Apple’s Find My network is a solid feature for folks within the company’s ecosystem. It’s a great way to track devices. And, apparently, it can also be used to send messages and other data.
Fabian Bräunlein is a security researcher who has published a blog post detailing how the Find My network can be exploited to send messages and other data. Bräunlein was able to work out a way to turn the Find My network into a data transfer mechanism, using the local devices to upload that data.
Apple’s network is designed to utilize the active iOS base to serve as individual nodes that can transfer location data. The blog post is pretty in-depth, but it starts with an AirTag. According to the researcher, it’s possible to emulate the way the AirTag not only connects to the Find My network and also broadcast its location. Interestingly, messages sent on the Find My network are encrypted, too, because the location data (which is encrypted) is replaced with the message.
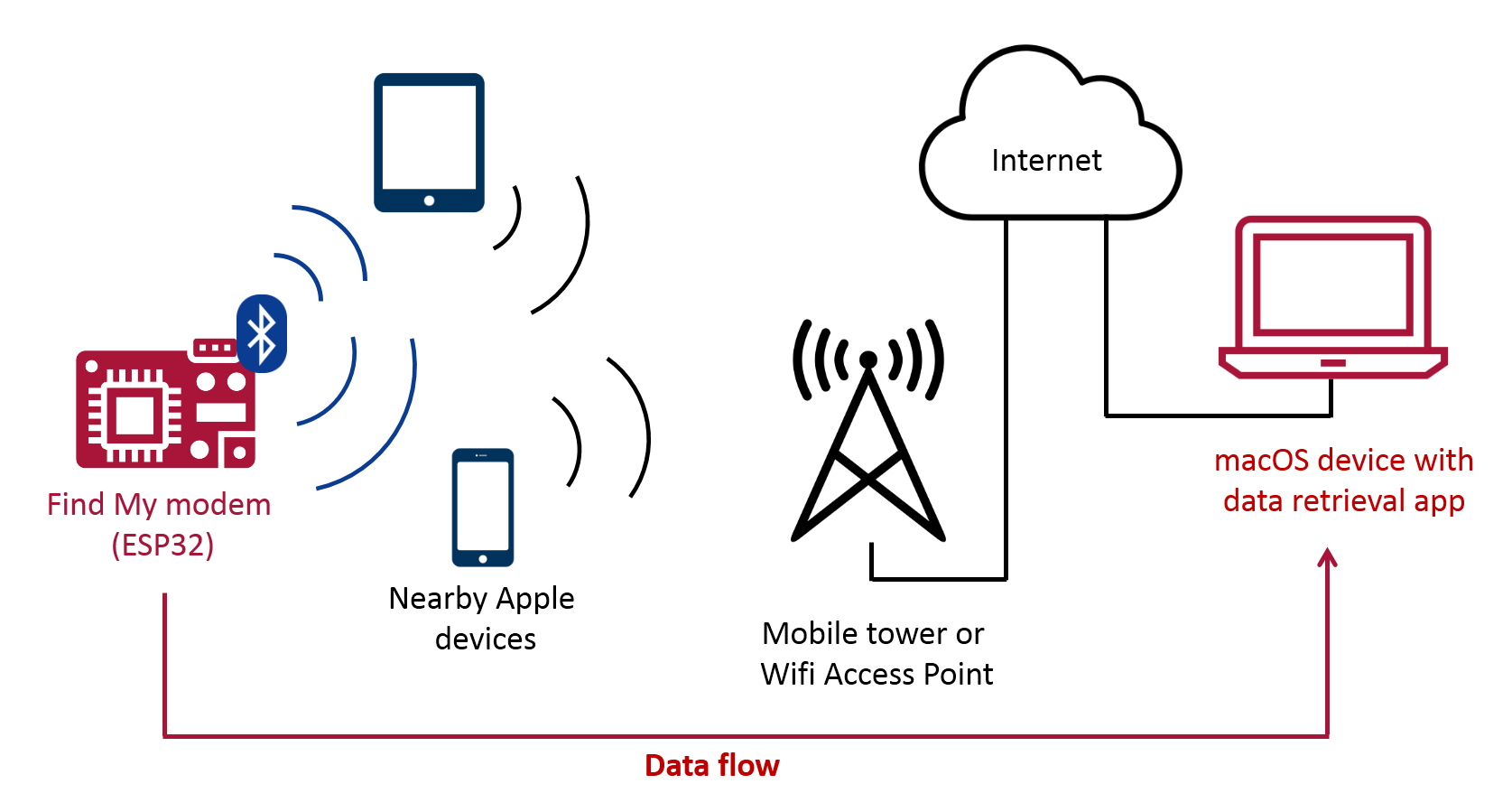
Bräunlein included a practical demonstration of how it all works on the blog post as well.
- When paring an AirTag with an Apple Device, an Elliptic Curve key pair is generated and the public key is pushed to the AirTag (and a shared secret to generate rolling public keys)
- Every 2 seconds, the AirTag sends a Bluetooth Low Energy broadcast with the public key as content (changes every 15 minute deterministically using the previously shared secret)
- Nearby iPhones, Macbooks, etc. recognize the Find My broadcast, retrieve their current location, encrypt the location with the broadcasted public key (using ECIES) and upload the encrypted location report
- During device search, the paired Owner Device generates the list of the rolling public keys that the AirTag would have used in the last days and queries an Apple service for their SHA256 hashes. The Apple backend returns the encrypted location reports for the requested key ids
- The Owner Device decrypts the location reports and shows an approximate location
At this point, this just looks like a cool discovery. At the time of publication any security implications aren’t known. This is technically an exploit, so it’s possible it could be used for nefarious uses in the future. It could also be something Apple develops into features for the end user at some point in the future, too.
Check out the full blog post if you’ve got the time, and you’re interested to see how it all breaks down.