Today is a day that many avid jailbreakers have waited for. Security researcher Linus Henze gave a much-anticipated talk at the Objective by the Sea security conference in which he demonstrated his Fugu15 jailbreak on an iOS 15.4.1 device using a fascinating JailbreakMe-style Safari-based method to do so.

Safari-based installation
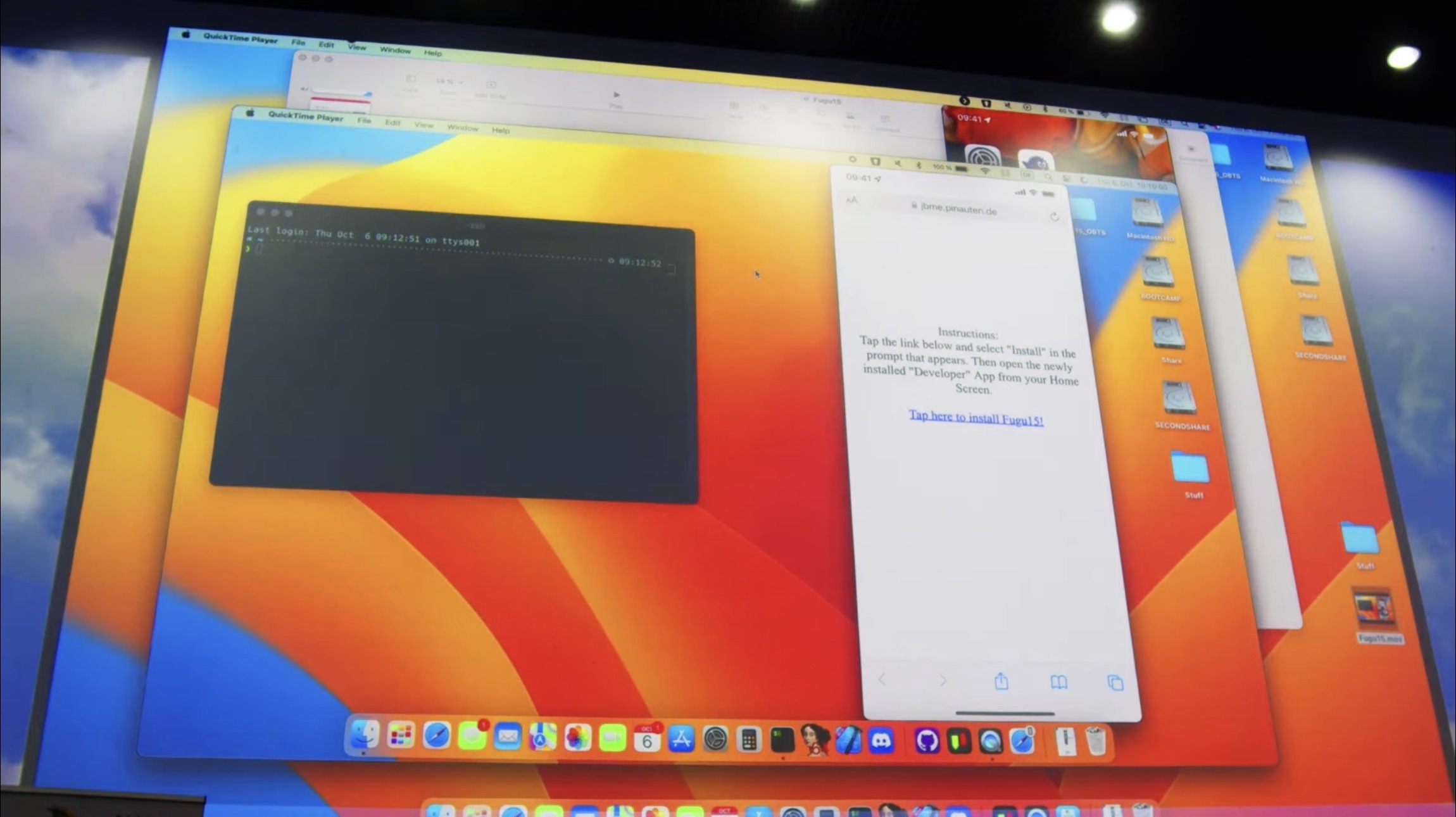
In the demonstration video, Henze navigates to https://jbme.pinauten.de/ in the stock Safari web browser on the iPhone and taps a hotlink on the webpage to initiate the install of the Fugu15 app to the Home Screen:
