For security purposes, booting Linux or any other non-Apple operating system except Windows 10 is currently impossible on Apple hardware featuring the company’s in-house designed Apple T2 chip unless you adjust your Secure Boot settings.
The T2 chip ensures your Mac is in a known trustworthy state when it’s booted by verifying the integrity of every step of the startup process to ensure no code has been tampered with. Due to the way this system security has been implemented in hardware, macOS Mojave currently won’t let you boot Linux. And to boot Windows, you must first enable Boot Camp.
Apple did an exception for Windows 10 if you install it through Boot Camp. To ensure secure booting of Windows, your Mac’s UEFI firmware includes a copy of the Microsoft Windows Production CA 2011 certificate which is used to authenticate Microsoft bootloaders.
But the fact remains that it’s currently not possible to boot third-party operating systems other than Windows 10 on any Mac computer featuring the T2 chip.
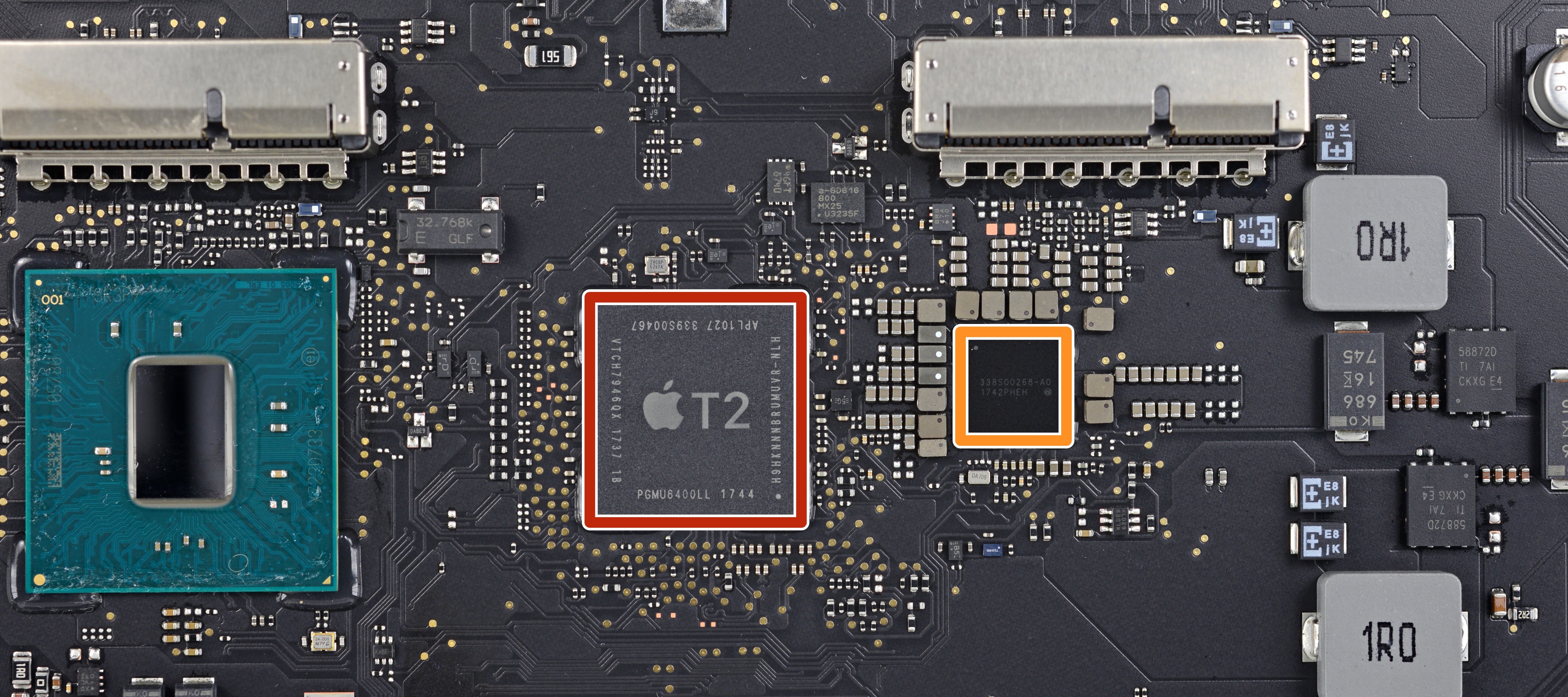
According to the developers of Macs Fan Control software, that’s because the T2 chip makes it impossible to see the internal drive. A possible workaround calls for installing Linux on an external drive, but don’t get your hopes high—the Macs Fan Control developers have tried this for Windows and it worked but the internal flash drive was not visible.
