Nearing around two weeks after security researcher @b1n4r1b01 published a working kernel exploit for iOS & iPadOS 15.0-15.1.1 based on Brightiup’s CVE-2021-30955 kernel bug, another respected hacker now appears to be surfacing with an exploit release.
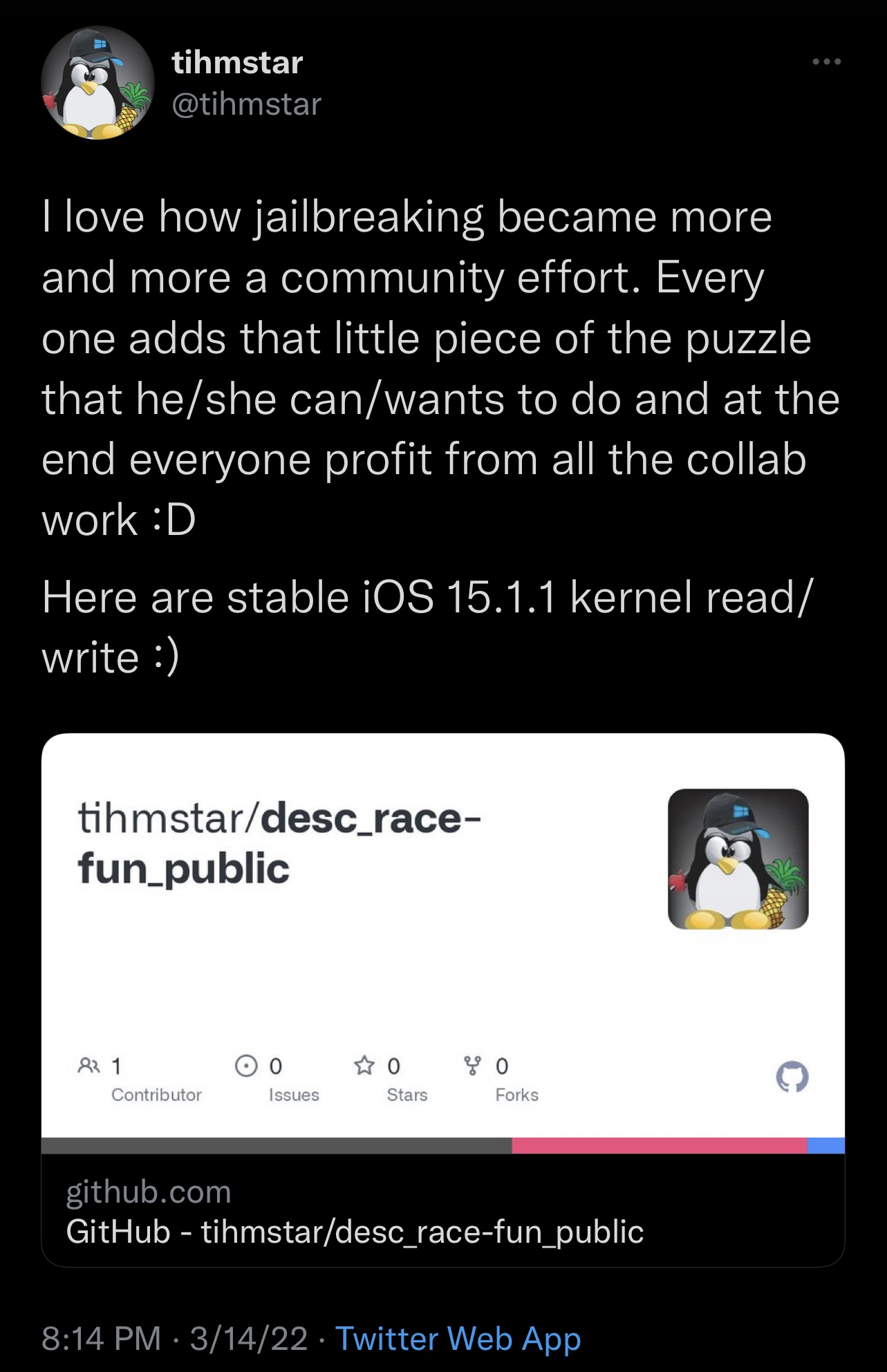
@tihmstar, a name you likely recognize if you’ve been jailbreaking for more than just a couple years, took to Twitterlate Monday evening to share their version of an exploit based on Brightiup’s kernel bug for iOS & iPadOS 15.0-15.1.1.
In the Tweet, @tihmstar praises the way the jailbreak community has been working together as everything begins to come together — such as with one person making a bug, another making a PoC, others continuing to make future improved exploits, and now jailbreak teams working to integrate it into their jailbreak(s).
The Tweet also contains a link to @tihmstar’s GitHub page, which points to their version of an iOS & iPadOS 15.0-15.1.1 exploit entitled desc_race-fun_public, which purportedly features a stable kernel memory read/write.
With yet another working exploit on the table, jailbreak developers have even more tools at their disposal for creating their jailbreaks. Of course, a lot of work still needs to be done since semi-untethered jailbreaks will need to be rootless — this requires re-writing much of the jailbreak from scratch and optimizing the bootstrap for the new changes.
Currently, CoolStar of the Odyssey Team says that the team is working on their iOS & iPadOS 15.0-15.1.1 jailbreak while signaling that A12 and newer devices will take more time due to requiring more security bypasses. A9-A11 devices should be much easier to crack on this firmware, which means a jailbreak for these devices could come sooner.
Are you excited to see various members of the community coming together to make things happen? Let us know your thoughts in the comments section down below.