You’ve no doubt heard about a scandalous security oversight which has enabled hackers to break into former Gizmodo writer Mat Honan’s iCloud account to remotely wipe his MacBook Air, iPhone and iPad. He was easily hacked because Amazon used to publish the last four digit of users’ credit card on the web, which happens to be exactly what Apple’s customer support reps need to reset one’s Apple ID password over the phone (in addition to your name and billing address).
Reacting to the security outbreak, Amazon has stepped up its battle to prevent this kind of social engineering. The online retailer on Monday closed a privacy hole that could allow anyone to access to Amazon accounts over the phone using just a name, email address and mailing address.
Amazon also promised to no longer allow adding new credit cards to accounts over the phone. Today, Apple reportedly sent a notice to its support staff, temporarily halting Apple ID password resets over the phone…
Wired tested Apple’s new policy by calling Apple Support and attempting to reset the password on an iCloud account. Apple Support wouldn’t abide to Wired’s request.Authors Nathan Olivarez-Giles and Mat Honan (the victim of the hack) explain:
Our Apple source’s information was corroborated by an Apple customer service representative, who told us Apple was halting all AppleID password resets by phone. The AppleCare representative shared that detail while Wired was attempting to replicate Honan’s hackers’ exploitation of Apple’s system for the second day.
The attempt failed, and the representative said that the company was going through system-wide “maintenance updates” that prevented anyone from resetting any passwords over the phone. The rep said we should try calling back after about 24 hours, and directed us to iforgot.apple.com to change AppleID passwords ourselves on the web instead.
“Right now, our system does not allow us to reset passwords,” the Apple rep told Wired. “I don’t know why.”
Just a few days ago, Apple Support told the reporters they could reset passwords over the phone if they were able to supply a serial number for a device linked to the AppleID in question.
Journalist Mat Honan has detailed his terrible identity theft experience, confessing that security and privacy oversights on his part had led to hackers easily compromising his entire digital life.
It’s a chilling admission of guilt and if there’s one thing we could all learn from it, it’s that none of this would have happened had he enabled a two-step authentication on his Google account, which was daisy-chained to his three-letter Twitter handle (which was the primary target of the attack).
First rule is to never daisy-chain social accounts through the same email address. Instead, use different email address for the key services such as Facebook and Twitter.
Moreover, use different recovery email addresses for your Gmail, Apple ID, Microsoft or Yahoo accounts. This way, if someone breaks into one of your main email accounts, they won’t be able to reset passwords across all your social media accounts and wreak havoc.
Most importantly, enable two-step authentication on your Google Account and don’t forget to create application-specific passwords for apps and service that don’t support two-step authentication yet (for example, Mail and Gmail apps on your iPhone or iPad, Gtalk clients, apps that access your Google Contacts and so forth).
Having read Honan’c account of the unfortunate events yesterday, I immediately went through the trouble of setting up a two-step authentication on my Google Account.
Google’s Search Quality team employee Matt Cutts and his blog post made that decision a no-brainer.
[tube]zMabEyrtPRg[/tube]
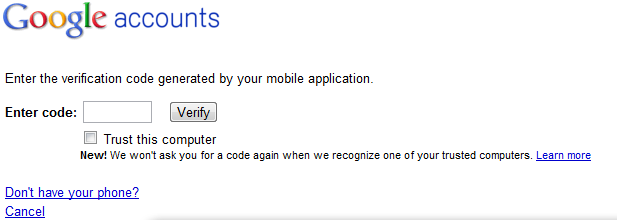
Two-step authentication secures your account by requiring both your Google Account password and a special code generated in the cloud and sent to your phone as a text message, voicemail or available through Google’s Authenticator app for Android and iOS.
Cutts took the opportunity to dispel some myths concerning two-step authentication.
Myth #1: But what if my cell phone doesn’t have SMS/signal, or I’m in a foreign country?
Reality: You can install a standalone app called Google Authenticator (it’s also available in the App Store), so your cell phone doesn’t need a signal.Myth #2: Okay, but what about if my cell phone runs out of power, or my phone is stolen?
Reality: You can print out a small piece of paper with 10 one-time rescue codes and put that in your wallet. Use those one-time codes to log in even without your phone.Myth #3: Don’t I have to fiddle with an extra PIN every time I log in?
Reality: You can tell Google to trust your computer for 30 days and sometimes even longer.Myth #4: I heard two-factor authentication doesn’t work with POP and IMAP?
Reality: You can still use two-factor authentication even with POP and IMAP. You create a special “application-specific password” that your mail client can use instead of your regular password. You can revoke application-specific passwords at any time.
Too bad I was too lazy to consider doing it before.
I urge you to enable two-step authentication. It’s the least you can and should do protect yourself while making hackers’ job a whole lot harder.
Trust me, you don’t want to experience identity theft Honan’s been through.
But don’t take my word for it, just read Honan’s scary story over at Wired.