Jailbreakers with access to an A7-A11 device pretty much have it made thanks to the hardware exploit-based checkra1n jailbreak that can’t be patched by Apple in a software update. Those handling newer devices, such as the A12 and A13 varieties, instead depend on infrequently released tfp0 exploits. These seem to surface sporadically with no rhyme or reason, and they can unfortunately be patched by Apple’s software updates.
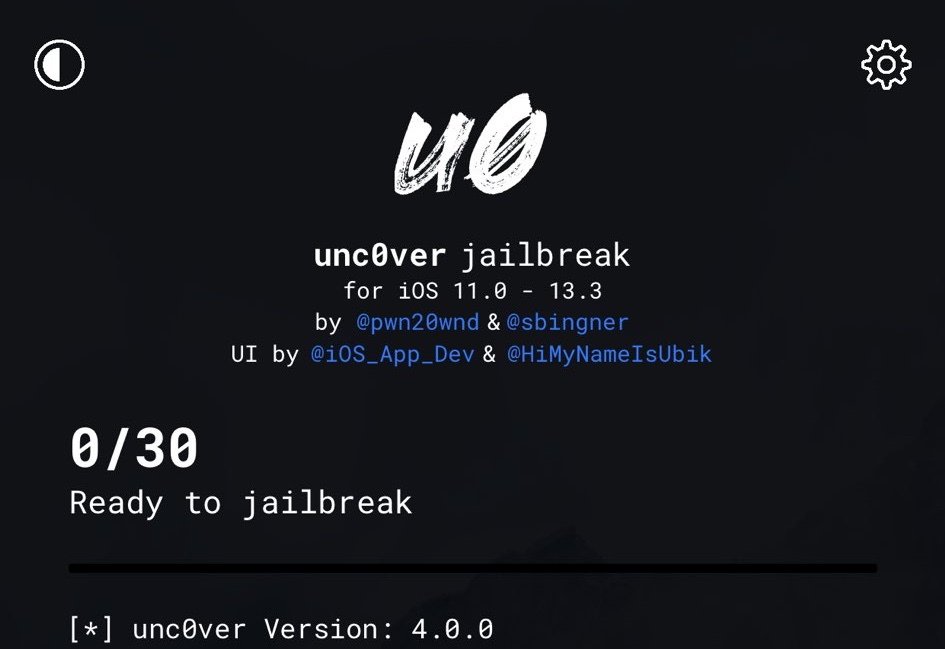
On a more positive note, it does appear that a skilled security researcher going by the Twitter handle @ProteasWang has achieved tfp0 on an A13-equipped handset running iOS 13.4.1. This is currently the latest version of iOS available from Apple, and with that in mind, the news has particularly exciting implications for jailbreaks such as unc0ver and the to-be-released Chimera13 tool.