Every so often, it helps to take a step back and examine the way things are being done. This applies to our day-to-day routine, or perhaps our workout regimen. I've also found that it applies to software.
iOS is no exception to this. Here is a software product that has been through vast changes since its creation. A good majority of the changes have been for the better, and iOS 8, which is mere weeks away, promises to bring more awesome goodies to the table.
But, from time to time, it pays to look at the way things are being done. We have to ask ourselves, "Is this truly the best way?"
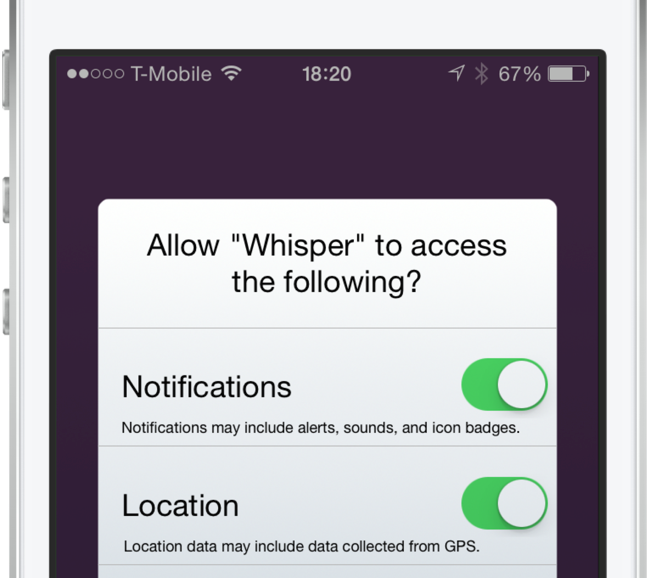
I feel that we've reached that fork in the road when it comes to the way iOS handles permission requests for apps. As more features are added to our devices, more permissions are required for apps that wish to use these features. It's gotten to the point that some apps require you to go through a whole checklist of permissions before you can even begin using the app.
The permission handling in iOS has become a frustrating affair. Not only do the numerous pop-up alerts annoy me, but it irritates me even more when I accidentally decline a permission because of speeding through the app setup process.
As discussed on today's episode of Let's Talk iOS, I'm convinced that there's a better way to handle permissions in iOS. There's a less intrusive, less frustrating way to handle requests for access to the various features on your device. Check out our video inside for an explanation of the problem, and a demonstration of the solution.