A fix for a new kind of exploit recently discovered in the Bash command shell used in multiple versions of Unix is underway, Apple confirmed Friday, adding that the “vast majority” of Mac users are unaffected because OS X is “safe by default” from the so-called ‘Shell Shock’ attacks.
“The vast majority of OS X users are not at risk to recently reported Bash vulnerabilities,” an Apple spokesperson said in a statement quoted by The Verge.
The vulnerability was documented and publicized Thursday by security researchers at RedHat and gained prominences after security expert Robert Graham called it “as big as the Heartbleed bug,” referring to a nasty vulnerability discovered earlier in the year in the OpenSSL software commonly used by nearly two-thirds of servers powering the Internet.
Bash is the popular Unix command shell and because Apple’s OS X is based on the strong foundation of UNIX, the utility is included in OS X.
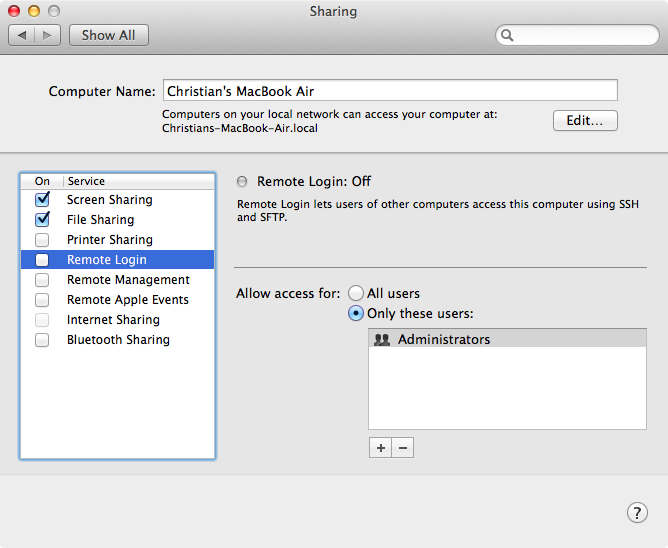
While acknowledging that many flavors of Unix, OS X included, have a weakness that could allow unauthorized users to remotely gain control of vulnerable systems, Apple did underscore that OS X systems are “safe by default” and ”not exposed” to remote exploits of Bash “unless users configure advanced Unix services”.
To check if your Mac computer is vulnerable, paste the following into the Terminal window (you can find the Terminal app inside your Mac’s Applications folder):
env x='() { :;}; echo vulnerable' bash -c 'echo hello'
If the output says ‘vulnerable’, your Mac is exploitable.
If it says:
bash: warning: x: ignoring function definition attempt
bash: error importing function definition for `x’
hello
then you’re safe.
Several variants of Linux already have patches available, and a fix for OS X is underway, Apple said.
“We are working to quickly provide a software update for our advanced Unix users,” said the Cupertino firm.
The impatient types who know their way around Terminal can fix the problem themselves by compiling a new, patched Bash version, as outlined in a detailed tutorial in this Stack Exchange thread.