People have complained about this on Reddit. The solution, as noted in this Reddit thread, is pretty obvious—disabling Secure Boot altogether—but it’s not something for the faint-hearted as you’ll need to manually locate and load missing drivers for the SSD controller.
Apple itself notes that it might be possible to disable the Secure Boot security in full when booting to the Startup Security Utility in the macOS Recovery mode. As a result, this may allow Linux to load on your T2 Mac but without any boot security.
On the other hand, don’t treat this as a foregone conclusion because disabling the Secure Boot startup features may not make any difference for the case in question, as per other reports.
The following Mac computers use the T2 chip:
- 2018 MacBook Pro
- 2018 MacBook Air
- 2018 Mac mini
- iMac Pro
All T2-equipped Macs supporting Secure Boot only trust content signed by Apple.
Apple’s T2 Chip Security Overview states that other operating systems cannot be used with Macs using Secure Boot as there’s currently no trust provided for the the Microsoft Corporation UEFI CA 2011 which would allow verification of code signed by Microsoft partners.
“This UEFI CA is commonly used to verify the authenticity of bootloaders for other operating systems such as Linux variants,” notes the document. Because support for secure boot of Windows isn’t enabled by default, it must be turned on manually via Boot Camp Assistant.
TUTORIAL: How to adjust Secure Boot settings on Mac
When you set up your Mac for a Windows installation using Boot Camp Assistant, the computer is reconfigured to trust Microsoft first-party signed code during boot.
Here’s what happens during secure boot:
After Boot Camp Assistant completes, if the system fails to pass the Apple first-party trust evaluation during secure boot, the UEFI firmware attempts to evaluate the trust of the object according to UEFI Secure Boot formatting. If this succeeds, it proceeds and boots Windows. If not, it enters macOS Recovery and informs the user of the trust evaluation failure.
Enabling the No Security option in Startup Security Utility on your Mac equipped with the Apple T2 chip completely disables secure boot evaluation on the main Intel processor and allows any operating system to boot your machine.
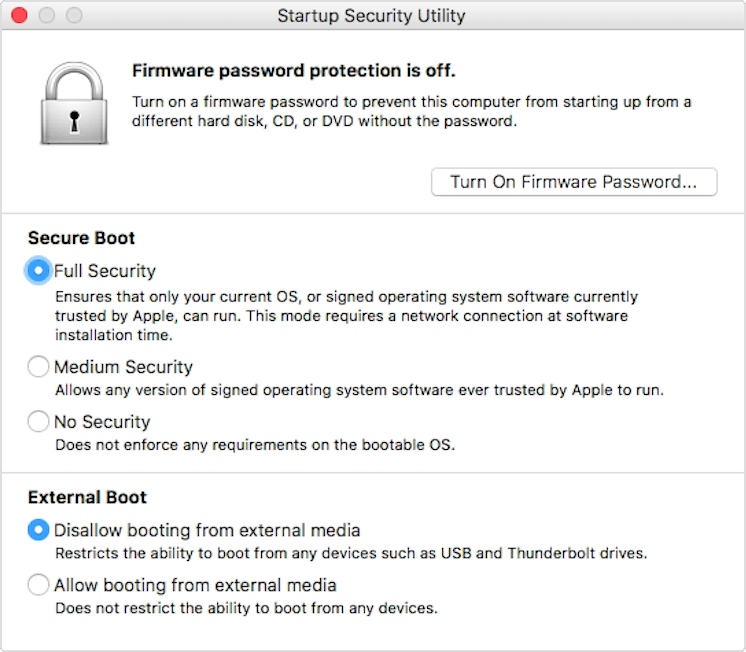
Disable or downgrade the secure boot functionality in Startup Security Utility
What’s your opinion about this situation?
Is Apple really locking things down, do you think? Has the T2 chip been purposefully designed to interfere with basic usability, like booting a third-party operating system, or is this just an unintended consequence of enforcing stronger security across the board?
Let us know by leaving a comment below.