In mid-October, hacker Justin Sherman took to Twitter to announce that he would soon publish a write-up detailing the likes of a kernel-level exploit for iOS & iPadOS 14.7 and below.
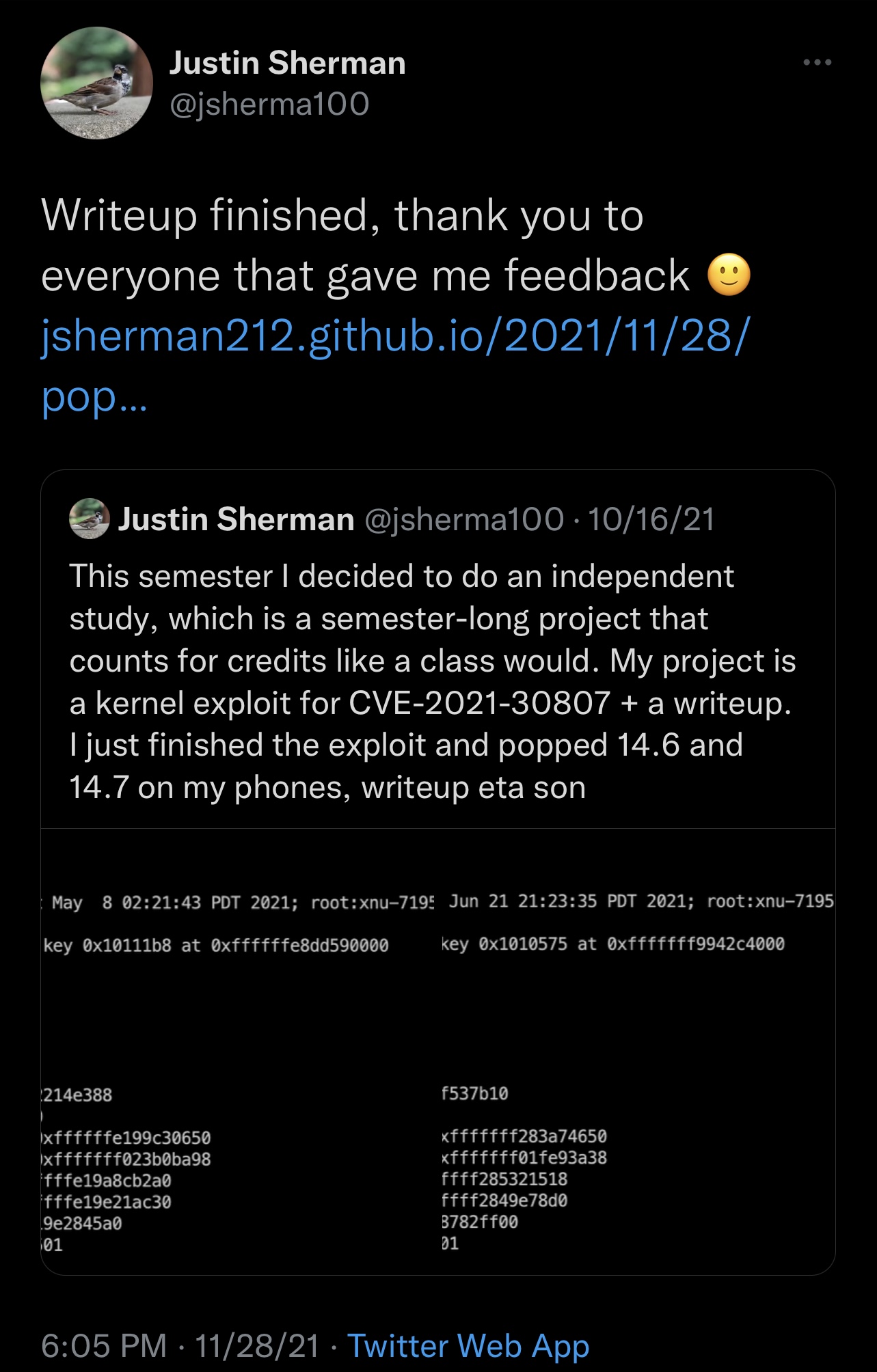
That promise was realized over the weekend after Sherman published a detailed blog about his purported kernel exploit along with instructions discussing how to test it out on his GitHub page.
Anytime we see the words “kernel” and “exploit” in the same sentence, it’s often challenging to hold back the excitement and barrage of questions regarding whether it can be used for jailbreaking. In this case, however, it does seem reasonably unlikely.
Citing the blog post, Sherman’s exploit is based on an IOMobileFrameBuffer bug (A.K.A. CVE-2021-30807), and while it originally seemed like it would only be viable on arm64 devices (A11 and older), some tweaking to the exploitation method demonstrates that it could be viable on arm64e devices (A12 and newer).
Toward the bottom of the blog post, Sherman claims that it would be possible to set up arbitrary kernel read/write APIs, and that it would be possible to begin jailbreaking from there. If that wasn’t fascinating enough, Sherman added that arm64e (A12 and newer) handsets should be viable because the exploit doesn’t attack PAC-affected data structures.
One of the major downsides to this exploit appears to be that it requires individual offsets for every device and firmware combination, and this could make trying to utilize it somewhat tedious. Further, it would likely need to be chained with another exploit to be used for jailbreaking because of entitlement concerns.
The GitHub page goes into detail about how users could acquire said offsets, but the process is extensive and would need to be performed for each individual device and firmware combination. Theoretically, Corellium’s powerful virtualization tools could help in cases where these devices and firmware versions weren’t available.
Albeit unlikely that Sherman’s exploit will be used for jailbreaking, especially given the current timeline comprised of Fugu14’s availability and the existence of a possible 0-day vulnerability for iOS & iPadOS 15, it’s still fascinating for anyone who might be interested in security research along with those who want and need to be reminded that even the latest version(s) of iOS and iPadOS are far from hack-proof (but we already knew that).
It remains to be seen what might become of Sherman’s kernel exploit, but it will certainly be interesting to find out.