
Here’s how to protect yourself from the EFAIL vulnerability in Apple Mail on both iOS and macOS. These temporary fixes come after the new vulnerability was discovered that allows hackers to derive decrypted plaintext from encrypted emails. For the attack to work, the third party must be in possession of your encrypted S/MIME or PGP emails.
Although Apple’s likely to offer a fix to this vulnerability sooner rather than later, there are things you can do now to make your email more secure.
The Electronic Frontier Foundation (EFF) was the first to discover this vulnerability.
Method 1
As previously mentioned, the first method involves removing the GPGTools/GPGMail encryption plugin from Apple Mail on macOS. To do so:
- Quit Apple Mail (Mail > Quit Mail in the menu bar)
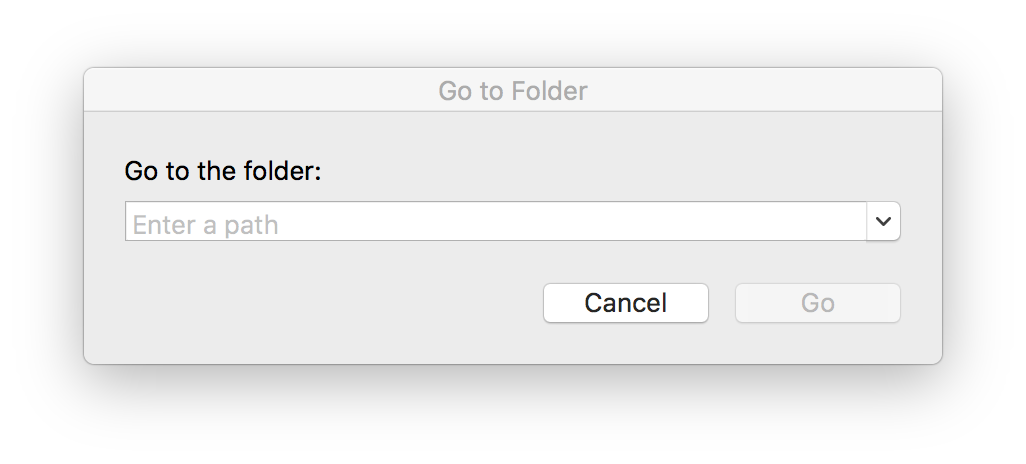
- Click on your desktop and in the Finder menu bar, select Go > Go to Folder
- From here, type /Library/Mail/Bundles, then click Go
- Delete the GPGMail.mailbundle file by dragging it to the Mac trash in your dock or by right-clicking it and selecting Move to Trash in the drop-down menu
- If you don’t see GPGMail.mailbundle file, return to the previous step and type ~/Library/Mail/Bundles in the Go to Folder dialog
- Please note: You may need to type the administrator password for your Mac before deleting the file
Method 2
On iOS, you’ll need to just change the setting called “Load Remote Images.” To do so:
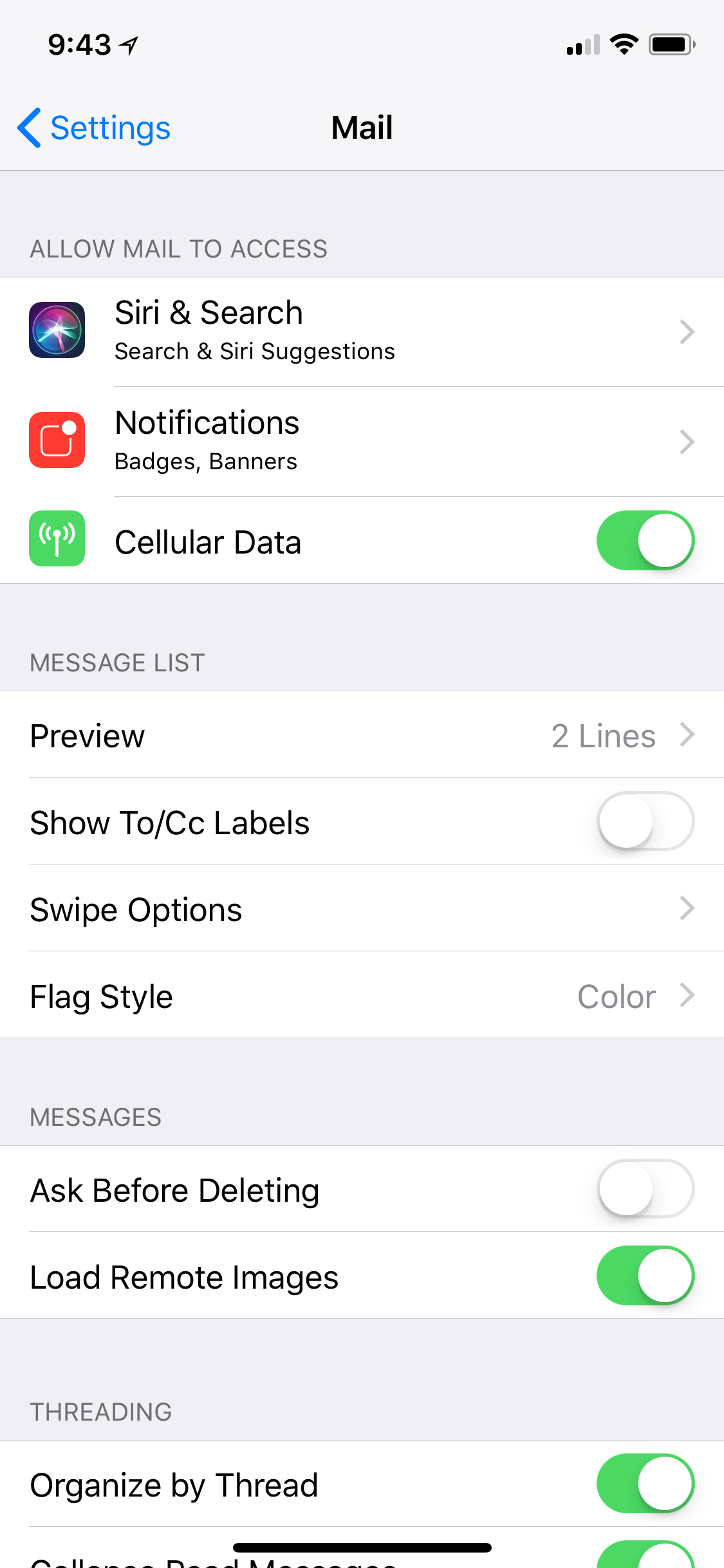
- Go into the Settings app and select Mail
- Under Message, toggle Load Remote Images to the off position
- It’s that simple
Removing EFAIL vulnerability — final words
Keep in mind this vulnerability is most likely to occur in an environment that relies on S/MIME and PGP encrypted email communications to talk in private. The average Apple Mail user is almost certainly not using any of these tools.
You can read the technical details about the vulnerability from the EFF website.
We’ll let you know when Apple pushes out a fix for this issue. In the meantime, let us know what you think about this newly discovered vulnerability in Apple Mail and other email clients by leaving a comment below.