After Henze confirms the installation via an iOS pop-up prompt, the Fugu15 app downloads to the Home Screen just like an app from the App Store would. When completed, the app icon looks just like the Apple Developer app rather than the Fugu15 app:

Henze explains that the reason for the Apple Developer app appearing on the Home Screen is that he needs a validly signed app to get Fugu15 onto the device. Once that’s completed, Fugu15 can be injected into the app, which happens almost immediately after Henze launches the newly downloaded Apple Developer app:
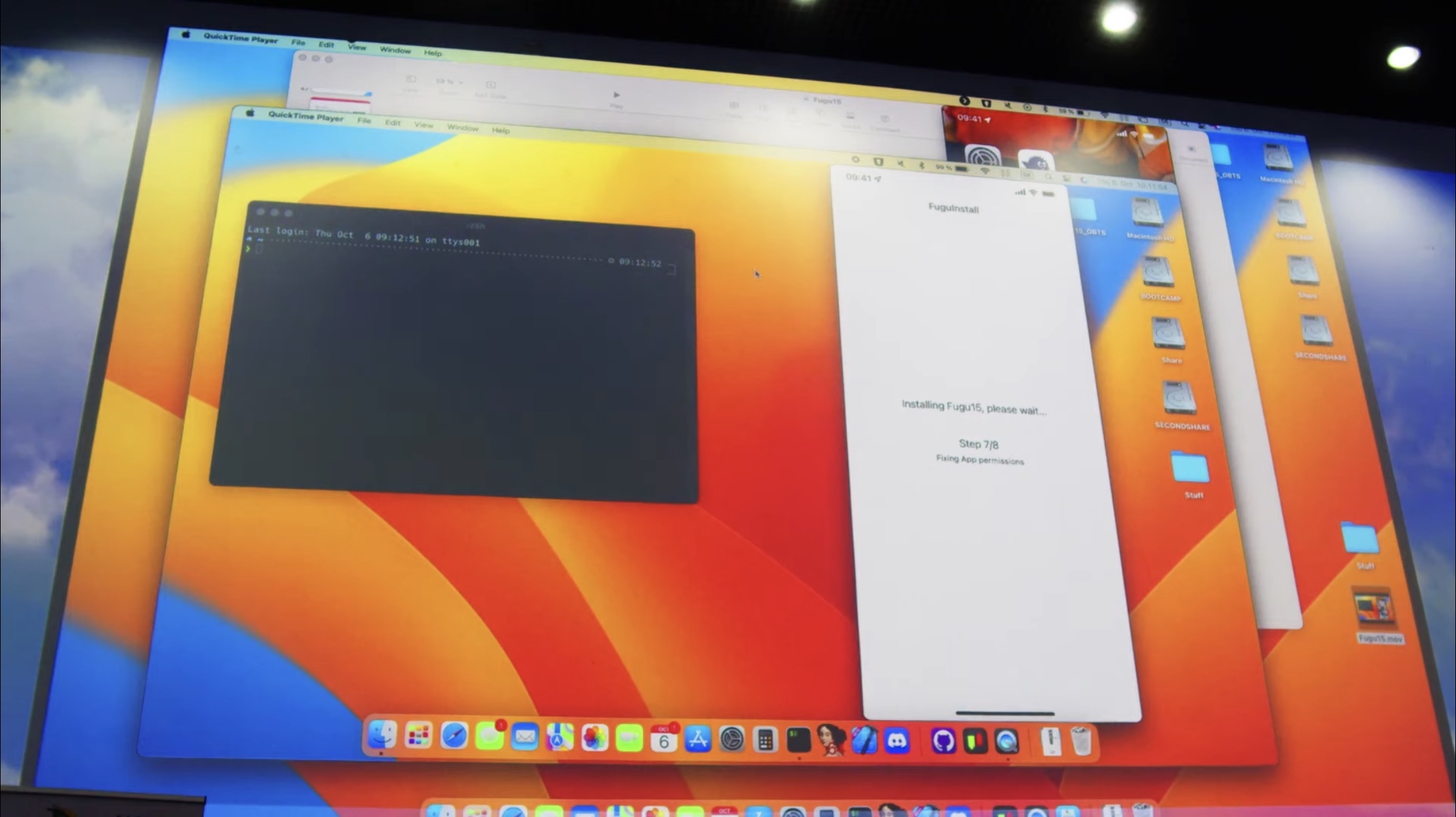
After a short wait, the app prompts Henze to remove the Developer app, which he then does, and doing so leaves the Fugu15 jailbreak app behind.
