A potentially serious bug has been discovered by developer Lemi Orhan Ergin that allows anyone to gain root access to your machine by attempting to login with the username “root” and leaving the password blank. The vulnerability can easily be replicated, but fortunately, there is a simple workaround to fix the problem on your Mac until Apple releases a patch.
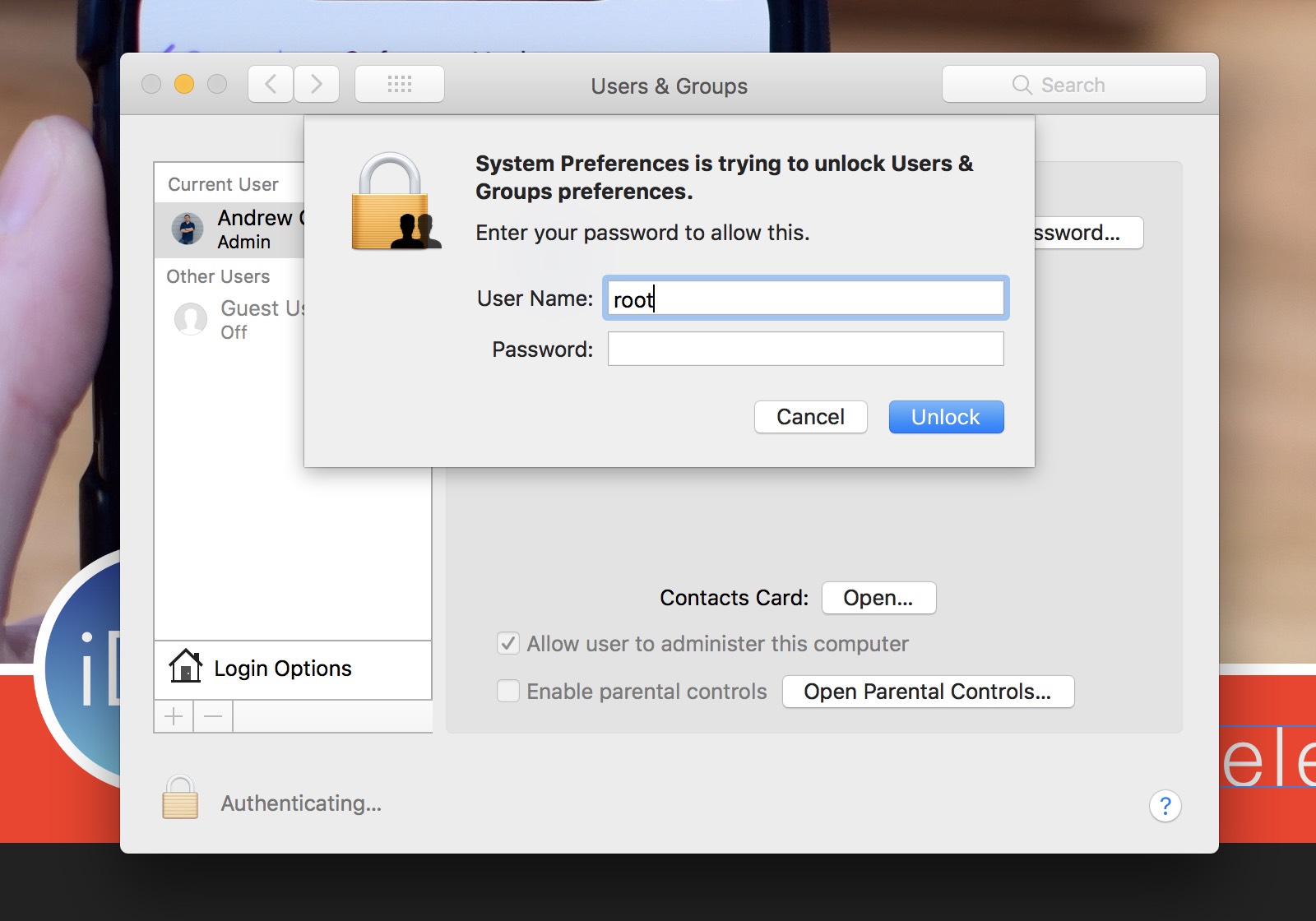
You can try replicating the issue yourself:
- Open System Preferences.
- Choose Users & Groups in the lower left corner.
- Click the
in the lower left corner.
- In the login box, type “root” as the username.
- Move the mouse to the Password field, click there, but leave it blank.
- Now click unlock.
This should now allow you access to the admin account, even the ability to update the password.
Ergin reported the issue on Twitter, and received a quick reply from Apple Support.
Let's take a closer look at what's happening together. Send us a DM that includes your Mac model along with your macOS version. We'll meet up with you there. https://t.co/GDrqU22YpT
— Apple Support (@AppleSupport) November 28, 2017
The bug is currently in the latest public version of macOS High Sierra, 10.13.1 as well as the macOS 10.13.2 beta. Considering the seriousness of this bug, Apple will undoubtedly release a fix as soon as possible.
Until then, there is a workaround you can enable if you’d like to be sure your Mac is locked down.
To protect yourself, just enable a root account with a password. You can check out Apple’s support document on how to do so, but we’ve copied the instructions here for brevity.
Enable Root user
- From the Apple menu (), select System Preferences, then click Users & Groups
- Click on the
in the lower left corner, then input your admin credentials
- Click on Login Options on the left side
- Then select “Join”, then choose Open Directory Utility
- Click the
that appears, and then enter your administrator credentials
- In the menu bar of the Directory Utility, click Edit, then Enable Root User, then choose a password for the root user
Apple told the press that a fix is in the works.
Have you been able to replicate this bug on your machine? Let us know in the comments.