iOS 17.6 and iPadOS 17.6 patch as many as 30 vulnerabilities and zero-day exploits, so install the update on your iPhone and iPad to get the latest security protections.
Install iOS 17.6 to protect your iPhone against these 30 vulnerabilities


iOS 17.6 and iPadOS 17.6 patch as many as 30 vulnerabilities and zero-day exploits, so install the update on your iPhone and iPad to get the latest security protections.

According to the iOS 16.5.1 release notes, the latest updates fix security issues in the kernel and WebKit that have been actively exploited in the wild.
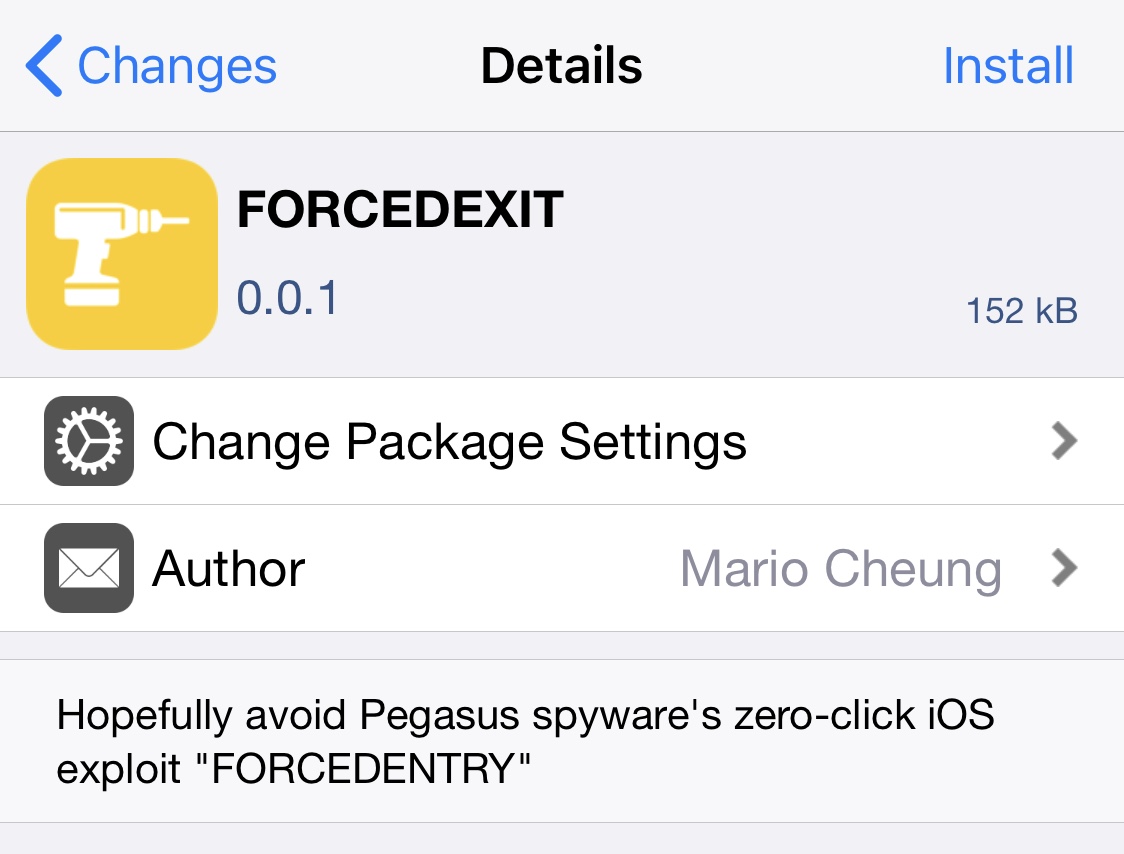
Last week, Apple released iOS & iPadOS 14.8 to the general public with important security patches for a zero-click exploit that could have resulted in arbitrary code execution.

Timely security patches and seamless iOS software updates are among the chief reasons for many Android customers to switch to an iPhone.

