Yesterday, Apple seeded its registered iOS developers with a so-called Gold Master version of iOS 7, which is essentially the same version owners of iPhone, iPod touch and iPad devices will be getting come September 18.
Unfortunately, it seems the company has quietly pulled the useful iCloud Keychain feature from the GM build. The company did not provide an explanation as to why exactly the feature got yanked.
For what it’s worth, it’s entirely possible the company leadership didn’t feel confident enough to declare iCloud Keychain ready for prime time. We have another theory…
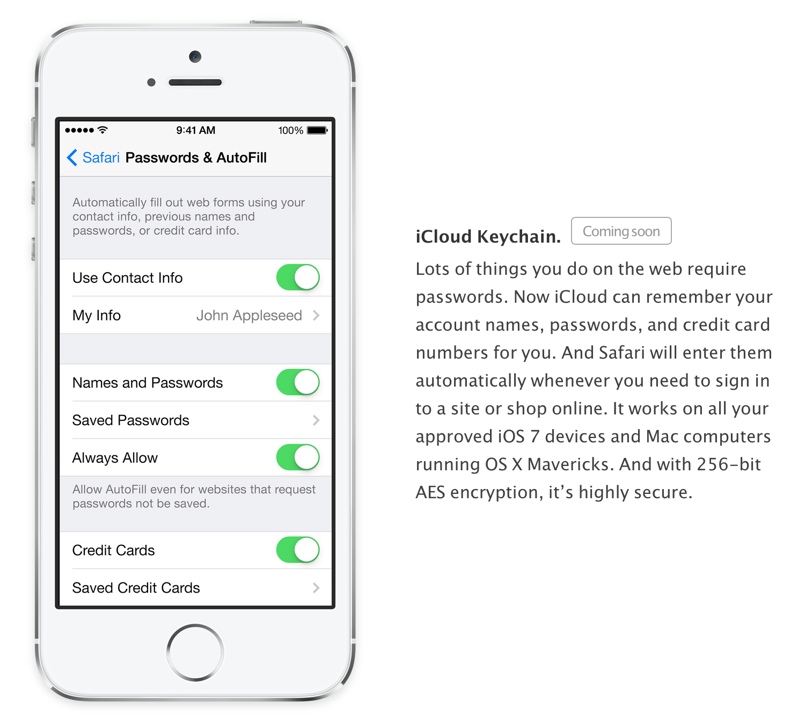
Advertised as a simple way to sync all your stored passwords across devices, iCloud Keychain worked in tandem with iOS 7 Safari by offering to save (and even generate) passwords people use to log in to websites such as eBay and Facebook.
iOS 7 GM still lets you save passwords locally to your keychain (Settings > Safari > Passwords & Autofill), but you won’t find the option in Settings > iCloud > Keychain to sync your saved passwords across devices.
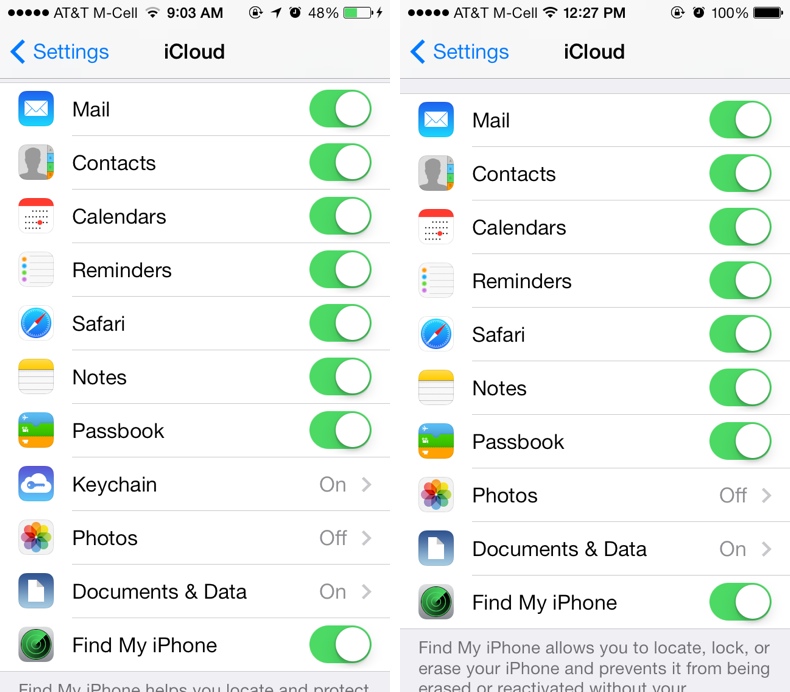
Here’s iOS 7 Beta 7 with iCloud Keychain (left) and the GM build without it (right).
MacRumors was quick to point out that iCloud Keychain is a goner in the iOS 7 GM build. Interestingly enough, Apple has updated the iOS 7 web page with the “coming soon” label next to the iCloud Keychain description.
In addition to web site logins, iCloud Keychain also syncs stored credit card information across devices so it’s possible the company temporarily removed the feature to avoid any potential security breaches.
With the advent of fingerprint scanning that debuted on the iPhone 5s, Apple must take extraordinary measures to keep customer data safe from prying eyes and not compromise their security (that’s NSA’s job). Apple’s execs during yesterday’s keynote frequently repeated that fingerprint data is stored on a secure module on the new A7 chip that only the Touch ID chip is allowed to access.
“It’s never stored on Apple servers or backed up to iCloud,” Apple’s press release assures. “All fingerprint information is encrypted and stored securely in the Secure Enclave inside the A7 chip on the iPhone 5s,” the company underscores.
In addition to unlocking your device without having to punch in a passcode, Touch ID on the iPhone 5s can also be used as a secure way to approve purchases from the iTunes Store, App Store or iBookstore.
Here’s Touch ID in action.
http://www.youtube.com/watch?v=qaAEcp52Ekc
We have every reason to believe that Touch ID will soon work with website passwords and perhaps even in-app passwords so perhaps Apple removed iCloud Keychain until Touch ID support for website/app passwords is properly implemented.
Also, as some noted on Twitter, they may be waiting for Mavericks.
Whoever writes the jailbreak tweak that steals fingerprint ID stored securely on the iPhone 5s A7 chip gets to land a job with NSA
— Christian Zibreg (@dujkan) September 11, 2013
There has been some commotion on Twitter concerning the potential for a rogue app or web site to steal your fingerprint ID. Now, I’m not a security expert, but I’m pretty sure Apple means business when it says only Touch ID can match your fingerprint to the data securely stored inside the A7 chip.
The most third-parties can hope for is an iOS 7 API for fingerprint authentication which I’m pretty sure won’t allow developers to ever touch your fingerprint data. As for websites, there’s no way a remote server could steal your identity because (at least in in theory), a server such as Amazon doesn’t need to know anything about fingerprint scanning – it simply puts up a standard web login form.
The only way to bypass the iPhone 5s Touch ID that I know of is this.
iOS 7 then recognizes the password prompt and ask you to authenticate using your finger – again, theoretically speaking.
Upon successful authentication, iOS 7 would then retrieve your Amazon login information previously stored in the iOS keychain (and synced to other devices via iCloud Keychain) and log you in – much like 1Password on steroids.
If you’re eager to learn more about the implications of using fingerprints versus traditional passwords, I wholeheartedly recommend Mark Burnett’s excellent write-up.