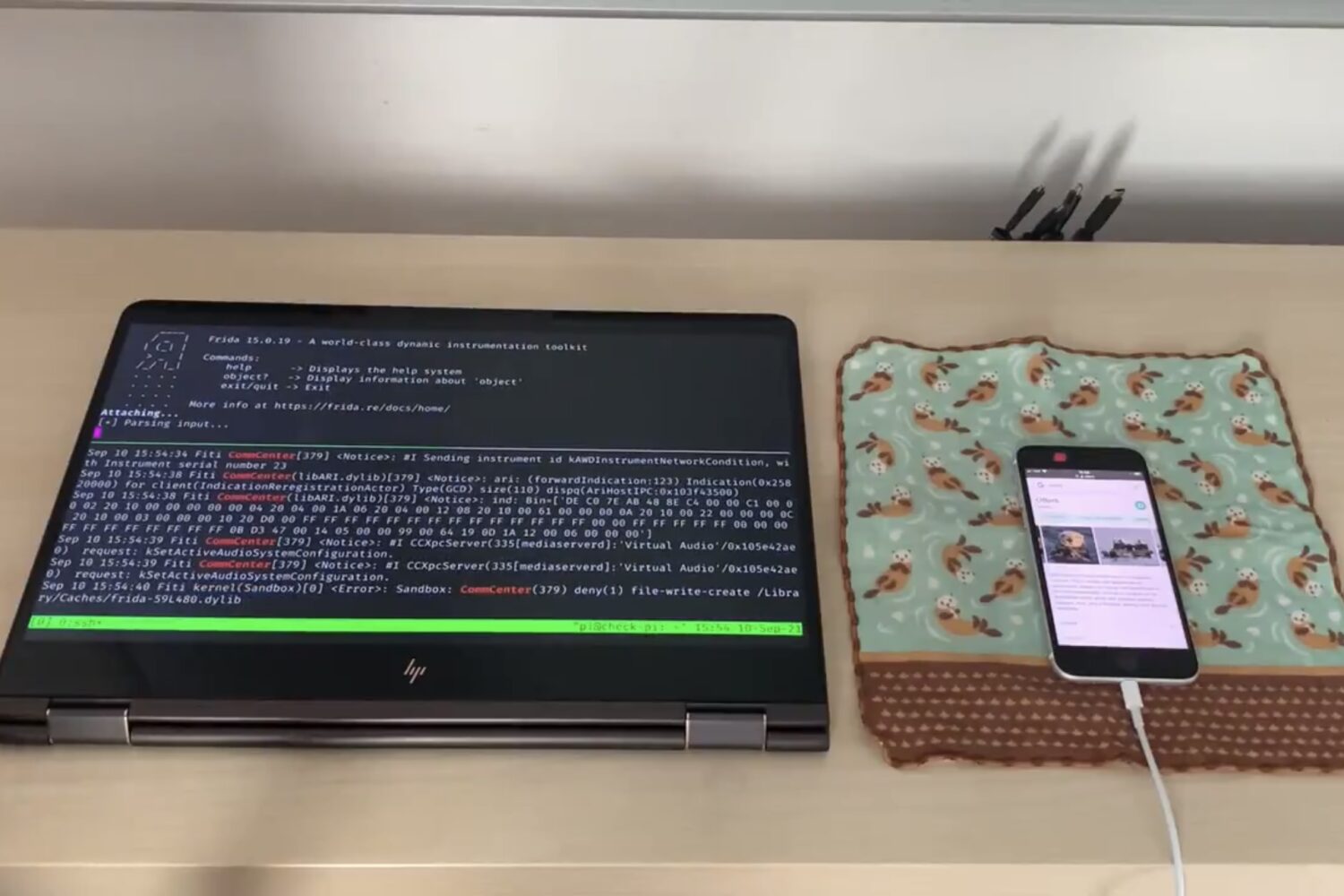
If you haven’t heard about the Fugu14 untether and how the unc0ver jailbreak now supports it, then you’d be inviting the age-old question of whether you live under a rock or not. And now that the latest version of AltStore (v1.4.8) can bundle the Fugu14 untether with the latest version of the semi-untethered unc0ver jailbreak tool, lots of people with compatible devices are jumping onboard.
What you need to know about unc0ver and the Fugu14 untether