Over the weekend, we told you about an ambitious project called kernel file descriptor (or kfd for short) that would help jailbreak developers achieve kernel read and write privileges on firmware up to and including iOS & iPadOS 16.5.

Over the weekend, we told you about an ambitious project called kernel file descriptor (or kfd for short) that would help jailbreak developers achieve kernel read and write privileges on firmware up to and including iOS & iPadOS 16.5.

The wait continues for an iOS & iPadOS 15 jailbreak, but fortunately, Odyssey Team lead developer CoolStar took to Twitter late last night with a particularly thought-provoking Tweet that may raise hope levels for those waiting.

If learning more about jailbreaking interests you, especially the methodology involved in achieving one, then we’ve got some good news for you.

Nearing around two weeks after security researcher @b1n4r1b01 published a working kernel exploit for iOS & iPadOS 15.0-15.1.1 based on Brightiup’s CVE-2021-30955 kernel bug, another respected hacker now appears to be surfacing with an exploit release.
Hacker and security researcher @pattern_F_ issued a stern reminder to avid jailbreakers Tuesday afternoon about the potential dangers of a jaw-dropping security flaw discovered in iOS & iPadOS 14.0-14.3.
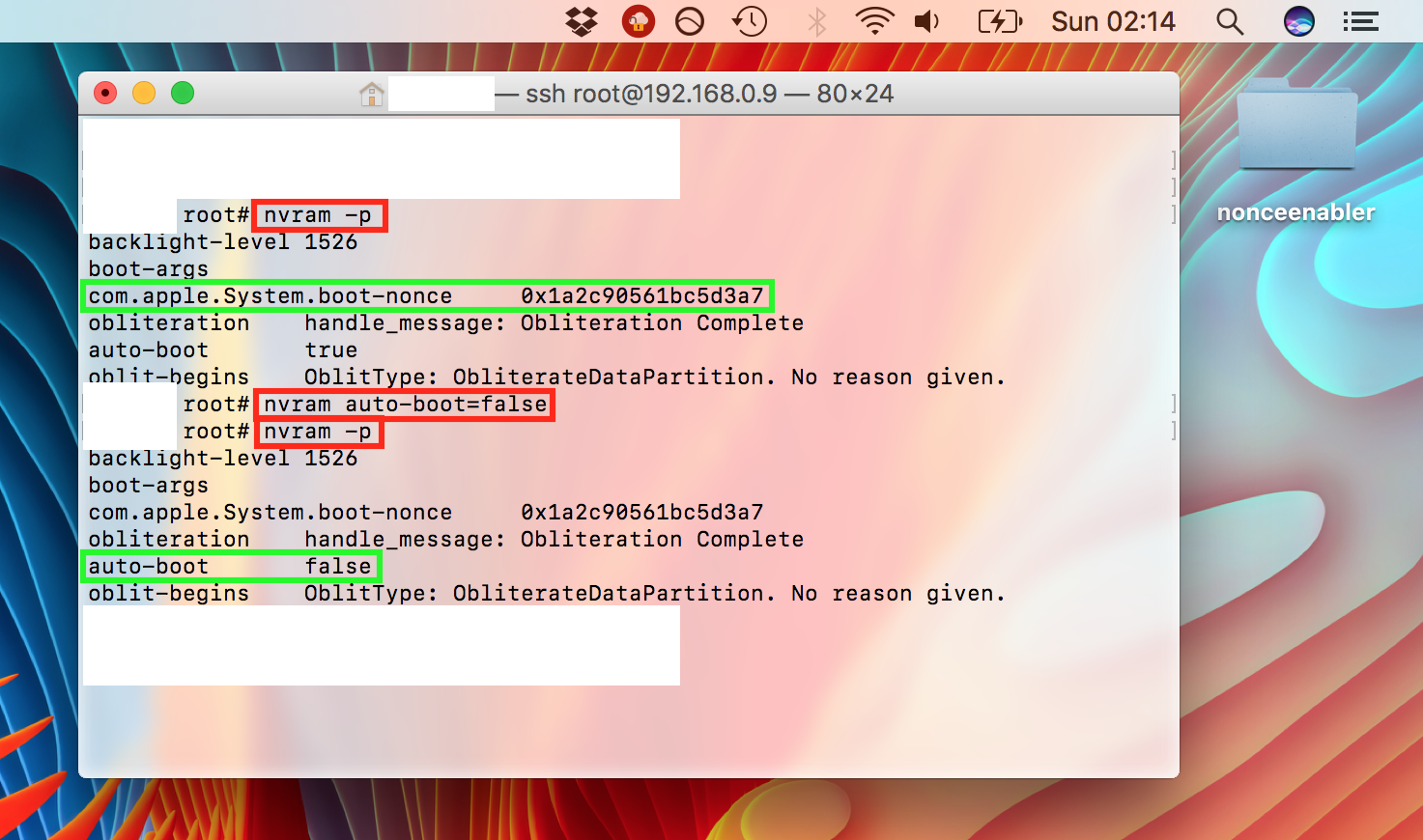
First off, this guide is only necessary for 64-bit devices which are currently jailbroken on old firmwares, such as iOS 9 and some versions of iOS 10. The jailbreaks for those firmwares did not always include a way to set a generator for use with futurerestore, and nonceEnabler provides that ability. Nearly all newer jailbreaks provide their own simpler ways of setting a generator, and they do not need to use nonceEnabler, nor this guide. If your device is not currently jailbroken on an old firmware such as the ones mentioned in this guide, and/or has its own method of setting a generator, refer instead to our main futurerestore guides.
Renowned hacker and unc0ver lead developer Pwn20wnd has issued a new revision to the unc0ver v3.0.0 pre-release Friday morning; beta 28 is now the latest version available for public testing purposes.
In a Tweet shared just minutes ago by Pwn20wnd, we learn that unc0ver v3.0.0 beta 28 adds provisions for timstar’s iOS 12-centric v3ntex exploit; on the other hand, the tool only supports the iPad Air 2 and iPad mini 4 with the v3ntex exploit at the time of this writing. Support for more devices will come later:

