If you’ve been paying any attention to the jailbreak community lately, then you’d be pretty hard-pressed to have never heard of palera1n. It’s a pretty big deal these days.

Palera1n is effectively the only publicly available jailbreak tool capable of pwning iOS or iPadOS 15.2 and later, but with the major caveat that it only supports these firmware versions on A9-A11 chip-equipped handsets.
While that’s a massive deal-breaker for so many prospective jailbreakers given that the age the aforementioned devices is starting to show, that won’t ever change because palera1n utilizes the checkm8 hardware-based bootrom exploit to achieve a jailbreak.
So what is checkm8? We introduced it to our readers when it was announced in September of 2019, and it’s been at the heart of modern jailbreaks ever since.
Since checkm8 is a hardware-based bootrom exploit, it’s physically present in all A5-A11 chips and can’t be fixed by Apple with a software update. The only way Apple could patch the exploit would be to recall every A5-A11 device and install updated chips in them, but that would be too costly of a venture for the company to take on, and even if they did, many people would keep their vulnerable devices for the sake of jailbreaking.
This is the reason why the same exploit used to make checkra1n back in the iOS 12 days was so easily subsequently updated to support iOS & iPadOS 13 and 14. While the checkra1n team doesn’t actively maintain their tool anymore, palera1n sort of came in to take its place for iOS & iPadOS 15 and 16.
But one thing that really seems to stand out to us in the responses to Tweets by the palera1n team are the endless stream of questions asking when the tool will add support for devices with A12 chips and newer, and it goes without saying that the answer to that question is a very firm never.
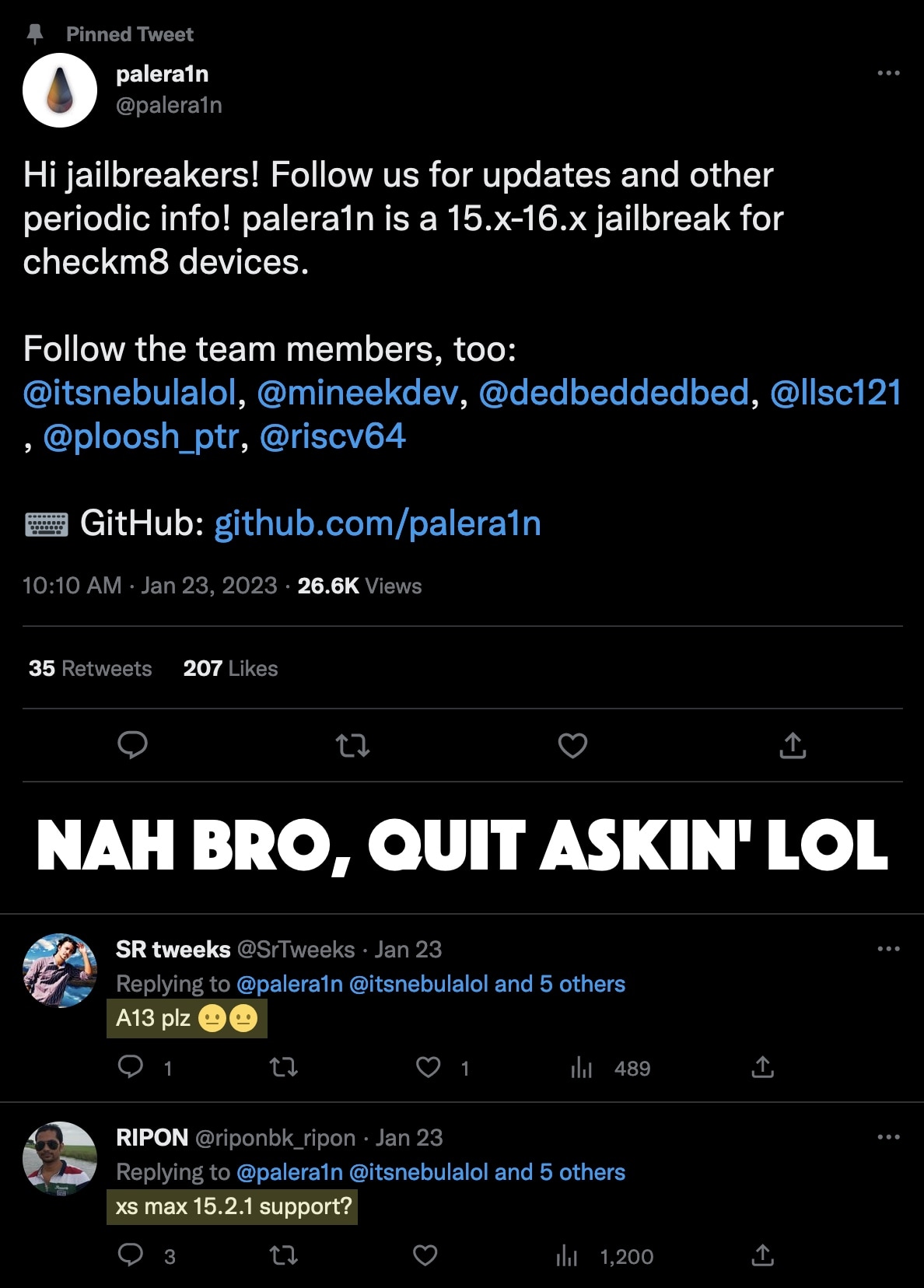
And those questions aren’t unique to Twitter – you’ll find them on Reddit too, unfortunately.
You see, the iPhone XR and newer come equipped with A12 and newer chips, which aren’t vulnerable to the checkm8 bootrom exploit. Sadly, the exploit is completely fixed in these devices, so there’s no way to add support. Doing so would require an entirely new bootrom exploit for newer Apple chips, and those are extremely rare — we generally only see a new bootrom exploit announced once every decade or so thus far, so they’re definitely not growing on trees like some of those other exploits that are easy for Apple to patch.
Instead, achieving a jailbreak on newer hardware requires not only a kernel exploit that supports every anticipated firmware version, but also various techniques to bypass security mitigations found in Apple’s latest hardware and software, including but not limited to a pointer authentication codes (PAC) bypass and a page protection layer (PPL) bypass, which must also support every anticipated firmware version. So you can see where this becomes resource-intensive very quickly.
Unfortunately, Apple’s latest hardware and software-based security mitigations have made it ever more challenging to achieve a jailbreak on newer devices running anything newer than iOS or iPadOS 15.2, so unless someone dedicates the time necessary and burns valuable techniques like those discussed above to make it all possible, a jailbreak for newer devices isn’t likely to materialize without a magic silver bullet, such as another bootrom exploit.
The excessive work associated with making jailbreaks and the low-reward that seems to come with Apple releasing a software update to patch it just days or weeks later has all but drained hacker motivation and morale. This, paired with the problems discussed above, explains why we haven’t seen an all-device-encompassing jailbreak tool for iOS & iPadOS 15.2 and later. Instead, we only have palera1n, which supports only older devices that few people regularly use as their daily driver anymore. Those on pre-iOS & iPadOS 15.2 firmware have other options, such as XinaA15.
Given these challenges, it will be interesting to see where the community goes from here.