ZDNet has just published an interesting report claiming that Apple, along with both RIM and Nokia, has built in backdoor iOS access for the Indian Military, leaving text messages, voice calls, and data trails completely exposed.
As you can imagine, after the recent CarrierIQ scandal, this information is making some waves around the internet. And what’s even worse, it sounds like the hidden trapdoor has been used in some not-so-kosher situations…
A few days ago, word started to spread that Symantec, the makers of Norton AntiVirus and other security software, had been hacked. As it turns out, the group responsible for the attack, the Lords of Dharamraja, has used the knowledge to infiltrate a wide array of highly-classified targets, including Indian Military Intelligence servers. The group has recently started publishing data that it uncovered from the breach, and one of the documents really stands out.
ZDNet’s Manan Kakkar explains:
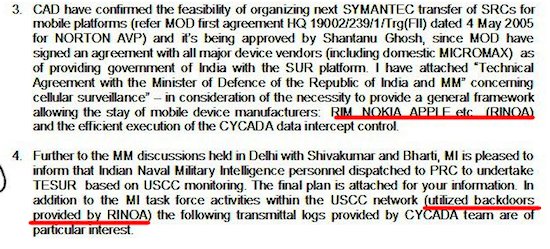
“Earlier today I came across scans of a set of documents that are internal communications between the Indian Military. The documents claim the existence of a system known as RINOA SUR. While I did not find what SUR stands for, RINOA is RIM, Nokia, and Apple. And this is where things start to get very interesting. According to the set of documents, the RINOA SUR platform was used to spy on the USCC — the US-China Economic and Security Review Commission.”
From what we’ve gathered from the documents, and Kakkar’s report, it sounds as though Apple agreed to give the Indian Military access to its communications in exchange for Indian market presence.
We’re not real savvy in International Law, but we’re guessing that spying on the USCC is not ok. We’re also betting that once pro-privacy fighters like Senator Al Franken get wind of this information, there will be a full-blown investigation.
Stay tuned, this could get interesting.
What’s your take on the situation? Is this iOS backdoor really a big deal, or does it all just sound like a bad James Bond movie?