time to make those optimizations, which puts the ball in someone else’s court to do exactly that.
The new exploit PoC is available on @b1n4r1b01’s GitHub page.
Jake James, the hacker who made and published a PoC on the same CVE-2021-30955 kernel bug by Brightiup just yesterday, Tweeted that @b1n4r1b01’s exploit PoC “should be enough to get jailbreak developers going,” which is excellent news for anyone waiting for an iOS or iPadOS 15 jailbreak:
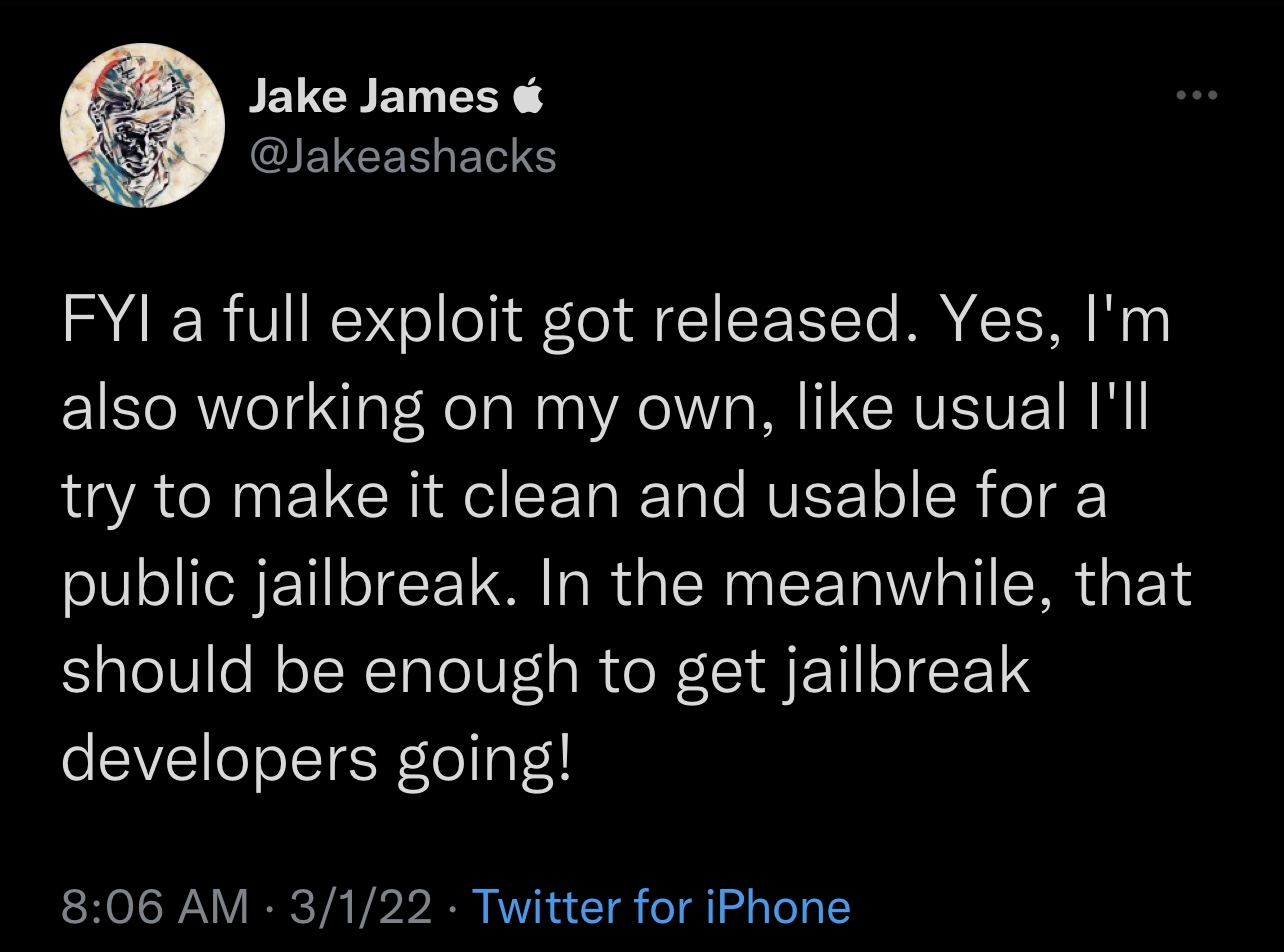
James also said he was working on his own exploit in the meantime.
So when should we expect an iOS & iPadOS 15 jailbreak? Well now that we have an exploit for iOS & iPadOS 15.0-15.1.1, jailbreak developers can start working on one, however it won’t happen as quickly as iOS & iPadOS 14 jailbreaks did because there’s are a lot of new security mitigations in iOS & iPadOS 15 that will require circumventing.
For example, iOS & iPadOS 15’s secure system volume (SSV) security mechanism makes it substantially more challenging to tap the root filesystem, which means semi-untethered jailbreaks such as unc0ver would likely need to be rootless, and therefore require an entirely different bootstrap. This shouldn’t impact the usability of most jailbreak tweaks, however.
It’s worth noting that the checkra1n team is trying a different approach and using bind mounts instead of union mounts, and that they will attempt setting up a separate volume for all things that can’t be bind-mounted. This should get around having to go rootless, but it remains to be seen if similar methods could be used for other jailbreaks. Checkra1n only supports A7-A11-equipped handsets due to the checkm8 hardware-based bootrom exploit present on those devices. Because of this, it can’t be patched by Apple.
Now that we have a working exploit for iOS & iPadOS 15.0-15.1.1 in the wild, it should be interesting to see what happens next. Of course, we’ll be closely watching James’ work as he says he’s working on an exploit of his own.
Are you excited for what may happen in the foreseeable future? Let us know in the comments section down below.