Unlike the malware-infested Android, Apple’s mobile platform is mostly malware-free. Little wonder that Apple prides itself with reviewing apps “to guard against malware” while asserting that other mobile platforms pose a “security risk”.
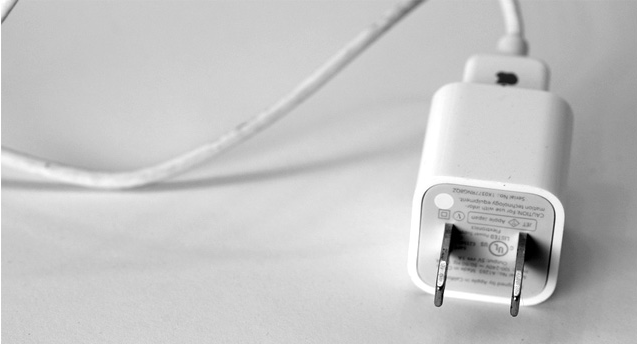
But what if malicious users could hack your iPhone via a specially built charger – and in less than a minute? That’s exactly what three researchers at the Georgia Institute of Technology claim is possible as they prep to show off a proof-of-concept charger which can be used to invisibly install malware on non-jailbroken iOS devices…
According to Forbes, the results of the experiment have been called “alarming”.
The malicious charger, called Mactans, is built around an open-source single-board computer known as a BeagleBoard, sold by Texas Instruments for a retail price of around $45.
The exploit lets an attacker hide their software “in the same way Apple hides its own built-in applications,” reads the description.
Forbes explains:
The researchers write that their attack can compromise an iOS device running the most recent version of Apple’s mobile operating system in less than a minute. They add that they can also demonstrate that the malware infection resulting from their malicious charger is persistent and tough to spot.
“This hardware was selected to demonstrate the ease with which innocent-looking, malicious USB chargers can be constructed,” the researchers write.
They contacted Apple about their findings, but have yet to hear from the company. The researchers will show off their proof-of-concept charger at the upcoming Black Hat security conference in late July.
An attacker wouldn’t necessarily need to get hold of your device in order to break into it.
For instance, a shady organization with a budget could replicate Apple’s charger and shrink a three-inch square BeagleBoard to fit inside, or even hide the board inside a third-party docking station or external battery.
And with mobile chargers increasingly popping up in places like airports, you have a recipe for a disaster (not that Apple won’t soon fix the exploit, mind you).