Yesterday, news broke that the hacking group AntiSec published a million UDIDs from an alleged trove of twelve million device IDs claimed to have been stolen from a laptop belonging to an FBI agent. Even though the hackers had removed some of the identifiable information from the list, your UDID might be exposed out in the wild, along with 999,999 other IDs posted on the web.
And why would you want to know if your UDID is out there for everyone to see? Good question. Your UDID uniquely identifies your device and expert hackers could use it to glean all sorts of information from other data associated with your UDID.
Yeah, it’s a privacy catastrophe, one that might potentially even lead to identity theft. Perhaps even more important than that, wouldn’t you like to know if your device is on the FBI’s watch list?
The tool to check if your UDID has been compromised has been put together by The Next Web and is made available here.
Just type in your UDID into the search field and they will run it against the database and spit out the results.
Of course, the publication promises not to store your UDID though we obviously cannot vouch for this.
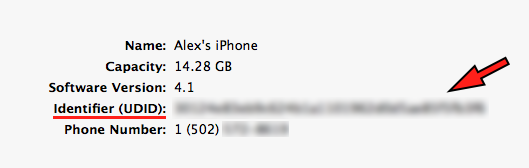
Don’t know what your UDID is?
Just hit the serial number entry in the device information pane in desktop iTunes or head here for a brief tutorial.
As you know, UDID, or “Unique Device Identifier” is just what the name says, a serial number unique to your device. Developers have been using UDIDs to identify users both across different apps and on a per-app basis for the purpose of simplifying and personalizing user experience.
Due to privacy issues related to apps sending UDIDs to ad companies without the user’s permission, Apple began clamping down on sites that sell UDID activations and rejecting apps that use UDIDs.
Presumably, a set of new tracking tools fore developers is likely in the works.
As for the FBI breach, what I’m way more concerned about is how the heck has the FBI gotten hold of twelve million UDIDs in the first place.
More importantly, why?
Data obtained by hacking into a Dell Vostro notebook used by Supervisor Special Agent Christopher K. Stangl from FBI Regional Cyber Action Team and New York FBI Office Evidence Response Team contains a wealth of information which also includes user names, name of device, type of device, Apple Push Notification Service tokens, zip codes, cellphone numbers, addresses and what not.
What business does Uncle Sam have storing sensitive personal data belonging to twelve million individual devices?
9to5Mac offers an interesting answer, that the FBI lifted these UDIDs in an unrelated raid last year which saw Instapaper creator Marco Arment’s server being stolen as well.
Arment on its part tweeted that the breach “didn’t involve the disks being taken, and I had nowhere near 12 million user records”. He also confessed that “Instapaper did log UDIDs with user accounts in the past, but has never transmitted or logged any of those other fields”.
Of course, it wouldn’t be an evening news topic without a joke attached to it (via David Chartier).
Here’s a new FBI FAQ:
Q: How do I find out if my UDID has be—
A: Shut up and pay no attention to the man behind the curtain.
What do you think?
Also, we’d love to hear from those of you who checked if their UDID has been compromised.
Is your device on the list?
If so, are you spooked now?