Just under two weeks ago, hacking guru tihmstar released v1ntex, a voucher_swap-like exploit for 4K devices that contributed to iOS 11.4.x support in both the Electra and unc0ver jailbreaks. But just this morning, tihmstar released another exploit dubbed v3ntex, which allegedly supports iOS 12 devices.
Tihmstar shared his exciting announcement via Twitter Monday morning with proof of the exploit, adding that he only tested his v3ntex exploit on an iPhone 6 running iOS 12.1.2 and that it could likely still do with some improvements:

It was only yesterday that hacker and unc0ver lead developer Pwn20wnd added official support for tihmstar’s v1ntex exploit to the unc0ver v3.0.0 pre-release, but another revision issued just this morning delivers some important v1ntex-related bug fixes and refinements.
Citing the changelog from Pwn20wnd’s official GitHub repository, the 21st beta of the unc0ver v3.0.0 pre-release sports the following changes:
In what appears to be a pleasant surprise for the jailbreak community on Friday, hacker and unc0ver lead developer Pwn20wnd revised the unc0ver v3.0.0 pre-release to its 20th beta with official support for tihmstar’s voucher_swap-like v1ntex exploit.
Pwn20wnd shared the news via Twitter just this afternoon, sharing the usual links to the official download page and to the /r/jailbreak sub-Reddit:

Just a couple of days ago, security researcher Brandon Azad released his voucher_swap exploit for 16K devices (A9[X], A10[X], A11[X]), but the exploit didn’t support 4K devices (A7[X], A8[X]), resulting in some devices being unsupported by the recent updates to the Electra and unc0ver jailbreaks.
On a more positive note, hacking guru tihmstar seems to have a solution. Thursday morning, he Tweeted his version of the voucher_swap exploit, subtly named v1ntex. Astonishingly, the exploit supports 4K devices, whereas Brandon Azad’s exploit did not:
Just over two weeks ago, it became known that hacking guru tihmstar was tinkering with a tfp0 exploit for iOS 11.4-11.4.1 devices of the A10 and earlier variety. But not long after finishing it, he opted not to release it, citing that ‘something cool’ would be coming instead.
Curiously, tihmstar appears to have undergone a change of heart on Tuesday after releasing his exploit to the public, a move that could reinforce existing iOS 11-centric jailbreak tools such as Electra and unc0ver: