
There is a new ransomware being distributed across the Mac ecosystem, and it’s being spread through pirated Mac apps.
According to the report shared today by Malwarebytes, the new ransomware is called “EvilQuest”, and the primary distribution model is through pirated Mac apps. The latest security threat was initially discovered in a pirated version of the Mac app Little Snitch, which was being shared in a Russian forum.
Installing that pirated version of the app made it possible for the installer to get the full version of the app itself, but then the installation also included an additional executable file labeled “patch”. This file was stored within the Users/Shared directory, including a post-install script that infected the machine where the app was installed.
Examining this installer revealed that it would install what turned out to be the legitimate Little Snitch installer and uninstaller apps, as well as an executable file named “patch”, into the
/Users/Shared/directory.The installer also contained a postinstall script—a shell script that is executed after the installation process is completed. It is normal for this type of installer to contain preinstall and/or postinstall scripts, for preparation and cleanup, but in this case the script was used to load the malware and then launch the legitimate Little Snitch installer.
That installation script then moves “patch” to a separate, new location and renames it “CrashReporter”. This is a legitimate macOS process, which means it is basically hidden within the Activity Monitor. Once that process is done, it installs itself in several locations within the Mac’s software.
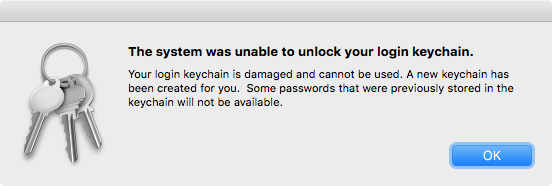
Once complete, the ransomware will then encrypt data files and settings, which is a similar process to how Keychain works — another legitimate piece of software on the Mac. When attempting to access the iCloud Keychain, an error will be prompted to the user, which you can see pictured just above. In addition to that, the dock started messing up, along with other apps, and the Finder also started to act up as well.
Apparently the attackers behind this new ransomware are asking $50 for access to the ransomed system. However, Malwarebytes says the ransomware works relatively poorly. It does also include a key logger, though, which can log keystrokes inputted across the system and in websites visited.
Malwarebytes does have some suggestions just in case the ransomware does end up on your system (which you can avoid by not installing pirated Mac apps, for one):
If you get infected with this malware, you’ll want to get rid of it as quickly as possible. Malwarebytes for Mac will detect this malware as Ransom.OSX.EvilQuest and remove it.
If your files get encrypted, we’re not sure how dire a situation that is. It depends on the encryption and how the keys are handled. It’s possible that further research could lead to a method for decrypting files, and it’s also possible that won’t happen.
The best way of avoiding the consequences of ransomware is to maintain a good set of backups. Keep at least two backup copies of all important data, and at least one should not be kept attached to your Mac at all times. (Ransomware may try to encrypt or damage backups on connected drives.)
While this appears to not be a widespread issue at the moment, it’s always good to be made aware of these situations as they are discovered. Go check out the full Malwarebytes blog post if you want to dig into the real nitty gritty of this latest ransomware attempt.