With all the recent excitement swirling around with respect to Linus Henze’s Fugu14 untether release and the unc0ver jailbreak receiving multiple updates with preliminary support for it, some might say it was easy to forget about a previously-published kernel exploit proof-of-concept by security researcher Saar Amar.

In case you don’t remember, Amar’s kernel exploit proof-of-concept encompassed all the latest versions of iOS & iPadOS 14 and even supported up to and including iOS & iPadOS 15.0.2. While a jailbreak supporting any version of iOS or iPadOS 15 is still a long way off, the proof-of-concept certainly raised hopes of seeing a public jailbreak for some of the latest iOS & iPadOS firmware releases.
Security researcher @pattern_f_ was among one of the first to go hands-on with the kernel exploit proof-of-concept in mid-October when he shared an impressive jailbreak demonstration of his own that allegedly used Amar’s exploit to pwn an iPhone 11 running iOS 14.0. Now, just over two weeks later, he’s at it yet again…
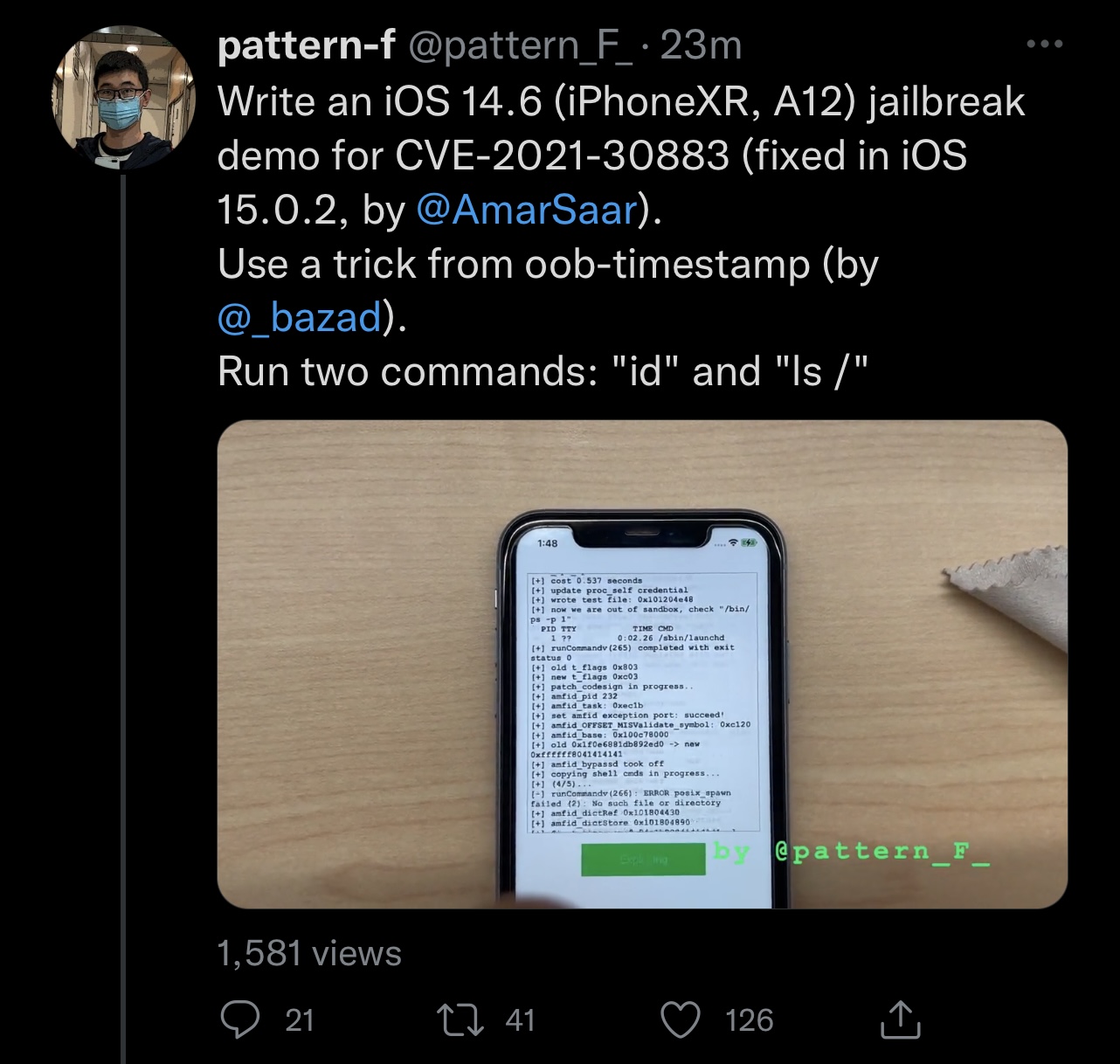
In a teaser video shared via Twitter this Monday afternoon, @pattern_f_ appeared to use the same kernel exploit proof-of-concept by Amar along with a trick borrowed from Brandon Azad’s tried and true oob_timestamp exploit to create yet another jailbreak demonstration, this time featuring an iPhone XR running iOS 14.6.
While it was nothing more than a demonstration, @pattern_f_’s sharing of this video is noteworthy because it reaffirms the possibility of using Amar’s kernel exploit proof-of-concept in existing jailbreak tools such as Taurine and unc0ver to implement support for newer versions of iOS & iPadOS 14.
It’s worth noting that Amar’s kernel exploit covers more device and firmware combinations than Linus Henze’s Fugu14 untether. More specifically, it supports all versions of iOS & iPadOS 14 on most devices except for A14+, or iPhone 12 Pro and newer. On the other hand, Henze’s untether only officially supports arm64e devices (iPhone XS and later) running iOS 14.4-14.5.1 at this time, with the possibility that it could implement support for more devices later on.
In short, while Amar’s kernel exploit isn’t untethered, it would provide for at least a semi-untethered jailbreak solution on most device and firmware combinations.
Now that we’ve seen the power of Amar’s kernel exploit first-hand, it should be interesting to see whether it goes on to support further jailbreak development or not. After all, there are many iOS & iPadOS 14 users who aren’t currently jailbroken, can’t currently jailbreak, and are holding out on iOS & iPadOS 15 with the hope of jailbreaking in the future.
Are you excited to see what materializes from Amar’s kernel exploit proof-of-concept now that we’ve witnessed what it’s capable of? Be sure to let us know in the comments section down below.