As reported recently on iDB, Luca Todesco has decided to solve the certification problems which have plagued the most recent Pangu release for 9.2-9.3.3, by making public a web-based tool for re-activating the jailbreak.
After doing some testing and research it seemed appropriate for a more in-depth discussion of the tool, along with a walkthrough, in order to address some of the more technical questions surrounding this latest development in the jailbreaking scene.
The latest Pokémon GO update blocks jailbreakers from using the game in a move to crack down on third-party apps and tweaks that harvest data for Pokémon tracking and cheating.
Of course, not all jailbreakers cheat in Pokémon GO, so it's a pretty harsh assumption on their part, so in this piece, we'll discuss how you can run Pokémon GO on your jailbroken device even if you have the latest update.
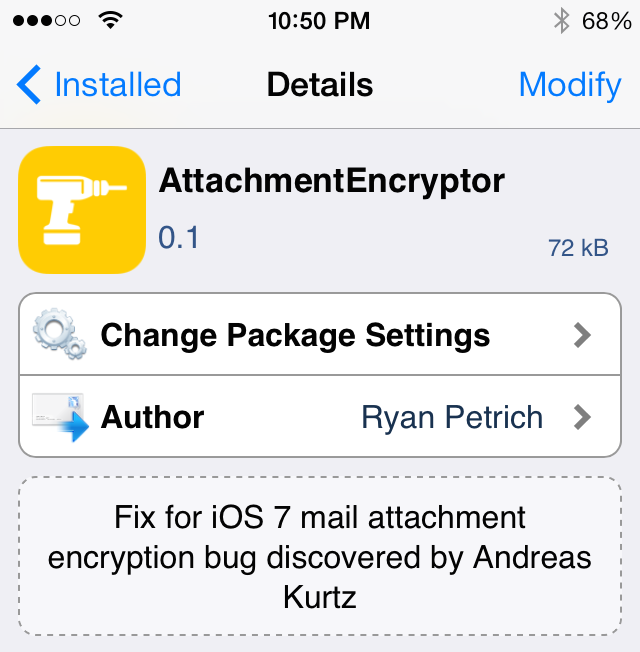
Earlier this week, word got out that there's a gap in security in iOS. Security researcher Andreas Kurtz discovered that all versions of iOS 7.1, and at least iOS 7.0.4, don't encrypt email attachments.
Kurtz says that he has informed Apple of the bug, and they are working on a fix, but there's no word when it will be available. Fortunately, the jailbreak community has a much faster response time...
Filippo Bigarella has released a new jailbreak tweak this weekend called GlyphPatch. The utility patches the recently exposed DoS exploit which targets Safari's WebKit engine and causes apps to crash when rendering a malicious sequence of characters.
The bug, which was made public last week, affects users on both iOS and Mac and can be triggered through a few different surfaces: SMS, iMessage, the web, and network SSID. But jailbroken iOS users can protect themselves from it with this new tweak...
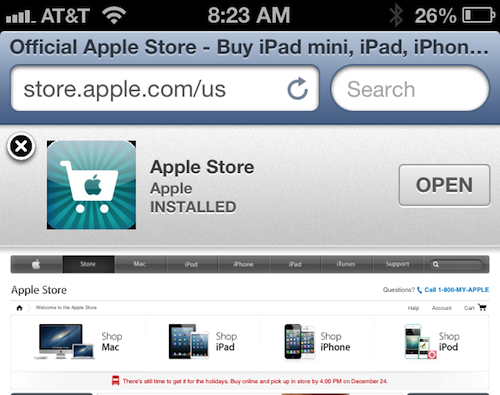
Last month, we reported that a JavaScript bug had been discovered involving Smart App Banners. Apple added the feature in iOS 6 as a way to help developers promote their apps and provide users with a direct link to download them.
Well as it turned out, these Smart Banners were enabling JavaScript in the iOS Settings app without user consent or knowledge. And this was considered to be a fairly serious security threat. But it looks like Apple has fixed it in iOS 6.1...

In case you didn't know, satellite provider DirecTV recently updated its iPad app with the ability to stream live TV. Customers can stream a selection of channels on the iPad when connected to the same home network as the DirecTV HD DVR.
Like Time Warner, DirecTV has blocked streaming access to users on jailbroken iDevices. A jailbreak patch has been released to fix the block...
If you may recall, with the release of the long awaited JailbreakMe 3.0 for iOS 4.3.3, literally 10 days later Apple patched the clever PDF exploit in iOS 4.3.4. The security exploit could be triggered by viewing a maliciously crafted PDF file which may lead to an unexpected application termination or arbitrary code execution.
While the main reason Apple patched the exploit was to stop the use of JailbreakMe, it can also be a security concern. A few days later, Apple released another iOS software update, iOS 4.3.5. Apple released this update to patch the certificate validation vulnerability.
If you love customizing your iDevice to the fullest, you've probably already jailbroken, unless you didn't update by accident or purchase your iDevice after Apple stopped signing iOS 4.3.3. Unfortunately, while not updating to the latest software may preserve your jailbreak, you may also be at risk from the same vulnerability...

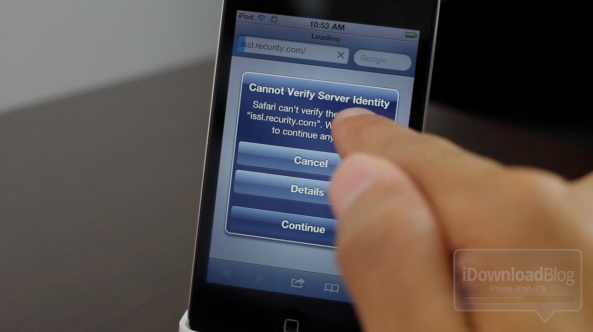
JailbreakMe 3.0 has garnered some serious attention over the last 48 hours. The last report we heard was that the site had been visited over a million times, and the PDF exploit had been downloaded over 500,000 times.
The exploit must have also grabbed the attention of Germany's Information Security team, because the group just issued a country-wide warning for all iOS products. The Mobile Safari vulnerability exposed by Comex in his new jailbreak tool has really made some folks nervous...