Smashing the Jailbreak button
In the Fugu15 app, we see a lone Jailbreak button, which Henze happily taps on:
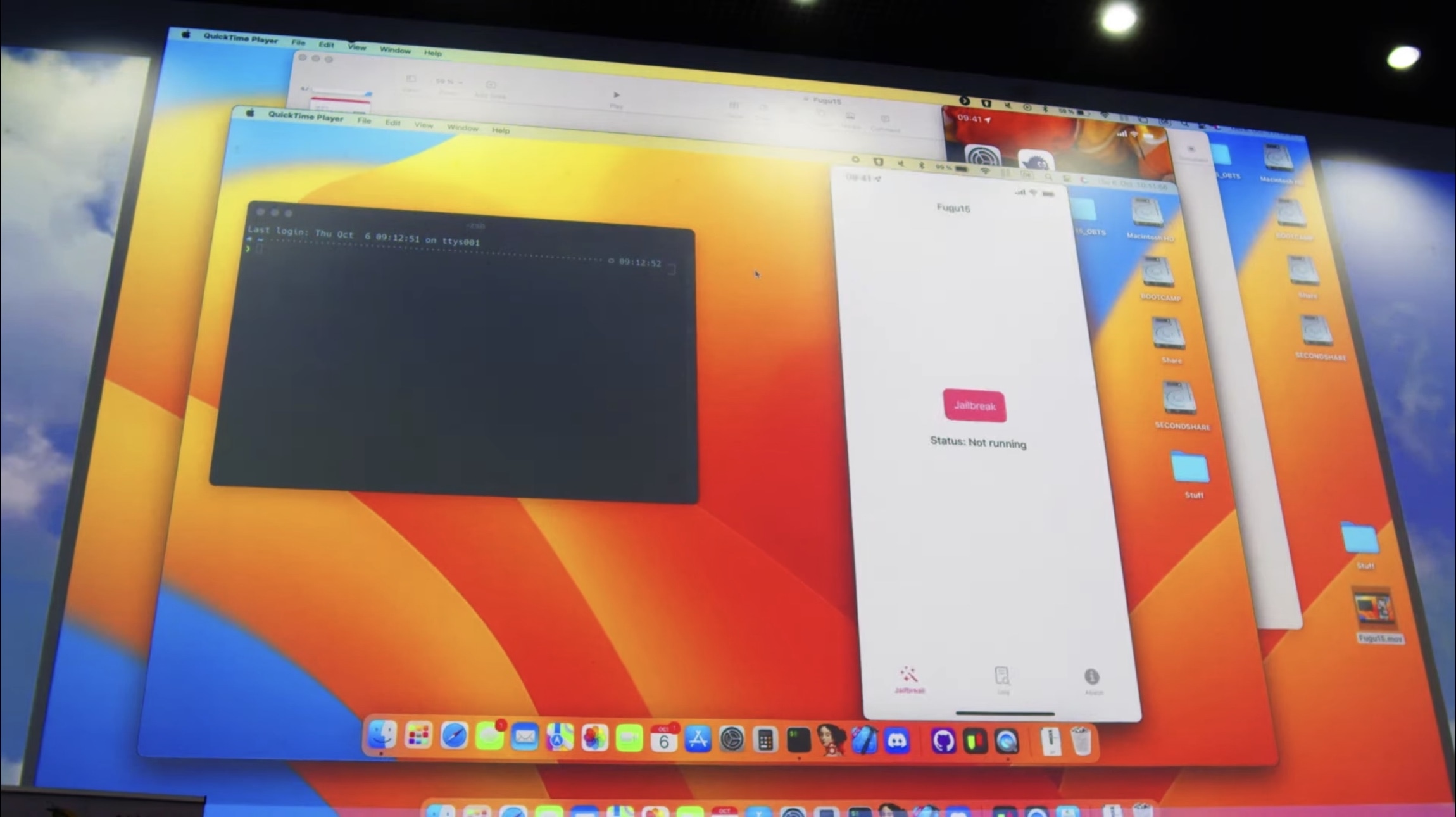
After the jailbreak process completes, Henze switches over to the Log to demonstrate everything that just happened, and then proceeds to Terminal on his Mac to install the Procursus bootstrap.
Sileo and Procursus on Fugu15
Indeed, Fugu15 installs the same Procursus bootstrap used by the Odyssey Team in its Odyssey, Taurine, and upcoming Cheyote jailbreaks, which means the Sileo package manager (not Cydia) will be installed on the device:

Near the end of the demonstration, Henze walks us through Sileo, explaining that there aren’t any jailbreak tweaks to install as of right now because his Fugu15 jailbreak is rootless and jailbreak tweaks aren’t yet updated for compatibility. This warning echoes the same tone expressed by Odyssey Team lead developer CoolStar, who hasn’t yet publicly released Cheyote for the same reason.
Henze’s Fugu15 jailbreak project depends on a CoreTrust bug to sign the Fugu15 jailbreak app and bypass Apple Mobile File Integrity (AMFI). It also appears to harness a Page Protection Layer (PPL)/Pointer Authentication Code (PAC) bypass, along with a bug that permits writing to PPL memory.
At the moment, Fugu15 as it was demonstrated appears to support A12-equipped devices and later running up to iOS 15.5 beta 4, which includes the iPhone XS and newer. Since most users aren’t running betas, this means iOS 15.4.1 is the latest public firmware it supports. Importantly, support for older devices such as the iPhone X and earlier, can be added in the future. Fugu15 is not untethered as Fugu14 on unc0ver was.
Watch the live stream with Linus Henze
The full video live stream of the Objective by the Sea security conference with Henze’s presentation is available on YouTube for those interested in watching it. The demo starts at approximately 1 hour and 59 minutes into the live steam below:
https://www.youtube.com/watch?v=NIyKNjNNB5Q
With no known release time frame for Fugu15 at the time of this writing, it looks like the community will need to continue waiting a while longer for an iOS 15.x jailbreak. But the demonstration was satisfying enough to invoke feelings that great things are just over the horizon whether you’re waiting for the Cheyote release for iOS 15.0-15.1.1 or the Fugu15 release for iOS 15.0-15.4.1.
Were you impressed by Henze’s masterful jailbreak demonstration on iOS 15.4.1? Let us know in the comments section down below.