
Jailbreakers haven’t even been able to blink their eyes lately without some sort of news regarding exploit or jailbreak tool updates, and as it would seem, there’s no sign that this will be slowing down anytime soon.
While the bulk of this news has dealt with adding support for newer firmware versions by way of updated and more efficient exploits, hacker and rootless JB 3.0 developer Jake James shook things up a bit this morning when he released updated versions of his Sock Port and Sock Port 2 tfp0 exploits with support for 64-bit devices running iOS 10.0-10.3.3:
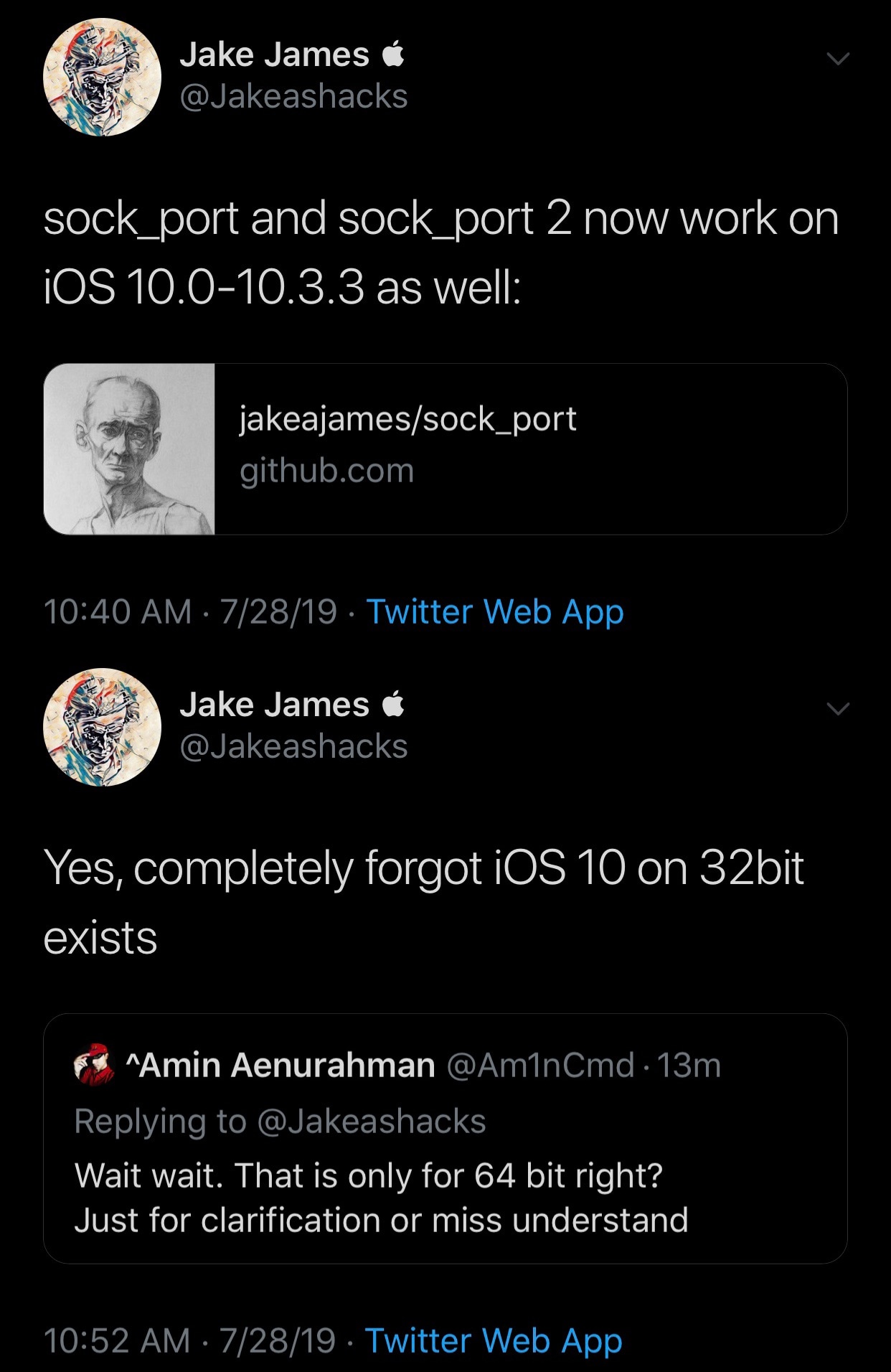
From what we can gather, these exploits will not work with 32-bit devices such as the iPhone 5 and older, but it’s still great news because it extends an olive branch to iOS 10 users who might be looking forward to a new jailbreak apart from Luca Todesco’s Yalu tool.
