A report on Monday alleged Apple began rejecting third-party iOS apps that make use of Unique Device Identifiers (UDIDs). Today, developer Paul Haddad confirms that a new build of his Tweetbot app failed to pass Apple's requirements due to its use of UDIDs. Haddad received an email from the company that cites section 17.1 of the App Store Review Guidelines.
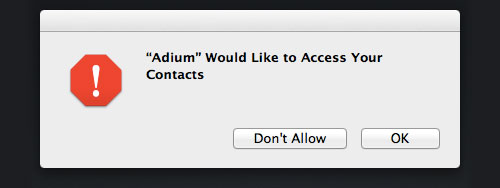
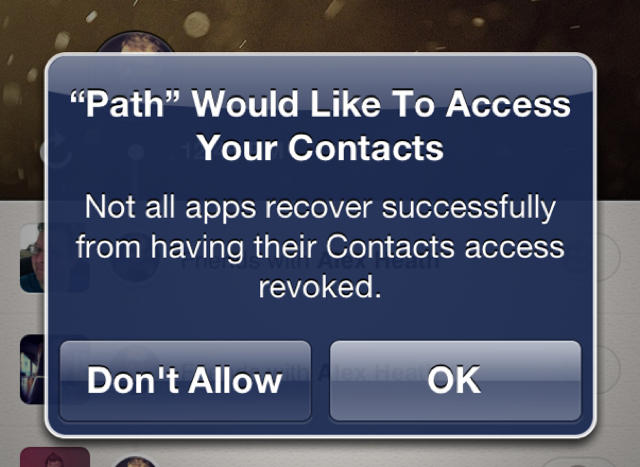
It states “apps cannot transmit data about a user without obtaining the user’s prior permission and providing the user with access to information about how and where the data will be used”.
With this app rejection, I think we can safely conclude that developers are now wise to drop UDIDs from their apps. Better late than never, if you ask me...