The cat and mouse between Apple and the jailbreak community has been going on for about 6 years now. Every time a new jailbreak tool is released, taking advantage of some holes in Apple's tight mobile operating system, you can bet your shirt that Apple will be quick at patching those holes with a software update.
Sometimes those software updates are released faster than others. For example, it took Apple 43 days to patch a series of vulnerabilities that allowed iOS 6 users to jailbreak their devices using evasi0n. In comparison, it took Apple only nine days to fix the bugs that were exploited by JailbreakMe 3.0.
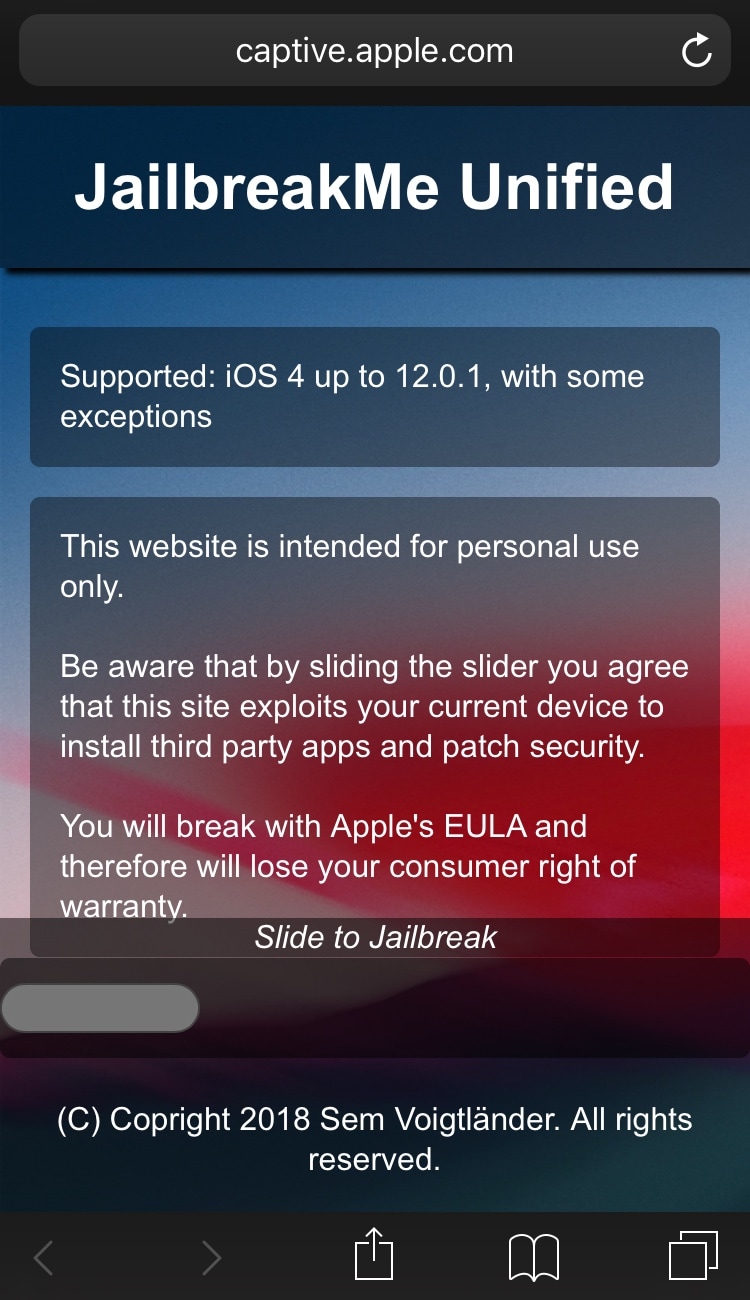
The time difference can be easily explained by the fact that exploits like those used by JailbreakMe represent a much a higher security threat to iOS users than those used in evasi0n. Remember, JailbreakMe could be run directly from the device's browser, thus exposing virtually every single iOS 4.3.3 user at the time to security risks. In comparison, evasi0n requires you to plug the device to a computer via USB. Clearly, the security threats is much lower with evasi0n.
This being said, every time Apple releases a software update that patches vulnerabilities used in a jailbreak, some enthusiastic jailbreakers are always quick at calling Apple names and accusing the company to actively fight the jailbreak community. "Apple hates jailbreakers. They just released a software update to kill the jailbreak," you can often read every time an iOS update that patches a jailbreak is released. But is that really the truth? Does Apple really hate the jailbreak community or is it trying to protect the safety of its most popular operating system?