Every year, there are handful of meets around the world where experienced hackers can speak and share their knowledge with others to forward the essential skill that is security research.

Every year, there are handful of meets around the world where experienced hackers can speak and share their knowledge with others to forward the essential skill that is security research.

There’s a lot going on in the jailbreak community as of right now. Not only is the checkra1n team actively attempting to jailbreak iOS & iPadOS 14 on many more devices, but hacker and security researcher @08Tc3wBB may also soon share details about an exploit viable for jailbreaking iOS & iPadOS 13.7 (the last versions of Apple’s previous-generation mobile operating systems).
If you find yourself more interested in the latter tidbit, which is likely the case if you stayed on the lowest possible firmware after iOS & iPadOS 14 got released, then you might be ecstatic to learn that @08Tc3wBB will present his latest research with security group ZecOps at the Black Hat Europe 2020 event.

Apple is predicted to unveil a macOS bounty program at the upcoming Black Hat security conference which takes place in Las Vegas, Nevada later this week, Forbes reported today.

You can now watch Apple's 'Behind the Scenes of iOS Security' presentation from this year's Black Hat Conference in its entirety. A video of the talk, featuring the company's head of security engineering Ivan Krstic, has been posted to the official Black Hat YouTube page.
Apple's presence at the conference was a nice change of pace, as the firm typically skips the event. Krstic covered a wide range of topics, including the technologies his team uses in services like HomeKit and iCloud Keychain that handle exceptionally sensitive user data.
If you've followed the jailbreak scene for any extended amount of time, you know that it takes a person with high-level skills to exploit iOS. There's only a handful of people in the world that can do it, and let's just say they're very, very talented.
So it shouldn't come as a surprise that planetbeing—one of the 4 members of the evad3rs—was recognized at this year's Black Hat hacking convention. He took home the Pwnie for privilege escalation, which was used in the evasi0n jailbreak...
Unlike the malware-infested Android, Apple's mobile platform is mostly malware-free. Little wonder that Apple prides itself with reviewing apps "to guard against malware" while asserting that other mobile platforms pose a "security risk".
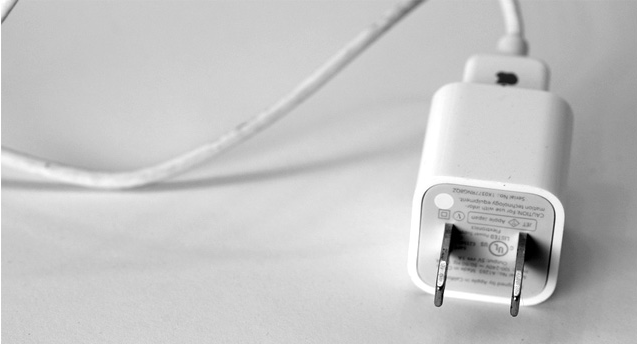
But what if malicious users could hack your iPhone via a specially built charger - and in less than a minute? That's exactly what three researchers at the Georgia Institute of Technology claim is possible as they prep to show off a proof-of-concept charger which can be used to invisibly install malware on non-jailbroken iOS devices...