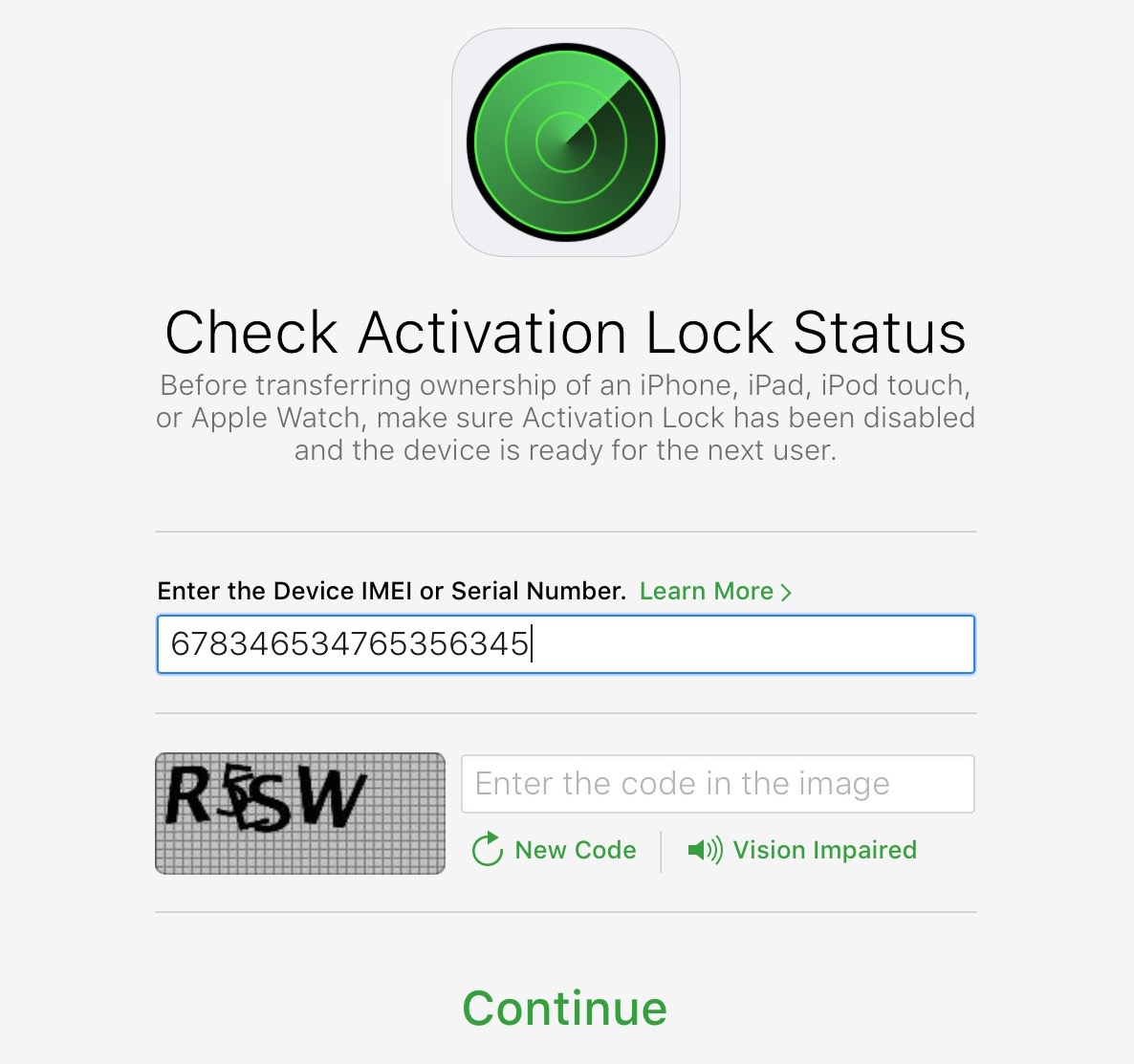
As we reported, Apple recently took down its tremendously useful Activation Lock webpage for reasons unknown. The theft-deterrent tool allowed legitimate iOS device owners and just about anyone else to check the status of the Activation Lock feature by entering a serial number. Apple provided no explanation for the removal, but all checks point to it being a precautionary measure meant to prevent hacks relying on stolen serial numbers, as a reader pointed out in comments.
Apple likely took down iCloud Activation Lock to stop hacks relying on stolen serial numbers