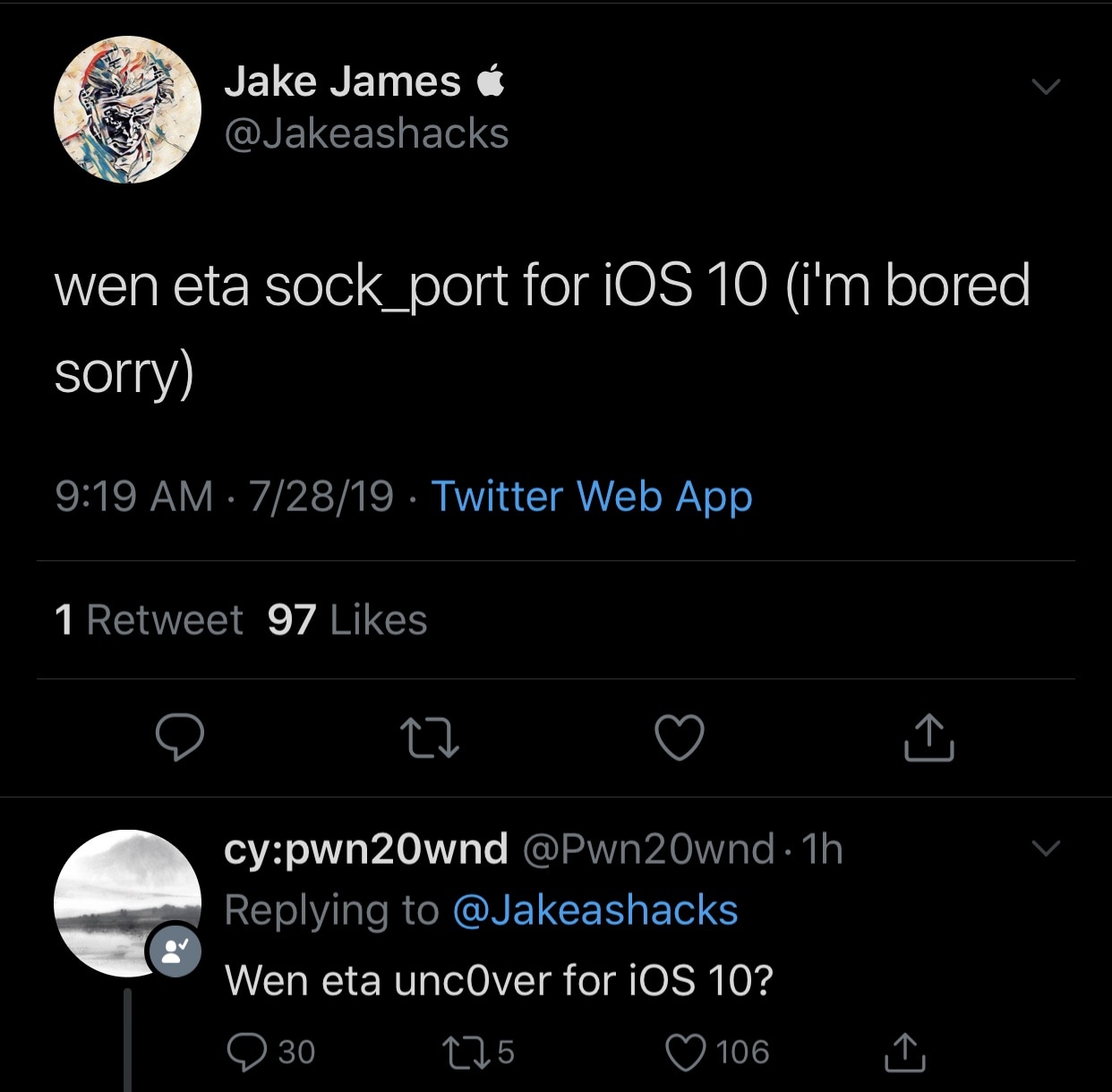
Worthy of note, unc0ver lead developer Pwn20wnd expressed interest in the exploit shortly after James began teasing it. While this isn’t a promise, it is indicative of the idea that unc0ver could one day pick up iOS 10 support, transforming it into an even more universal jailbreak tool than it is already:
James has published his updated exploits on GitHub with a full write-up PDF available here. Below are the release notes:
iOS 10.0-12.2 tfp0 for all devices (in theory).
Some info:
- Uses socket bug by Ned Williamson
- Uses some things by Ian Beer, machswap, SockPuppet
- The rest of the code is licensed under GPL, unless given permission explicitly to distribute closed-source (the unc0ver team, pwn20wnd and sbingner, have this permission)
Write-up: https://raw.githubusercontent.com/jakeajames/sock_port/master/sock_port.pdf
Thanks to Pwn20wnd and GeoSn0w & users for helping with testing on multiple devices (and Corellium).
Would you like to see unc0ver pick up iOS 10 support with James’ new Sock Port exploit, or are you only looking forward to jailbreaking future firmware versions? Let us know in the comments section below.